FCC shrugs at fake cell towers around the White House
It’s open season for cell tower spoofing in Washington.
Turns out, Ajit Pai was serious last year when he told lawmakers that the FCC didn't want anything to do with cybersecurity.
This past April the Associated Press reported "For the first time, the U.S. government has publicly acknowledged the existence in Washington of what appear to be rogue devices that foreign spies and criminals could be using to track individual cellphones and intercept calls and messages."
But when lawmakers formally asked Ajit Pai and the FCC to investigate the DHS confirmation of unauthorized cell towers in use, Pai gave them the brush off -- leading to a big WTF on the Energy & Commerce Democrats' official Twitter account.
Today's insane news brought to you by @AjitPaiFCC who JUST declined to investigate reports of foreign surveillance citing lack of evidence the SAME day @DHSgov confirms surveillance devices were detected near the White House. https://t.co/IJTfmBw5mT https://t.co/Wa7KmxlpaV
— Energy & Commerce Dems (@EnergyCommerce) June 1, 2018
When reached for comment, Brian Hart Director, Office of Media Relations Federal Communications Commission, disputed the tweet's choice of language and added a twist: That the FCC won't talk about this in public. Hart told Engadget via email:
One of the FCC's core missions is to ensure the reliability and resiliency of the nation's communications network and to promote public safety through communications. We continue to coordinate closely with our counterparts at DHS, DOJ, and the FBI on this issue, and we have not said that we have declined to investigate.
Rather, we have said that if we have particularized evidence that certain devices are being unlawfully used within the United States, we will investigate the matter alongside our federal partners and take all appropriate enforcement actions. But we cannot disclose publicly what evidence we may or may not have on this subject.
Unlike Hart's statement to Engadget, Pai's letter asserted "The Department of Homeland Security has taken the lead in assessing the potential threat from certain uses of cell-site simulators."
Maybe Pai wasn't up to speed on the fact that the DHS had already passed this problem off to other agencies, saying they aren't able to investigate it. And as we pointed out last year, the DHS is an organization with no regulatory authority over the commercial communications sector. This is what the FCC was created for.
The DHS initially found evidence of cell phone spying near the White House last year, right around the time Pai was shrugging off cybersecurity. It discovered several fake cell phone towers (also called ISMI catchers, or Stingrays) intercepting calls and ran an 11-month investigation, emerging with serious concerns. This was all explained last month in a letter from the DHS to Sen. Ron Wyden, D-Oregon.
Wyden, in turn, kind of flipped his lid. As well he should. Fake cell towers trick mobile phones into thinking they're connecting with legitimate carriers. This can allow whoever is running the interceptor to do any number of things, including eavesdropping on calls, intercepting texts, grabbing photos, pinpointing physical location reportedly within three meters, or planting malware for more spying. They've been in use by government and law enforcement agencies for over a decade, sometimes in legally contestable grey area citizen-spying instances. In those instances, the fake cell towers are FCC-approved devices.
The DHS's acting National Protection and Programs Directorate head, Christopher Krebs, said in his letter that the false cell towers they found might come from legitimate sources. But he offered no attribution and instead kicked the can on down to other agencies to figure it out. "Krebs stated that NPPD doesn't have the law enforcement and counterintelligence authority to directly address the IMSI catcher threat," wrote Ars Technica, "and it had passed along the data collected to other agencies."
While the acting NPPD head pushed the problem off to other agencies, reporters at a local TV station in Washington D.C. piled into a van with security researchers and drove around the DC area for a few hours to see what they could find. Because of course hackers have been playing with these things for years, even publishing cell simulator DIY how-to guides.
NBC's I-Team identified what they believed to be around 40 locations where fake cell towers were in use "in high-profile areas like outside the Trump International Hotel on Pennsylvania Avenue and while driving across the 14th Street bridge into Crystal City."
The I-Team got picked up [by StingRay devices] twice off of International Drive, right near the Chinese and Israeli embassies, then got another two hits along Massachusetts Avenue near Romania and Turkey... The phones appeared to remain connected to a fake tower the longest, right near the Russian Embassy.
I-Team also wrote that their phones got "picked up twice while driving along K Street -- the corridor popular with lobbyists."
Anyway, in a move we don't usually expect to come from our elected representatives, Wyden rang the alarm. In a statement at the end of May, CNN reported, "Wyden demanded telephone companies and the Federal Communications Commission act to curtail the potential targeting."
"The news of a possible foreign Stingray near the White House is of particular concern giving reports that the President isn't even using a secure phone to protect his calls," Wyden said. "The cavalier attitude toward our national security appears to be coming from the top down. It is high time for the FCC and this administration to act immediately to protect American national security."
Indeed. Yet three ranking House members had already asked the FCC to investigate the potential operation of unsanctioned imitation cell towers in April. After all, it is the FCC that approves of these devices.
Maybe FCC head Ajit Pai was hoping they would just forget, or go away. After Wyden's demand, Pai finally responded to the other lawmakers -- not Wyden -- with probably the closest thing to a shrug emoji he could get away with: A rejection letter. Leading, of course, to everyone's collective WTF moment.

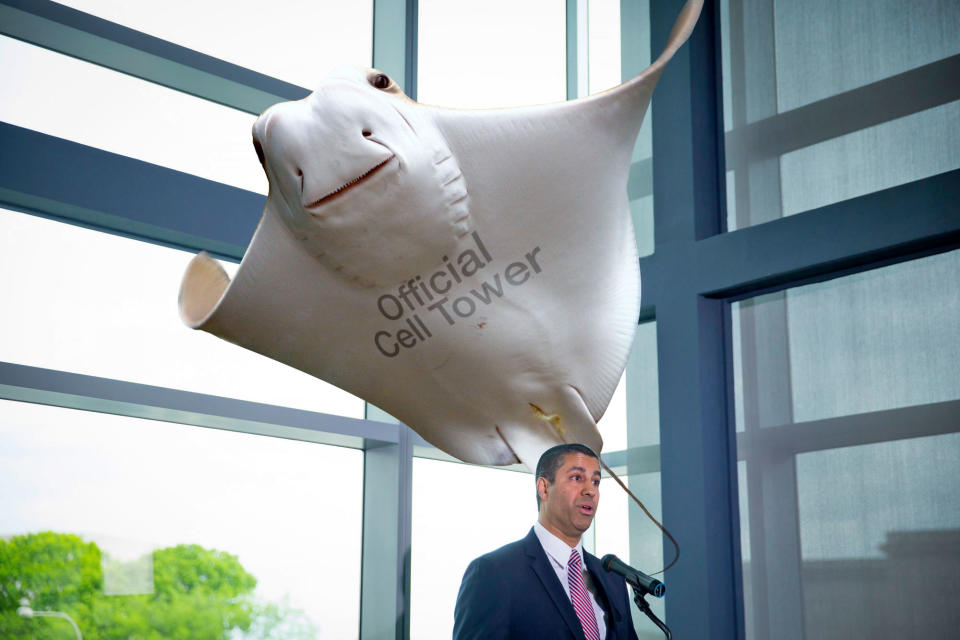
Everything, everything Ajit Pai has done since becoming head of the FCC -- but especially this situation -- calls into question who, exactly, he serves. Pai laughed his way through killing net neutrality. He ignored millions of fake comments on the FCC's own website (and refused to cooperate with investigations), some of which were stolen identities of government officials. There's so much more, but you get the picture.
Pai does not seem to listen. Worse, Pai does not appear to learn. Don't think for one second that anyone who wants to do cell tower spoofing around the White House has ignored this very public, ugly little scene. Pai's belligerence in publicly shoving this issue off toward the DHS, or whoever, will surely test whether or not the FCC's public no-maybe-yes game once press are involved was such a wise idea.