SmartphoneSecurity
Latest

Apple responds to Sen. Al Franken’s Face ID concerns in letter
Apple has responded to Senator Al Franken's concerns over the privacy implications of its Face ID feature, which is set to debut on the iPhone X next month. In his letter to Tim Cook, Franken asked about customer security, third-party access to data (including requests by law enforcement), and whether the tech could recognize a diverse set of faces.

Apple questioned about Face ID security by the US Senate
A lot of people quickly raised concerns about privacy and security the moment Apple revealed iPhone X and its Face ID feature. Edward Snowden, for instance, thinks it normalizes face scanning, "a tech certain to be abused." Now, US Senator Al Franken is pressing the tech titan for answers, penning a letter addressed to Apple chief Tim Cook with a list of questions concerning the technology's "eventual uses that may not be contemplated by" its customers.
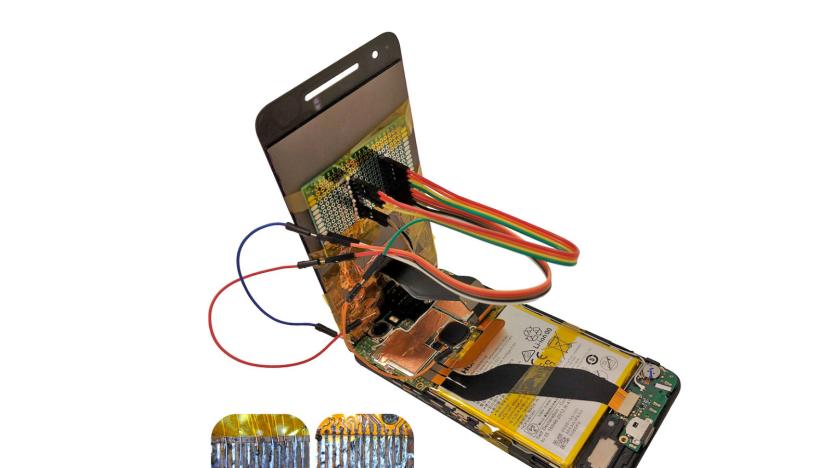
Replacement screens can be used to hijack your phone
A new study has shown that one of the most common fixes to a stock smartphone ailment can be used to steal your data, and compromise your device. In the newly published paper, researchers from Israel's Ben-Gurion University of the Negev reveal how a replacement screen can easily be altered to override your mobile. By embedding a malicious integrated chip within a third-party touchscreen, the research team were able to manipulate the communications system on a Huawei Nexus 6P and LG G Pad 7.0. This essentially allowed them to record keyboard inputs, snap pictures of the user and forward them via email, install apps, and direct the user to phishing websites. A second class of attack also saw them exploit vulnerabilities in the handset's operating system kernel.

Military hunting smartphone safety to hold off enemy bugs, spooks
Ah, smartphones -- the delightful little slates carry our contacts, our content -- even our cash, and they still fit right in our pockets. No surprise then, that a lost or stolen phone can be a minor disaster -- or a major security risk (just ask the President). Now that soldiers are packing them to send GPS coordinates or situational images in the field -- on top of using them at home -- DARPA has enlisted security company Invincea to fortify the devices. Its first effort, encrypting OS files and filling the memory of a lost phone with worthless data, has already been deployed to 3,000 troops in Afghanistan. Its next target is to cloister apps into virtual rooms within the OS, locking off access to sensitive parts of the phone like its GPS or contact lists. That would keep any nasty bits of malware from potentially gaining root privileges so soldiers can fight, and Facebook, without compromise.

Symantec report on mobile security concludes iOS and Android both vulnerable to attacks
In Symantec's bleak, dystopian world, it doesn't matter whether you choose Android or iOS -- you'll be making yourself vulnerable to attacks regardless of the camp you're in. The company just concluded a study pitting iOS's security against Android's -- an undertaking intended mainly for corporate IT staffs trying to figure out which devices they can safely issue to employees. (Curiously, despite the enterprise focus, you won't find a single comparison against BlackBerrys.) Although iOS won higher marks when it came to thwarting traditional malware and showed a more modest advantage in terms of data loss, data integrity, and service attacks, the two platforms proved equally adept at preventing web-based attacks -- and equally powerless to catch socially engineered ones. And when it came to implementing certain security measures, such as permissions-based controls, Android pulled ahead. Ultimately, Symantec (which sells mobile security software of its own, by the by) concluded that both "are still vulnerable to many existing categories of attacks," not least because both platforms allow users to sync with third-party apps or web services that may or may not be secure themselves. Indeed, Symantec's thesis is that Apple's App Store approval process helps explain its lead in the malware-blocking department. Also, in shocking news, Symantec adds that people using jailbroken are especially attractive targets for attackers, and that these devices are as vulnerable as computers. Don't say no one warned you. Head past the break for a press release with a summary of the findings or, if you're curious, hit the source link for a PDF version of the full report.



