The Open Source Initiative hopes public awareness is Heartbleed's 'silver lining'
Looking for a positive take to cut though all the negative press that Heartbleed has been getting? Then the Open Source Initiative (OSI) has one. The news has been full of stories about the exploit in OpenSSL (itself, an open-source project) that has caused a wave of panic around the internet. With much of the public not understanding what open-source is (it's complex, but mostly involves freedom to redistribute, and access to the code it's built on), and the fact that all this can be caused by a few lines of edited text, the integrity of open-source software has understandably come under scrutiny. We spoke with a representative from the OSI, and they gave us the positive spin we'd all been looking for.
"It's actually incredibly beneficial to the community that this has been raised as such an important issue. A lot of folk rely upon open-source software to get through their daily business lives, but they may not be aware that they are relying upon it," Leslie Hawthorn, a member of the OSI board, told us in an interview.
Hearbleed's made a large number of people aware of what open-source is for the first time.
Hearbleed's made a large number of people aware of what open-source is for the first time. The OSI hopes that this awareness will help users realize they can contribute by filing bug reports, ultimately leading to safer software. That will certainly help, but with the Heartbleed vulnerability having gone unnoticed for over two years, would it not have been subject to more than enough eyes to catch it sooner? The OSI concedes that this is more specific to the OpenSSL project itself. "It's been widely reported that the OpenSSL folks didn't have the same kinds of financial or human resource contributions that many open-source projects do," Hawthorn said.
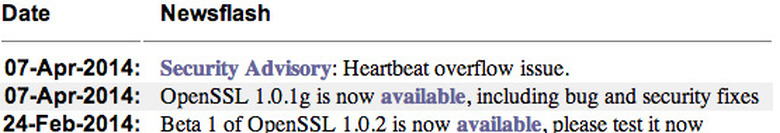
This is perhaps compounded by a general public relations issue between the devoted volunteers behind such projects, and the public that uses them. If you go to the OpenSSL project's webpage, for example, you won't see any big banners, blog posts about what to do or links to resources that the public can use to understand Heartbleed. Instead, there's just one discreet "newsflash" link pointing to a jargon-laden plain text file. Hawthorn admits that this is a typical "engineering" response. Essentially, it says: Here's what's wrong; go update your systems. Of course, for the vast majority of bugs, this likely works; after all, when was the last time you headed over to OpenSSL.org to check what's new? And this brings us back to the question of open versus closed (paid for) software.
"It's been widely reported that the OpenSSL folks didn't have the same kinds of financial or human resource contributions that many open-source projects do," Leslie Hawthorn says.
Hawthorn tells us the OSI thinks that there's a balance between the two models, but ultimately (as you'd expect) still sings the virtues of open source's "many eyes, [potentially] fewer resources" setup. Lars Eilebrecht — co-founder and member of the Apache Software Foundation that powers a great many of the internet's web servers — is more reserved about the situation. "Making something open source doesn't automatically make it more secure, but it provides the basis for better security. In addition, open-source projects typically have a very good turnaround time for critical security fixes, e.g., hours vs. days or weeks [for close-source projects]." Eilebrecht points to a recent case where Akamai (which sells a service that uses a custom version of OpenSSL) claimed it patched its software up to be secure.
Usually, this is something paying customers just have to trust. In the wake of Heartbleed, however, a researcher investigated Akamai's product after the update, and found it was actually still vulnerable. This kind of scrutiny is routine for both camps, but usually involving more eyes in the world of open-source software, its proponents argue. Eilebrecht sums the complex situation up neatly when he says, "Unfortunately, the OpenSSL bug has shown that a security bug can hide in plain sight for a very long time despite all the peer reviews of the OpenSSL code." He reminds us, "At the end, what matters is the number of qualified people peer-reviewing a piece of code to increase the confidence and trust that there are no security vulnerabilities."