'Icarus' machine can commandeer a drone mid-flight
The drone has to be using the DMSx signal protocol, however.
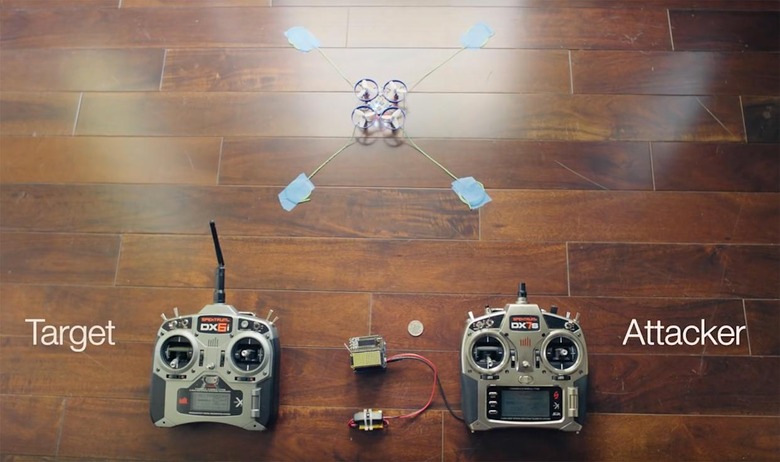
Security researcher Jonathan Andersson has shown it's possible to hijack drones that rely on the DSMx signal protocol. Unlike conventional jammers, which simply strip control from the user, this technique gives the attacker full flight capabilities. In an email to Ars Technica, Andersson explained that his new "Icarus" system is effective because it observes the underlying protocol and then brute forces the "secret" shared between the drone and controller. In addition, the setup relies on a "timing attack vulnerability," effectively pipping the original transmitter's signal to the drone, so that it accepts the attacker's inputs and rejects the owner.
Andersson presented his work at the PacSec security conference in Tokyo earlier this week. It's a timely reminder that drones, like any form of remote electronics, can be hacked with enough time and persistence. DSMx, however, isn't the only signal protocol. Many drone manufacturers, including DJI, use an alternative protocol which may or may not be vulnerable to a similar attack. Regardless, such methods should be of interest to the government and law enforcement — both to protect their own hardware, and stop the UAVs used by their adversaries. If you're intrigued too, you can check out Anderson's slides from PacSec here.
Drone hijack hardware demonstration at PacSec in Tokyo. pic.twitter.com/NQxA82qJTD
— dragosr (@dragosr) October 26, 2016