Should the DMCA be revised?
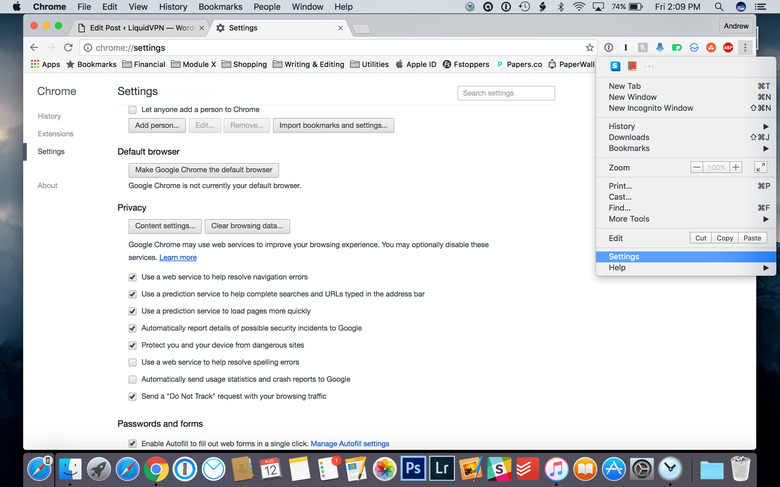
In June 2016, a group of over 180 musicians started a new battle with websites like YouTube and the government to revise the DMCA. For years the music industry has been fighting with Google's service over copyright issues. But what is the DMCA, and should it be revised? Digital Millennium Copyright Act The Digital Millennium Copyright Act (DMCA) is a copyright law in the United States. It carries out two different treaties of the World Intellectual Property Organization (WIPO). WIPO is a patent office, except for the entire world. The DMCA makes it illegal to share or produce technology, devices, or services meant to go around digital rights management (DRM). DRM controls access to copyrighted content, like books, movies, and music. For example, many ePub files in Google Play books have Adobe DRM. Supporters of DRM say that it stops people from copying protected content. Opponents of DRM say that there is no evidence that it prevents copyright infringement, and instead lets big businesses stifle innovation and competition while hindering legitimate users. Both the Electronic Frontier Foundation and Free Software Foundation say that using DRM is an anti-competitive practice. Safe Harbor The DMCA gives services like YouTube "safe harbor". In general, safe harbor "is a legal provision to reduce or eliminate liability as long as good faith is demonstrated." In relation to the DMCA, safe harbor means that YouTube is not held liable for copyright infringement from its users, as long as the company responds to takedown notices from rights holders. Music labels and publishers claim that this gives YouTube an advantage in negotiation, a power that music companies like Spotify do not have. In March of this year, the Recording Industry Association of America (RIAA) called this a "value grab." Safe harbor laws are relevant for everyone. Companies like LiquidVPN, rely on the safe harbor to create privacy services that don't track what people do online. If safe harbor laws did not exist, these companies would either have to shut down, move to a different country or log everything that users do. As you can imagine, this would be a huge blow to companies that support privacy. However, it seems that safe harbor is not good enough for the music industry anymore. The Petition RIAA manager Irving Azoff has made the reform of DMCA a priority. By "reform" what he really means is forcing services like YouTube to pay more in music royalties and removing the safe harbor liability exemption. This would have significant consequences for many companies, not just YouTube. YouTube lashed back, saying that its Content ID system makes it easy for content owners to identify uploaded music. However, the rightsholders say that it isn't enough, and claim they are losing millions. Whatever the case, the fate of DCMA should not be left in the hands of the music industry. They are notorious for anti-competitive, anti-user stunts. On April 1, 2016, hundreds of artists, along with labels like Universal Music, Sony Music, and Warner Music, signed a petition calling for this reform. In part, the letter states: "DEAR CONGRESS: THE DIGITAL MILLENNIUM COPYRIGHT ACT (DMCA) IS BROKEN AND NO LONGER WORKS FOR CREATORS. As songwriters and artists who are a vital contributing force to the U.S. and to American exports around the world, we are writing to express our concern about the ability of the next generation of creators to earn a living. The existing laws threaten the continued viability of songwriters and recording artists to survive from the creation of music. Aspiring creators shouldn't have to decide between making music and making a living. Please protect them." Black Box In a way, this situation is almost laughable. The music industry itself takes millions from their musicians, yet they are using the artists almost like pawns. The term for this is "black box" royalties, and the industry makes no secret of it. Essentially, money from music held in worldwide escrow accounts is the black box. Many musicians do not even know it exists. Here's how it works: A songwriter earns royalties when one of their songs is played on the radio, television, or streamed/downloaded from the internet. Entities called performance-rights organizations (PROs) calculate and collect this money according to different rules in almost every country. They act as middlemen and receive/disburse the payments. If the songwriter is in a different country, a PRO in that country gets the payments. This PRO then gives the money to the writer's music publisher, who then gives it to the songwriter. But this process is slow and inefficient, and lacks transparency as money passes hands. The black box part comes into play when the flow of royalties passes from different countries. PROs hand out the money after a certain period, and most of it goes to the publishers. So unfortunately, it is entirely legal. The Numbers & the MTV Mistake It can be hard to feel sympathy when the music companies use millionaires like Taylor Swift and Paul McCartney, but it's still a problem. But the music industry isn't going about this the right way. The International Federation of the Phonographic Industry (IFPI) provided some statistics. In 2015, 68 million paid streaming music subscribers made up $2 billion in revenue to record labels. In contrast, $900 million users of ad-funded services generated $634 million. The biggest ad-funded service is YouTube and makes up the bulk of that revenue, but the music industry says this isn't enough. According to The Guardian, much of this battle with YouTube comes from "the MTV mistake", a big example of a bad deal that the music industry made. It created expensive music videos for MTV and used them as a promotion for song and album sales, and not money makers themselves. Later everyone found out that Viacom, MTV's parent company, made a bunch of money because of how popular these videos were, and were not paying royalties. The crux of the issue is that no matter how much the music industry complains over YouTube, they would complain even more if YouTube suddenly went under. There is a mutual relationship here. Record labels are loath to admit that they need YouTube more than YouTube needs them.
Read More