RSA security conference: 25 years of discontent and pranks
Attendees of America's largest computer security conference entertain themselves with harmless shenanigans.
The first time I went anywhere near the RSA information security conference in San Francisco, it was by way of a prank.
Two things I love to cover are computer crime and and enterprise security, so when I met friends for drinks at a downtown hotel bar during the conference one year they were genuinely surprised I'd never attended RSA. One of my drinking pals that night was Twitter's head of security, and he jokingly asked if I wanted to go to RSA — right now.
Seeing the confused look on my face, he explained that RSA's big, lavish, exclusive "Codebreaker's Bash" was happening at the very hotel whose Grey Goose supply we were currently draining. He grabbed the badge of another Twitter security employee sitting next to me, and handed me his own. To get in I just had to follow his lead, and impersonate him.
Turns out I wasn't a very convincing head of security at Twitter. We cruised past a few sets of intimidating security teams (who were more concerned about my inability to match the Victorian-themed dress code) and then my guide toured me around a fairly opulent ballroom of endless shrimp platters and flowing champagne.
Pranking me like only a hacker would, he made a point of introducing me to attendees he claimed were from the FBI. Seeing as that the conference is a mix of government, enterprise, commercial security product vendors, and contractors, I'm inclined to believe the nice gentlemen teasing me over champagne cocktails about whether or not my name was really "Bob" were actually with the agency.
As an event, RSA began as a non-corporate gathering that grew big enough by 1994 to have its second event at the Redwood Shores Sofitel — a good distance both in physicality and spirit from its present-day sprawl of 40,000 attendees filling up San Francisco's Moscone Center. Reflecting on RSA's Softel days, one anonymous source recalled beloved industry elder Bruce Schnier as "some kid named Schneier who sold me a book called "Applied Cryptography" from a blue nylon duffel bag he had full of them."
But even though RSA Conference has changed a lot since its inception 25 years ago, attendee pranks are among its consistencies. My source explained that as the conference became more business focused into the late 1990s, there were power struggles and "a lot of bad blood." At that time, RSA didn't let just anyone attend the conference. I was told, "European competitors couldn't get a booth. If you did things that they didn't like you couldn't get a booth."
So, a number of the earliest RSA "pranks" were essentially getting one over on the powers-that-be by way of what we'd now consider guerrilla marketing — mild by today's standards, criminal to RSA at the time. If you couldn't get a booth at the conference, my sources explained, "you'd get a suite at the W Hotel and hire people to hand out leaflets inviting them to your thing. The RSA people were humorless and reacted in humorless ways. I don't know that they ever actually tried to get guerrilla marketing, off-site events arrested, but the tales flew that they did."
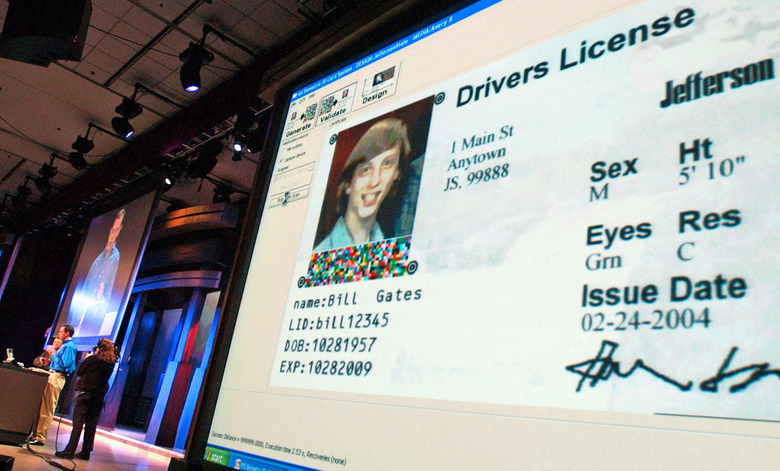
RSA's big party (then called the "RSA Cryptographer's Ball") was also a target for these seemingly harmless pranks. The dot-com boom days of the early 2000's was when the party had top tier musical acts, custom martini bars, cigar bars, single malt scotch, and according to our source, one year there was literally caviar. Getting in was a brass ring — which meant social engineering your way in and spoofing badges was a hot prank.
This was especially because RSAC people didn't like badge sharing, attendees asking for plus-ones, and hated any other after-hours parties. I was told, "If a company was known to throw an after-hours party, they might get denied booth space next year (yes, really) so a number of these were themselves pranks and almost like speakeasies. There were people who ran secret mailing lists to let people know where the parties were. (People involved with Survival Research Labs* helped a lot with this.) RSA parties were kinda like SRL events, where the location was a secret until the last minute."
One year, our source explained, the RSA Cryptographers Ball was at an undisclosed location "and we were all herded into buses. A number of people had in a matter of just a few hours hacked their own tickets and followed the buses to the California Academy of Sciences in Golden Gate Park, found parking, and then walked in through the kitchens in their tuxes and ball gowns playing dumb. They beat us through the gauntlet that we other people had to go through."
Enter Team Sadface
Around 2010, RSA Conference became the dated-feeling, mega-corporate trade show of security vendors and U.S. government agencies it is today: A boring event that feels like it's staffed by other people's parents, and where nothing really happens. By this time, these people's kids had all grown up, and for this line of work there were way more exciting and inclusive conferences to attend, like DEFCON and HOPE (Hackers On Planet Earth). Anyone female or non-white would've already felt alienated by getting stuck in their company's RSA booth. Worse, if you were young in an industry that looked richer than god and promised triumph over threats that would've been five years old — five years ago.
So on the days they didn't have to wear suits and stand in an RSAC booth for work, a group of young pranksters came together to ask just how much pranking could be done on the conference's expo floor.
The answer to that question was, a lot.
RSAC in the 5-year span around 2010 struggled for relevance in its keynotes and talks the same way it does today. But the conference was expanding into China, and its expo floor was turning into a sales-forward infosec circus sideshow. Companies such as Dell, Microsoft, Intel, MacAfee, Cisco and HP had booths alongside hundreds of smaller security vendors, along with the FBI, DHS and NSA. Every one of them would do practically anything to attract attention and get bodies in their booth. They staffed their expensive little patch of carpet with clueless salespeople tasked with running demos and contests on hacking that were beyond their skillsets.
For the prankster hackers calling themselves "Team Sadface" — named for the looks they left on the faces of salespeople — this was a playground.
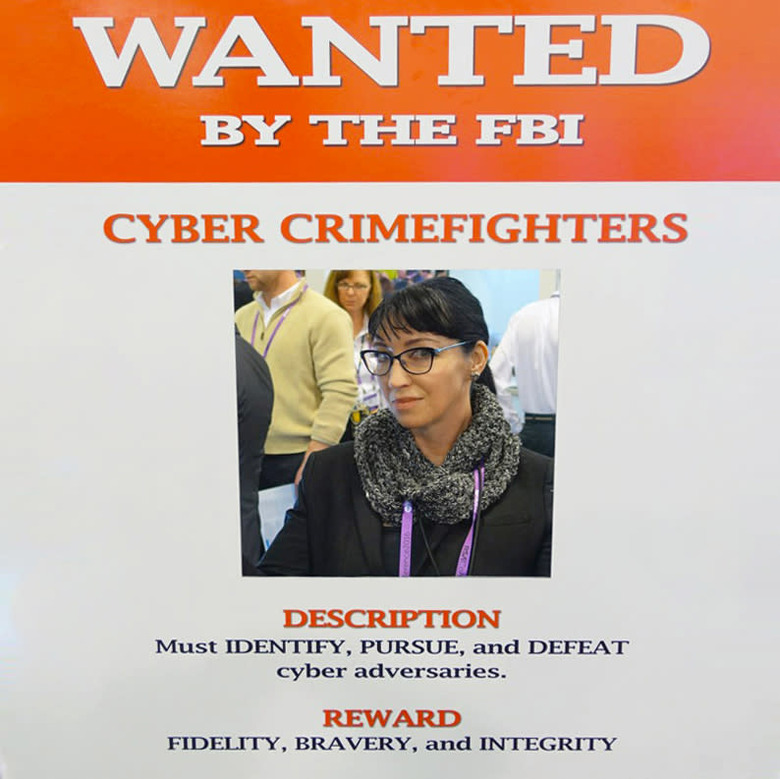
Crashing demos was easy for them, but boring. One year, members of Team Sadface arrived to the conference with fake FBI challenge coins. These tokens hail from a military tradition, indicating special achievement and membership. In hacking culture, these small, heavy coins bear the insignia or emblem of an organization and are awarded to winners of hacking contests, or those who earn (or prove) membership into a hacker crew or group. The coins also prevent name dropping and insulate against untrustworthy outsiders. While in conversation with a group of people at a European hacking conference a few years back, I mentioned my association with a certain crew — and was relieved I had my coin on me when I was demonstrably challenged to prove it.
As you'd imagine, Team Sadface was really proud of its FBI challenge coins. Unfortunately, the coins only saw use once or twice — when Team members would show up at the FBI booth, present the coin, and say they were here to collect their prize. People staffing the FBI booth reacted as you'd expect; confused. Prize? What contest? Team Sadface would wait patiently as one FBI employee would go get someone who might know, who would go get someone who might know... All in fun, to see if maybe some kind of cool prize would be produced. Because unlike the DHS and NSA, the FBI actually has really great conference schwag, like patches. It was a no-go, but apparently everyone really liked the coins.
Nowadays, the RSAC conference expo floor doesn't have any hacking contests — but it used to. Nor are any prize drawings done on-site. But during this short time frame, which was team Sadface's heyday, there were lots and lots of hacking contests for prizes. In the booths, sales and marketing staff didn't stand a chance against players who took the industry's challenges seriously.
Not unlike today's bizarre "hackers are evil, come meet this celebrity hacker" marketing at RSA, the contests back then were framed with slogans and concepts that mixed PR with a near-pathological confusion of good guy versus bad guy. One was framed to would-be contestants with the challenge, "Do you have what it takes to be a cyber criminal?" To people who actually knew what it took to be a cyber-criminal, this sounded like someone in marketing was either crazier than a shithouse rat, or was desperately trying to remake the world to meet their own expectations.
Most of the contests were Flash games (and I'm guessing every hacker who just read that line is now grinning from ear to ear). One Flash game had a "random acts of crime" counter — the more crimes, the higher your score — and this was apparently easy to reverse. Easy for Team Sadface, that is. For some of these contests, they explained to me, the payloads to walk up and win first place would even be preloaded for deployment from their phones.
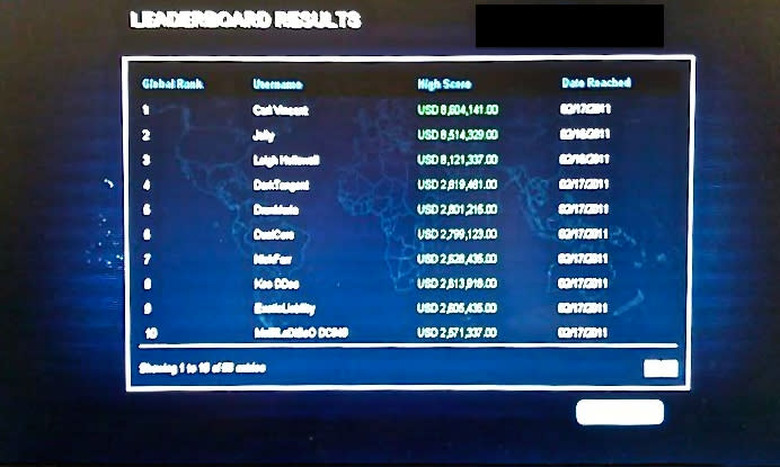
One booth game framed the player as a botnet herder with a set amount of exploits to assign to different countries on a global map, with each country earning different amounts of money (points). The goal was to make as much money as possible with the least amount of expenditure; scores and winner names were racked up on the booth's leaderboard throughout the day.
For this game, Team Sadface ditched their business suits so they would be considered unimportant by the salespeople (and they were). First, they pretended to play the game. While one would play badly and lose, another Team member would take photos of their friend losing — photos that included information other than their loser friend eating shit on a stupid Flash game.
The next day of the expo, Team Sadface pretended to play the game four times throughout the day, which happened to be the times awards were being handed out for top scores on the board. They won each time, and by the end of the day had amassed a group of fans, attendees in suits, who were coming back to the booth to cheer them on. On the last day of the expo, Team Sadface returned for a final round of winning, and to leave the board in hacker style. They left a final prank, rewriting the board with impossibly high scores (containing "1337") and tagging the name fields with the handles of other hackers as winners.
The wild years of Team Sadface at RSA weren't limited to computer hacking. One company's publicity scheme centered on a timed contest to hack physical locks. The event was based around Master Lock's "directional" padlocks: If you could open the lock in 5 minutes, you'd win.
But there was just one problem: Sadface crew included and liaisoned with the best lock pickers and safe crackers around, and these locks (which store the combination in a mechanical hash) were actually terrifically secure. Simply hacking these locks wasn't going to be an option. Nor could Team Sadface pre-pick the contest locks, as they'd done previously with a different lock opening contest on the expo floor.
Again out of business suits and aiming to not be taken seriously, Team Sadface played a few rounds with the locks to lose, asking "really dumb" questions and hanging out to see what they could see.
They noticed that in between the contest sessions, each lock would need to be reset. The annoyed and flustered salesperson who reset the codes didn't have a private area to perform the resets, and sat in the same place each time. He also didn't notice the Team Sadface member in t-shirt and jeans who looked over his shoulder each time, and relayed the codes to other members. After that, the Team "won" eight or nine times.
The salespeople knew something was up. Salesmen told the exuberant winners of their lock cracking contest to come pick up their prizes at the end of the expo. Naturally, Team Sadface showed up to claim their pirate's booty — and were met with a woman who wasn't having any of it. She told them, "We don't know what you did. But we know you did something. No prizes for you." One Team member recalled the exchange with a huge smile saying, "She was stone cold. I have so much respect for her."
* Disclosure: I am a former member of Survival Research Laboratories.