Should we be worried about election hacking?
Turns out our election systems are as secure as Ashley Madison.
When you know you're gonna lose, one surefire way to cast doubt on your loss is to say the whole thing was a setup.
That's exactly what Republican presidential nominee Donald Trump did when he found out that he was trailing Democratic nominee Hillary Clinton by nine points in Pennsylvania last month. While campaigning in the state, he said that the only way he could lose Pennsylvania is through fraud — as in, electronic voting machines that could be hacked.
This happens to be an issue that everyone from hackers to large information security companies have been trying to draw attention to for more than a decade.
Trump's malfeasant wet dream started to look like reality when Brian Calkin, from the Multi-State Information Sharing and Analysis Center (which shares information with the FBI), said Monday that MS-ISAC found three states targeted in recent voting-related hack attacks, though so far he's not naming names.
That same day, a need-to-know, insider-only FBI flash on recently hacked elections systems was leaked. It confirmed that two unnamed states were breached and voter data snatched. Embarrassingly, the attackers used common off-the-shelf tools left in the default settings, employing a very basic flavor of attack called a SQL injection. Which is to say that literally anyone could've done it, possibly even someone with Trump's IQ.
Many believe the two states in question to be Arizona and Illinois. Earlier this week, Arizona's state government said its voting system was offline in June to cope with an attack. As for Illinois, its general counsel of the state's board of elections, Ken Menzel, said a data breach discovered in July saw the theft of registration records for 200,000 voters.
We're still in the dark as to which state is behind door number three. According to reports, an anonymous attacker in June targeted an unnamed county election official with a phishing email that installed a keylogger. Snatching the unknowing official's credentials by recording their keystrokes, the invaders got access that would've allowed them to do things like delete voter registration records and prevent people from casting ballots.
Phishing and SQL injections — two simple and entirely preventable attacks that have had infosec pundits facepalming in dread all week.
But it's not just security basics putting our democratic process at risk: It's hubris. It may not be reassuring coming from hack-illiterate Homeland Security Secretary Jeh Johnson, but during a call August 15th with state election officials, he offered them the use of DHS cyber-hygiene services around voting — which would help secure election infrastructure by scanning for vulnerabilities and implementing NIST recommendations. Incidentally, such measures could prevent SQL injection attacks.
Despite those benefits, two states rejected the offer, including the great state of Georgia, which exposed six million voters' private data in a security blunder earlier this year. That was when the office of Georgia Secretary of State Brian Kemp sent twelve different media organizations CDs containing the private information of the state's six million registered voters — which included their names, home addresses, dates of birth, race, gender, Social Security and driver's license numbers. Among the outlets that received the unencrypted files were The Atlanta Journal-Constitution and Georgia GunOwner magazine. The "error" was blamed on one IT employee, who was fired.
In an unpalatable twist this week, Kemp has been named to work with the DHS's Election Cybersecurity Panel.
Zeynep Tufekci, a University of North Carolina information and library science professor, told NPR over the weekend that Georgia is running electronic-only machines that have zero paper trails. Not only are the machines used in the state more than ten years old and the hardware "falling apart," he said "the operating system they're using is Windows 2000, which hasn't been updated for security for years, which means it's a sitting duck."
Unfortunately, this problem isn't confined to the Peach State. Voting machines throughout the US are so old and feeble they're practically pedal powered. And they were born that way. Def Con has been joyfully cracking voting machines since at least 2004. In fact, the machines are so badly maintained, historically backdoored, and easily hacked that even Def Con hackers massively stress out about the voting process in their own forums and chat spaces.
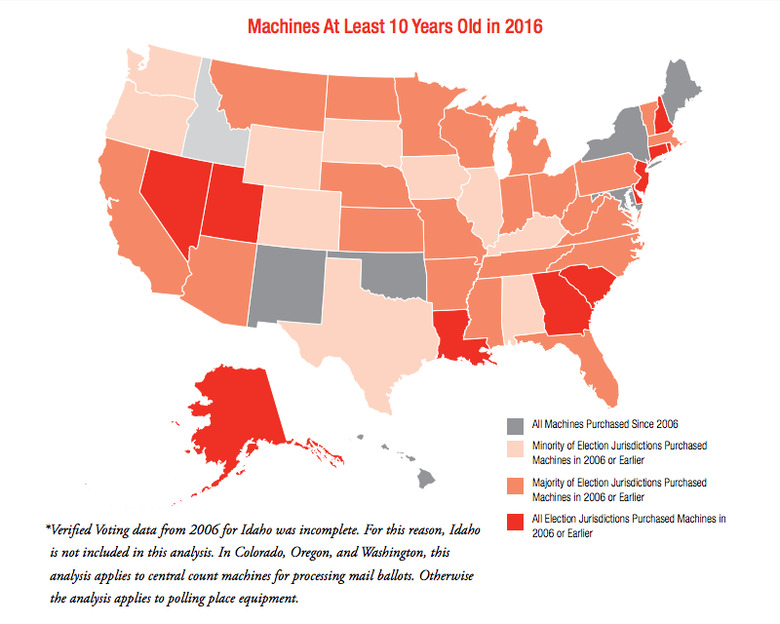
For this election, most voting jurisdictions will be using machines that are at, or near, the end of their life cycles. It's not even an opinion anymore; a study released last year by the Brennan Center called "America's Voting Machines at Risk" puts it on the record.
According to the paper's findings, voting machines are like laptops in that they're not supposed to last a decade and must be upgraded to avoid "flipped votes, freezes, shut downs, long lines, and, in the worst case scenarios, lost votes and erroneous tallies."
"Voting Machines at Risk" also tells us that "Forty-three states are using some machines that will be at least a decade old in 2016.... In 14 states, machines will be 15 or more years old."
What's worse, "nearly every state is using some machines that are no longer manufactured and many election officials struggle to find replacement parts," according to Larry Norden, the report's author. He recently told press that "everything from software support, replacement parts and screen calibration were at risk."
On the upside, the report does mention that the machines get put out to pasture now and again. Apparently the state of Virginia "recently decertified a voting system used in 24 percent of its precincts after discovering that an attacker could get in through the machine's wireless features to record voting data or inject malicious data."
It's all too convenient for Trump and anyone else who loses on election night, who can cite everything here as "proof" that their elections were rigged. The terrifying fact is that our election infrastructure is caught in the crossfire of pisspot politics, its security has been neglected from the get-go, and it's time for the voting machine glue factory in every curtained stall.
So should we be worried? Yes, I think so.
Distressingly, "America's Voting Machines at Risk" added that "in interviews with dozens of election officials and independent technology experts, the word 'crisis' came up repeatedly."
At the risk of being crude, that's not exactly the word I'd use for it.
Image: PETER MUHLY/AFP/Getty Images (voting machines circa 2002)