How Intel's Chief Software Security Officer is reshaping the chip giant
Industry veteran Window Snyder is ready for the challenge.
Window Snyder transformed how Microsoft, Apple and Mozilla dealt with software threats. She served as the security lead for the Windows XP Service Pack 2 update, which fixed a wide variety of vulnerabilities in a notoriously buggy OS. And at Apple, she helped manage security on iOS and OS X. Now, she's taking on the role of Intel's first Chief Software Security Officer, where she's responsible for revamping how the company protects its products and customers. Obviously, she has her work cut out for her.
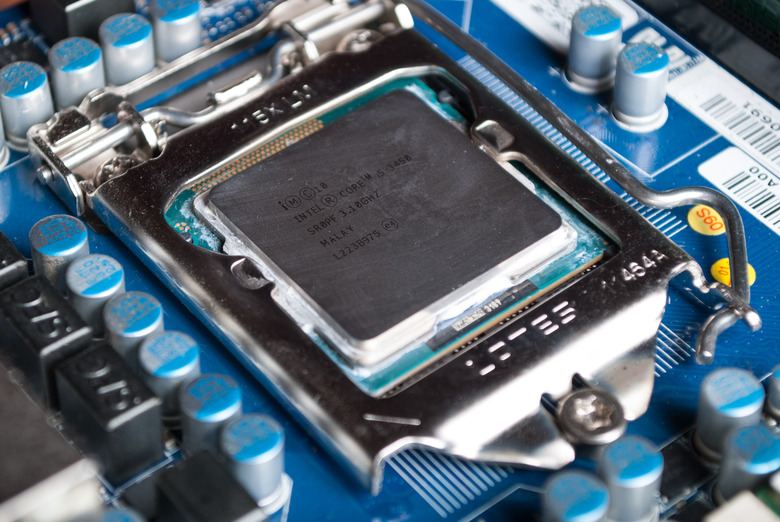
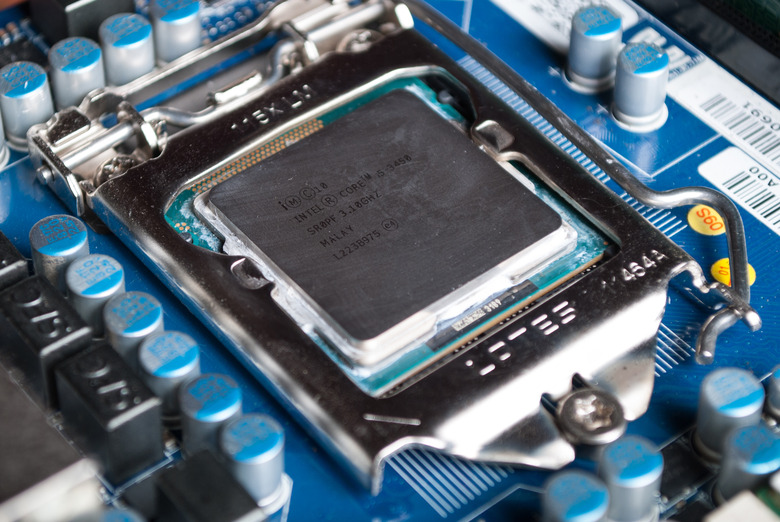
Intel is still reeling from the fallout of the Spectre and Meltdown CPU vulnerabilities, which affected the entire PC industry, including competitors like AMD and ARM. While most companies were able to deal with Meltdown through software patches, they could slow down PC performance. And we'll have to wait for an entirely new chip architecture to be rid of Spectre. As the largest PC processor maker (Samsung stole the crown of the biggest chipmaker last year), Intel took the brunt of the criticism. And it didn't help that the company failed to warn government officials about the issues, or that they were revealed by The Register instead of an official announcement.
After three months as the head of Intel's Platform Security division, Snyder has identified three ways the company can improve, she said in an interview with Engadget. First, she wants to focus on the obvious: Anything that can make software and hardware more secure and resilient. That includes things like cryptographic instructions in the company's chips that can speed up encryption, to features that can isolate processes from each other (like separating something that's running with unrestricted root access from a more limited user). "These are examples that are part of Intel's long heritage of developing security technologies, but I think they are ones that are easy for a large audience to understand," she said.
Next, Snyder wants to focus on building tools that can evaluate hardware and software to suss out any nefarious code. "Things like getting back to a known state, or a reset function... or helping you understand a data system in one way or another," she said. "Even if it's exposing information that can be used by forensics tools to understand whether or not the firmware in the system is intact."
And finally, there are tools that leverage the above two security categories. "They're used to build something else on top of it that enables an experience that may or may not be security-related," she said. That includes things like authentication, which directly ties into security, or content protection, which doesn't. Currently, Snyder says she's focusing more on the first two security categories, which will help build a strong foundation for Intel.
Snyder was diplomatic when we asked how her strategy differs from what Intel was previously doing. "I think there were a lot of different investments that might have been good ideas on their own," she said. But with a more cohesive strategy, Intel will be able to make sure that it's investing in things that actually serve their customers, as well as give the company a way to measure if a particular security strategy is successful.
For the past few months, Snyder has been traveling to chat directly with customers and researchers. "I'm out there asking questions, and I'm engaging folks to try and understand what their priorities are, what problems they're having, where they feel like they've got the support, where they feel like they don't have the tools that they need or they don't have what they're looking for when it comes to security," she said.
At Microsoft, Snyder organized the Blue Hat Hacker Conference to open up dialog between security researchers and the company's management. Gathering a bunch of people who are hacking your software might sound like a trap, but as she explains, "It was kind of a trap, but it wasn't for the hackers that so generously came and spoke. It was for the executives that we corralled into the room so that they could actually see, 'This is what our customers are up against.' I feel like they were really supportive of the security work we were doing, when they could see that there were security researchers in the community demonstrating the methods that they would use to attack [Microsoft's software]."
Last year, Intel cancelled its long running Developer Forum — deciding instead to focus on smaller events and individual communities. While Snyder didn't mention anything specific, it wouldn't be a stretch to imagine a similar gathering like the Blue Hat conference where Intel can directly engage with the broader security world. She's also still very interested in working together with AMD, Qualcomm and the rest of the chip industry to deal with the fallout from Meltdown and Spectre — and beyond.
"I think it's incredibly important to make sure that we're working with the [chip] ecosystem, not just in response to vulnerability but in general to build strength as a platform," she said. "We're all in this together, so working with security researchers, working with enterprise and folks who are on the corporate security end of things or the deployment end of things to the data center, to people who are actually writing security software, to the operating system folks. There's a component of the story in all those areas, and since what we build supports computation everywhere, we need to be engaged with all those communities."
Looking ahead, Snyder's more focused security philosophy will also be at the center of how the company pursues new markets, like mobile modems and IoT. "They're different parts and different environments," she said. Because of that, the company will have to evaluate exactly how they're being used, and determine the best way to avoid security risks. But those threats will constantly change, which leaves her in the difficult position of trying to anticipate what's coming. The last thing Intel needs is another Meltdown.
Photo credit: Emilija Randjelovic via Getty Images