How could Lenovo miss its Superfish security hole?
Until mid-day yesterday Lenovo thought the biggest problem with Superfish VisualDiscovery was the annoying ads it caused to pop up on customers' laptops. SuperFish was supposed to analyze images on the web and "help" consumers find similar products, but the information security world was learning that it (apparently unintentionally) does quite a bit more. Facebook engineer Mike Shaver tweeted Wednesday night about how the preloaded adware performs a man-in-the-middle (MITM) attack on supposedly secure connections, and by Thursday morning security researcher Rob Graham showed how it could be used to spy on the encrypted communications of anyone running the software. At that point, Levono CTO Peter Hortensius still referred to resulting security problems as "thoretical" but moves today from Microsoft and the US government — and his comments to us — show that they've realized the threat is very real.
Update: Lenovo has just released a Superfish removal tool. In an accompanying statement (included after the break), the company says it's also working with McAfee so that virus scanners will remove the software and its certificate.
Now, Lenovo admits to the gravity of the problem (even if the company behind Superfish does not, as shown by a spokesperson's comments to Ars Technica) and is working with others in the industry to fix it. Still, the question remains — how did a security hole this problematic get there in the first place? As Hortensius told me, that's the question he and his team will be trying to answer over the next week or so.
How to make Superfish go away
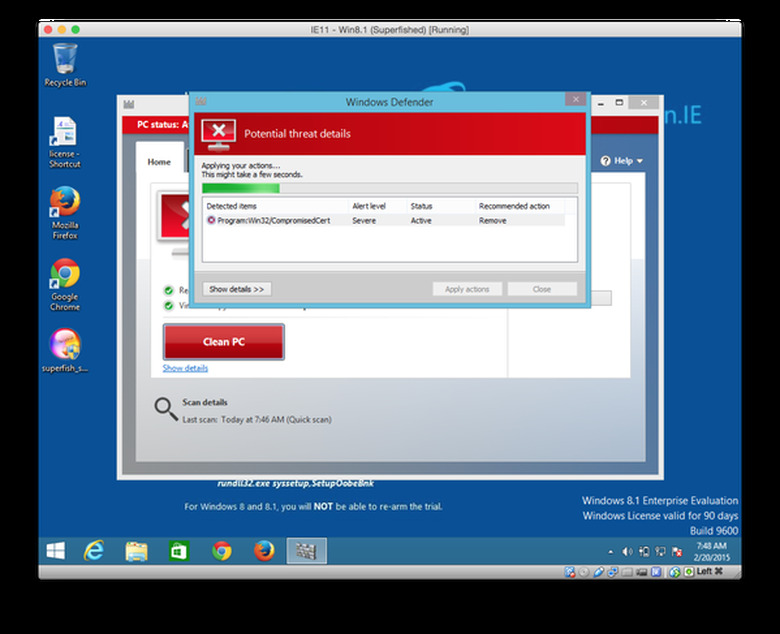
The first priority is making sure that Superfish disappears and the security hole is closed, and there's several ways to make sure your PC is secured. Browser test pages (Filippo.io, LastPass) can tell you if you're affected and give tips on removal. Lenovo has its own list of uninstallation instructions, and as of today Microsoft's Windows Defender scanner has been updated to remove Superfish and its security certificate. You can expect for other scanners to get a similar update soon, and of course Lenovo is working on an uninstall program of its own that could be available later today.
Why is Superfish such a big problem?
Superfish's security problems are worsened by practices researchers have uncovered over the last day or so: not only is its security certificate easily extracted, as Rob Graham discovered, it uses the same one on every computer. It appears that Superfish (and others) used technology from a company called Komodia to pull off its hamfisted intervention, and all of them are equally vulnerable. Even worse, beyond the initially discovered MITM vulnerability and weak encryption, the Komodia package can be easily tricked into accepting any certificate as valid. According to CloudFlare security team member Filippo Valsorda, that means it's easy to intercept encrypted traffic from anyone with Komodia-powered software on their system.
What is Lenovo doing about it
While we wait to find out the next way this will get worse, Lenovo says it is taking steps to turn things around. Of course, as security researcher Kenn White asked, after the company ignored respected security researchers "activating the Batsignal", restoring its public trust will be tricky. The software appeared on computers beginning in September, and posters on Lenovo support forums were asking questions that should've raised alarms for months.
This is not a level of maintenance like changing oil; this is whether your headrests will sprout spikes in an accident.
- MuninrepeeK eroL (@munin) February 20, 2015
According to Hortensius, Lenovo does security checks for software that it preloads, but apparently Superfish bypassed those even with this glaring security hole. He says "If we knew then what we know now, we'd never have shipped this", and that security practices, even the ones the company will institute going forward can never be 100 percent. He says that information with real substance is coming, that will detail how Lenovo plans to avoid getting caught out like this again, which will be key. Patching the software is relatively simple — filling in this hole in the company's reputation may not be so easy.
[Image credit: (shark) Martin Barraud, (Windows Defender scan) Filippo Valsorda]
Lenovo:
February 20, 2015
As we've said previously, Lenovo is exploring every action we can to help our users address the concerns around Superfish. In addition to the actions that we have already taken we are:
1) In addition to the manual removal instructions currently available online, we have released an automated tool to help users remove the software and certificate. That tool is here: http://support.lenovo.com/us/en/product_security/superfish_uninstall
2) We are working with McAfee and Microsoft to have the Superfish software and certificate quarantined or removed using their industry-leading tools and technologies. This action has already started and will automatically fix the vulnerability even for users who are not currently aware of the problem.
We ordered Superfish pre-loads to stop and had server connections shut down in January based on user complaints about the experience. However, we did not know about this potential security vulnerability until yesterday. We recognize that this was our miss, and we will do better in the future. Now we are focused on fixing it.Since that time we have moved as swiftly and decisively as we can based on what we now know. While this issue in no way impacts our ThinkPads; any tablets, desktops or smartphones; or any enterprise server or storage device, we recognize that all Lenovo customers need to be informed. We apologize for causing these concerns among our users for any reason – and we are learning from experience and improve what we do and how we do it. We will continue to take steps to make removal of the software and underlying vulnerable certificates in question easy for customers so they can continue to use our products with the confidence that they expect and deserve.