The NSA tried to use app stores to send malware to targets
It shouldn't come as a surprise to hear that the NSA worked on iOS and Android malware meant to capture information from a target's phone, but actually getting the software onto phones? That's tricky. To help solve that problem, the NSA (and the rest of the Five Eyes intelligence community) attempted to hijack data being sent to and from app stores like those run by Samsung and Google. According to a document leaked by Edward Snowden, obtained by The Intercept and published by the CBC, it was mostly in search of a way to implant secret surveillance payloads into those data connections in hopes of identifying an Arab Spring in action in other countries.
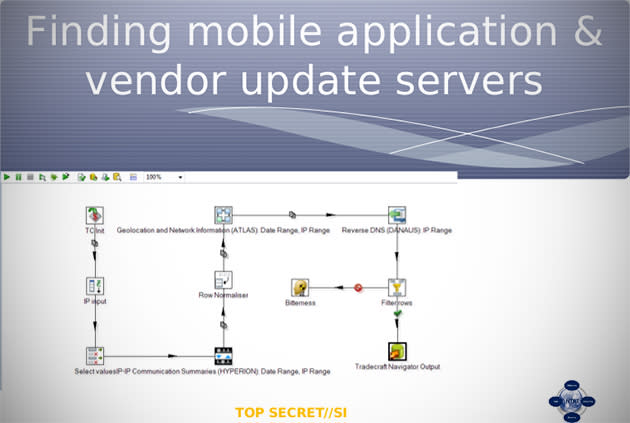
The project (code-named IRRITANT HORN) was deemed successful in the slide deck published today, noting that the team managed to "identify connections from the countries to application and vendor servers in non-5 Eyes countries." Though the group looked especially closely at a Google app store server in France along with similar servers in Cuba, Senegal, Morocco and Russia, its biggest payoff came thanks to a popular mobile app called UCBrowser that's owned and operated by Chinese e-commerce giant Alibaba. Upon closer investigation, the group discovered that the app was leaking user data -- think phone numbers, device information and SIM card identifiers -- back to servers in China. Naturally, the Five Eyes teams cooked up even more complex objectives if they found success in cracking those secure connections. The Intercept notes they also aimed to send "selective misinformation" to targeted phones in a bid to muck with dangerous or sensitive operations, not to mention quietly harvest information about certain users by way of those app store servers. Intelligence teams in the US, Canada, the UK, Australia and New Zealand worked on IRRITANT HORN for a good chunk of 2011 and 2012, though it's not clear how (or if) their work has progressed since then.

