Now you can explore Hacking Team's world of selling spyware
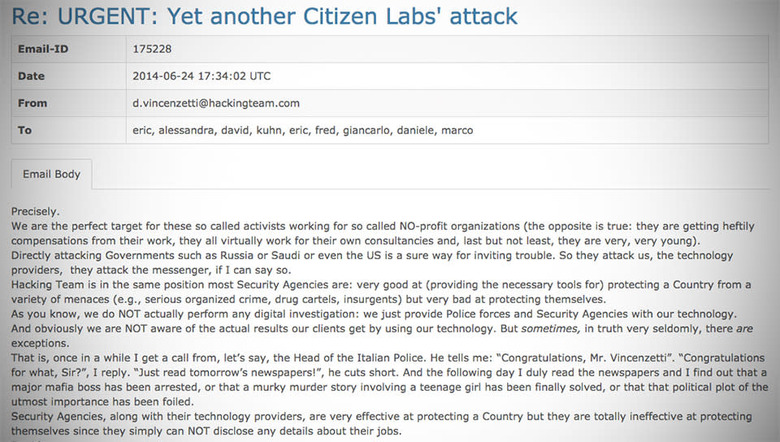
Plenty of ink has already been spilled about the Hacking Team's spectacular security meltdown, but why should the press have all the fun? WikiLeaks posted a searchable archive of over a million emails from the Italian IT firm last night, which means armchair sleuths can take a peek into the cloak-and-dagger world of selling spyware to governments with just a few clicks. Now obviously not everything contained in this hefty database is damning; lots of it just chronicles the day-to-day operations of a lucrative business. Every once in a while, you'll find something almost shocking in its mundanity, like this corporate email blast about restaurants in London that wound up in Hacking Team COO Giancarlo Russo's inbox. Still, there are plenty of juicier tidbits waiting for you if you keep a few keywords in mind.
Searching for hits related to Uzbekistan — a country whose track record for human rights violations has been generously referred to as "atrocious" — turns up a series of conversations between members of Hacking Team and employees of a company called NICE that were keen to keep specific details about its client off the table. We can make some pretty solid guesses about who'd actually stand to benefit from Hacking Team's remote surveillance tech, though — NICE Systems is a known business partner of Uzbekistan's National Security Service. Meanwhile, searching for ".gov" brings up (among other things) a thread in which employee of what appears to be Saudi Arabia's Ministry of Interior really wants to make sure Hacking Team's system can capture traffic even if the target is using Tor or some similar obfuscating tool. The answer? A resounding yes. There's plenty of more sifting to do in the coming days and weeks, so why not jump in and see what there is to see?