Researchers find popular car immobilizer can easily be hacked
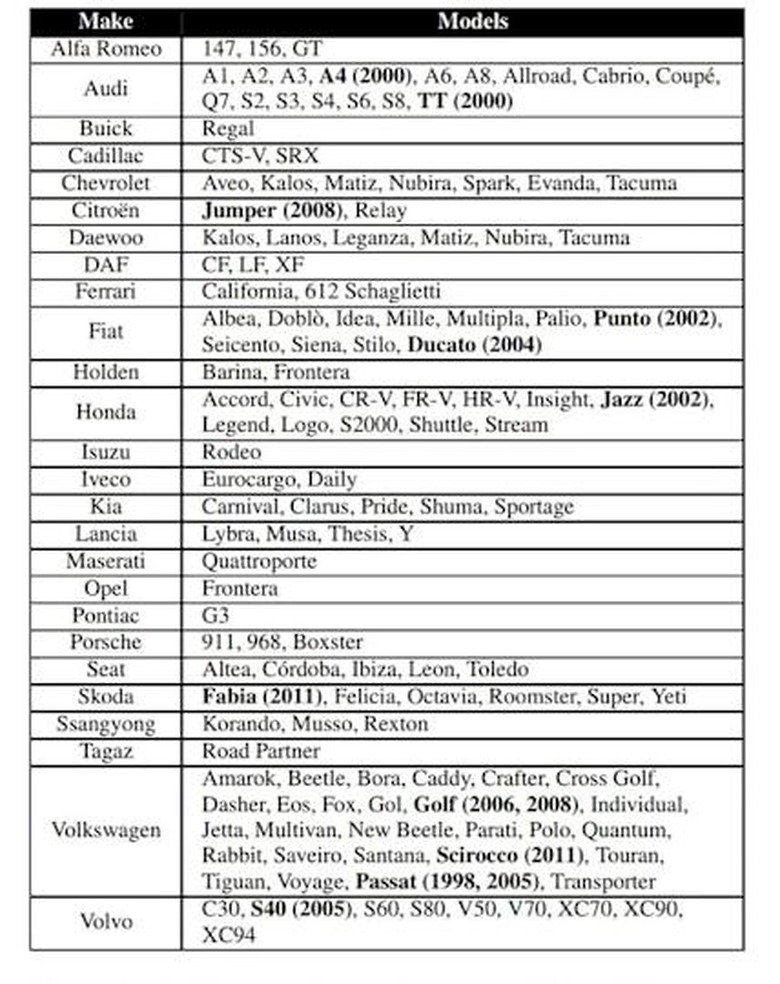
Immobilizers are supposed to kill a vehicle's engine to prevent it from being stolen. However, a trio of researchers recently released a study that reveals the Megamos immobilizer system used by more than two dozen car manufacturers — including Volkswagen, Porsche and Honda — can be cracked with "trivial" effort. They would have revealed this glaring encryption flaw two years ago, when they completed the study, except that Volkswagen and European defense contractor Thales sued them to prevent its publication.
The research team from Holland's Radbound University found that the radio signal from the key fob to the car alarm, which has to be nearby to unlock the car and disable the immobilizer, can be intercepted by thieves (and security researchers). By eavesdropping on the data transmissions between the fob and the security system, the team was able to figure out which cryptographic key would unlock the system's encryption and disable the immobilizer. It took them less than 30 minutes.
The team said that it had been in contact with a number of the affected manufacturers about patching the flaw. However, the team points out that any solution would be difficult since it would involve swapping out the physical chip in the fob for a more securely designed one. "This is a serious flaw and it's not very easy to quickly correct," Tim Watson, Director of Cyber Security at the University of Warwick, explained to Bloomberg Business. "It isn't a theoretical weakness, it's an actual one and it doesn't cost theoretical dollars to fix, it costs actual dollars."
This revelation follows a string of recent security flaw discoveries throughout the automotive industry including the Ownstar hack, the Tesla S debacle, the text message takeover trick and the infamous highway Jeep attack that saw 1.4 million Fiat Chrysler vehicles recalled.