America accuses Iran of hacking the dam, cyber-squirrels rejoice
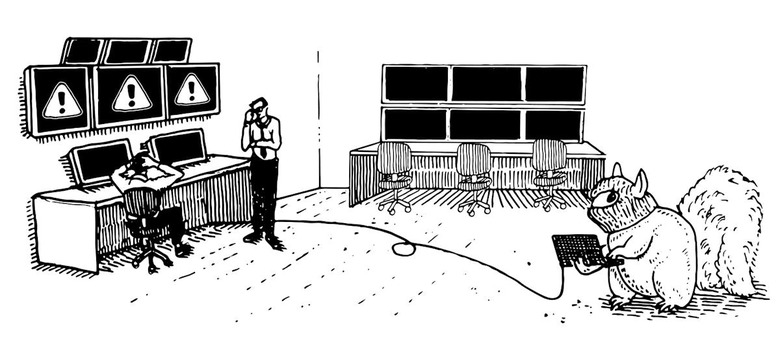
While America is worrying about nation states, our infrastructure is being terrorized by rodents.
As cyber-geddon stories go, Middle Eastern countries hacking into US dams or power grids and making stuff go haywire sounds like the plot for a not-so-subtly racist Hollywood scare flick. But that's the story we got when news outlets, citing unnamed sources, recently reported the Obama administration would be calling out Iranian hackers as the culprits behind a malicious 2013 breach at a New York dam.
Outlets reported at the time of the disclosure that hackers were "unable to get into the full dam system, but could take control of the flood gates."
The news drama here hinges on reports that hackers accessed the dam's floodgate controls. The Bowman Avenue Dam near Rye Brook, New York, whose only purpose is to mitigate flooding, does have a computer-operated sluice gate ... er, it does now, anyway.
After the Department of Homeland Security approached the city of Rye about investigating the dam in 2013, Marcus Serrano, Rye city manager, told local press something that's not making it into this week's resurgence of stories about Iranian hackers. In local news outlet My Rye, Mr. Serrano said:
"In or about June 2013, a sluice gate was added to the Dam, in order to help control the flow of water and assist with flood mitigation during storm events. The gate was designed to be opened and closed via computer; however, despite a ribbon cutting ceremony, the gate was never fully operational, and remained non-functioning through the DHS investigation. In any event, based on information provided to us, at no time was the sluice gate ever manipulated by unauthorized users outside of the city.
Subsequent to and after taking certain security measures consistent with the DHS report, the City did implement the sluice gate for the first time during a storm event on or about April 30 to May 1, 2014."
So the damn dam, which in this case was really more like an artist's rendering of a dam, was operating at less than a minimum. The Iranian "cyberspies" who "had access to [the dam's] control system" had it only in theory.
It seems like someone's trying really hard to make Iranian hackers seem more dangerous than bird poop.
Bird poop shut down Indian Point nuclear plant https://t.co/HSkJIXzkPb – Westchester NY
— CyberSquirrel (@CyberSquirrel1) March 3, 2016
If it's a contest, bird poop is kind of winning. But that's nothing compared to the most significant and active threat to our nation's industrial control management systems: sSquirrels.
In a July 2015 comment, John C. Inglis, former deputy director, National Security Agency, said, "I don't think paralysis [of the electrical grid] is more likely by cyberattack than by natural disaster. And, frankly, the No. 1 threat experienced to date by the US electrical grid is squirrels."
And he's right. With our government's increased focus on threats of cyberterrorist attacks on industrial control systems (like power grids), the data from the sardonic Cyber Squirrel Map proves that Iranian hackers have nothing on the leet haxxor skillz of those bushy-tailed little acorn-hoarding bastards.
To this effect, Cyber Squirrel 1 reminds its readers that "of all the claimed nation-state cyber attacks that have impacted critical infrastructure that we have been made aware of such as the Brazil Blackouts, German Steel Plant event, and the Ukrainian power outages only the US lead Stuxnet operation can be confirmed at this time. We are continuing to look into the December events in the Ukraine."
When it comes to executing successful infrastructure attack ops, squirrels have any and all government-sponsored hackers beat by a mile. Late last year, the hacker behind Cyber Squirrel began collecting "all unclassified Cyber Squirrel Operations that have been released to the public that we have been able to confirm."
Squirrel knocks out power of hundreds in Lee County https://t.co/vhukwO2Xyb – Lee County TX
— CyberSquirrel (@CyberSquirrel1) February 22, 2016
According to Cyber Squirrel, as of the beginning of March 2016, there have been 1,139 successful "cyber squirrel" attacks — though the running tally of ops is inclusive of all animals, including birds, rats, raccoons, and snakes.
It remains to be seen whether or not the Obama administration will finger Iranian hackers for the dam that wasn't really hacked — and what sort of evidence, if any, we'll get. Since someone's playing the cyber-attribution blame game here, maybe it's just that China and Russia got the week off.
Perhaps it's part of the monster-of-the-week cybersecurity news roadshow, conveniently brought to us by a DHS that just might be desperately trying to look like it's really doing stuff. The madness around this dam — the way it just doesn't add up but feels part of the general cybersecurity mood right now — along with the Apple encryption mania, feels like a kind of hysteria in the air, one that news outlets seem to breathe in and catch.
Surely, this dam coming back into the news so circumspect with fact is a harbinger: The next Big Bad to be leveraged for scaring up both legislation and clicks will be the hacking of industrial control systems (and switches).
But the beauty of Cyber Squirrel at a time like this is that it's all about perspective. That when it comes to domestic cybersecurity, authorities (and infosec) should be giving less attention to vague threats, and more to problems at home — like getting our infrastructure systems properly patched.
In the meantime, for whatever the hell happened (or not) at the Bowman Avenue Dam, my money's on squirrels.