The TSA is failing spectacularly at cybersecurity
Five years of Homeland Security audits found airport security can't even get the basics right.
Five years of Department of Homeland Security audits have revealed, to the surprise of few and the dismay of all, that the TSA is as great at cybersecurity as it is at customer service.
The final report from the DHS Office of Inspector General details serious persistent problems with TSA staff's handling of IT security protocols. These issues include servers running software with known vulnerabilities, no incident report process in place, and zero physical security protecting critical IT systems from unauthorized access.
What we're talking about here are the very basics of IT security, and the TSA has been failing at these quite spectacularly for some time.
The report centers on the way TSA (mis)handles security around the data management system which connects airport screening equipment to centralized servers. It's called the Security Technology Integrated Program (STIP), and TSA has been screwing it up security-wise since at least 2012.
In essence, TSA employees haven't been implementing STIP properly — that is, when they've been implementing it at all.
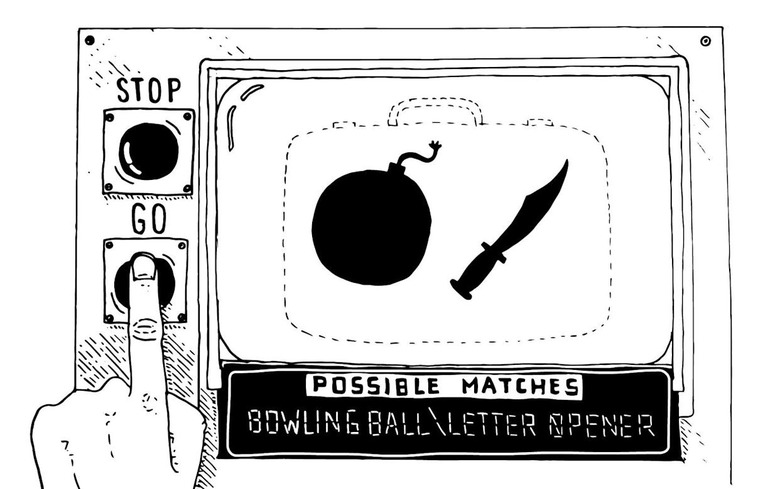
STIP manages data from devices we see while going through security lines at airports, namely explosive detection systems, x-ray and imaging machines, and credential authentication.
The bottom line is that the TSA hasn't followed DHS guidelines for managing STIP equipment, and the risks are grave, as spelled out in the report. "Failure to comply with these guidelines increases the risk that baggage screening equipment will not operate as intended, resulting in potential loss of confidentiality, integrity, and availability of TSA's automated explosive, passenger, and baggage screening programs."
"System owners" were preventing patches
If you thought the long security lines, missed guns, sexually creepy staff, and copied master keys for your bags were bad, just wait until you see the laundry list of infosec basics that TSA staff let slide. IT Management Challenges Continue in TSA's Security Technology Integrated Program is nothing to read before bed if you want to sleep the night before your next flight.
In addition to unpatched software and a lack of physical security that allowed non-TSA airport employees access to IT systems, the auditors found overheated server rooms and computers using unsupported systems — and much more.
The observed "lack of an established disaster recovery capability" noted by the OIG is particularly scary. If a data center was taken out by natural disaster, passenger screening and baggage info would be rendered inaccessible.
Not only that, but there was no security incident report process in place, and there was "little employee oversight in maintaining IT systems." And, auditors were not pleased at all that non-TSA IT contractors maintained full admin control over STIP servers at airports.
Intended as a positive note in an otherwise terrifying cavalcade of opportunities to hack the hell out of any given airport's security, IT Management Challenges Continue pointed out that TSA had indeed taken steps to resolve its STIP security issues.
"For example," the report said, "according to a TSA staff member, system owners may no longer prevent implementation of software patches due to concerns with system performance."
That sound you just heard was the collective rage-scream of 40,000 information security professionals who endured TSA security theatre to fly to RSA San Francisco last February and the 20,000 expected to fly to Las Vegas for Black Hat and DEFCON in July.
All I'm saying is, I can't imagine how outraged hackers and infosec workers will feel when they find out what's in these reports. Not to mention normal people, too.
"12,282 high server vulnerabilities"
Papers in the DHS's IT Management Challenges audits have reported these problems since 2012 and focused on specific airports. These include Chicago O'Hare (2012), Hartsfield-Jackson Atlanta (2013), Dallas/Fort Worth (2014), and San Francisco (2015). This new report was based on an audit at DHS data centers at the Orlando International Airport "to further assess the extent of STIP deficiencies and the actions the TSA has taken to address them."
As part of this year's final report, auditors watched TSA staff as they scanned STIP servers located at two DHS data centers and the Orlando International Airport. The scans "detected a total of 12,282 high vulnerabilities on 71 of the 74 servers tested."
One of the vulnerabilities sitting in plain sight dated back to 1999.
"Another cause for the software vulnerabilities," the report explained, "was that TSA did not test IT security controls on STIP airport servers or IT components of TSEs prior to equipment deployment."
Even the audit was incomplete due to TSA security failures. Eight STIP servers at Orlando couldn't be scanned, as the TSA didn't have any procedure in place to provide either remote scans or reports.
The report concluded with 11 recommendations of super-basic IT security practices, like not deploying servers with known bugs and updating the damn software when they're supposed to. These changes "should resolve many of the STIP IT security deficiencies identified in this and prior OIG reports," DHS Inspector General John Roth said.
The TSA agreed to make changes, but that's probably because TSA counted their options in this situation, and got to a total of one.
The DHS Office of Inspector General considers the issues to be open "until TSA provides supporting documentation that all corrective actions are completed."
Yeah, proof is probably a good idea, considering these reports have been blistering the TSA's cybersecurity hide with the same problems for five years running. The "strongly worded letter" approach doesn't seem to be working all that well.
But times have changed. Maybe when these audits began, there just wasn't enough cybersecurity awareness going around to slap TSA's attention into the here and now of taking computer security seriously.
Like the saying goes, there's no time to avoid a life-threatening cybersecurity incident like the present.
Images: AP Photo/Damian Dovarganes (TSA x-ray); Jakub Pavlinec / Getty Creative (cables)