It's not easy being Yahoo
Catching a break is tough when you basically suck at everything.
Remember when Yahoo was great? Yeah, I'm having a hard time, too. Especially in light of the past few weeks, during which the company's house of cards collapsed — and afterward those cards were set on fire and then pooped on by a passing flock of seagulls who'd had some bad curry.
After Yahoo copped to a monumental breach they'd kept secret, revelations about mass email spying catapulted the company into a whirlwind of abysmal press. These events were crowned by a report claiming Verizon asked for a $1 billion discount on its acquisition.
Most everything being reported about Yahoo is coming via anonymous sources. But one glaring fact rings true through the swirling rumors: If other companies are bad at protecting their users, Yahoo may very well be the worst.
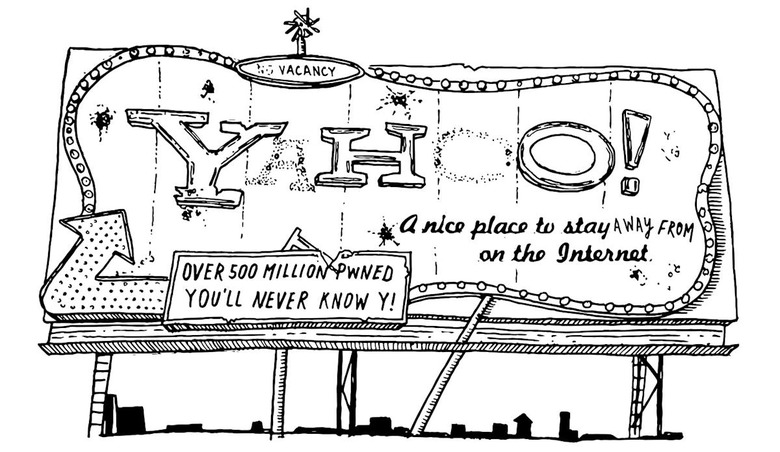
It started on September 22nd when, just after Yahoo's fire sale to Verizon, the flailing company admitted it was massively hacked in 2014. Its statement said that "a state-sponsored actor" had stolen at least 500 million user accounts' "names, email addresses, telephone numbers, dates of birth, hashed passwords... and, in some cases, encrypted or unencrypted security questions and answers."
The Yahoo hack is currently considered the biggest breach in history. Everyone wants to know why it waited so long to tell anyone, but the company has remained mum.
One could say that CEO Marissa Mayer simply fiddled while Yahoo burned. Several lawsuits were filed within days of the statement, six senators told Mayer they wanted a timeline of the hack, and another senator kindly asked the SEC to investigate. This would turn the company and this incident into a test case for the SEC's data breach disclosure rules.
Before anyone could say "Titanic," press went wild as unnamed sources came out of the woodwork to have their say. One told the New York Times that Yahoo's then-security chief Alex Stamos and his team had really tried super hard to make improvements, but mean old Marissa stood in their way. And because Stamos left Yahoo suddenly and without explanation, infosec pundits opined the real reason Stamos parachuted to Facebook was because he fought for the users (and certainly not the money).
If the accounts about her decision-making skills are true, the Times' scathing hot take on Mayer's governance of her security team is totally accurate. Except Stamos' team did so much innovative and experimental security stuff in the realm of improvements, it makes this angle look like horseshit.
This is probably a good time to remind everyone that the New York Times has a sweet little financial relationship with Facebook, where the Wal-Mart of social networks recently gave the Times $3.3 million for content.
The anonymous source sideshow wasn't over, and the next one at the microphone wasn't playing nice. Business Insider was told by a former Yahoo executive in contact with investigators that the number of victims is at least double the 500 million the company claimed. The source believes the hack is much "bigger than what's being reported." They continued, estimating the number of accounts affected to be anywhere between one and three billion, saying "How they [Yahoo] came up with 500 is a mystery."
Yahoo's attempt to blame state hackers (usually it's China or Russia) fell apart when a not-anonymous source talked to CSO Online. Security firm InfoArmor said it uncovered that hackers-for-hire did it. They found some of the stolen data during a three-year investigation into an Eastern European hacking gang. Andrew Komarov, InfoArmor's chief intelligence officer told CSO, "According to our information, most of the group's clientele are spammers." Komarov claimed the gang had sold the stolen Yahoo database in three private deals, including one worth at least $300,000.
Just when things were looking really bad for Yahoo... it got worse. On Tuesday, Reuters dropped a bombshell from yet another unnamed source with an axe to grind against the purple menace. According to "three former employees and a fourth person apprised of the events," Yahoo "last year secretly built a custom software program to search all of its customers' incoming emails for specific information provided by U.S. intelligence officials."
The article offered an alternative to the narrative in the New York Times about why Yahoo's head of security ran to Zuckerberg's warm embrace.
It said:
"According to two of the former employees, Yahoo Chief Executive Marissa Mayer's decision to obey the directive roiled some senior executives and led to the June 2015 departure of Chief Information Security Officer Alex Stamos, who now holds the top security job at Facebook Inc."
At this point, it was clear that every reporter sucking the teat of a source had forgotten to ask what Stamos and his team were doing, exactly, during the biggest hack in history. And why no one said a damn thing while millions (possibly billions) of innocent people had their sensitive info sold and re-sold on various black markets for years.
Yahoo called the report "misleading." But, as everyone noticed, there was no denial. Those who didn't have a big bowl of popcorn by this point were out of luck, because right after the "misleading" report, the New York Times fired back with even more anonymous source-ry. The Times' new article directly rejected Reuters' report that Yahoo built surveillance tools so the government could spy on Mail users.
The Times said, "A system intended to scan emails for child pornography and spam helped Yahoo satisfy a secret court order requiring it to search for messages containing a computer 'signature' tied to the communications of a state-sponsored terrorist organization." The alleged sources allegedly said that the alleged program had allegedly been terminated anyway. As for Stamos, yet another anonymously sourced Reuters article claims the program had been shut off by the time he left.
Furthermore, the New York Times sources said the scanning came out of a FISA court order and not "a classified U.S. government demand... at the behest of the National Security Agency or FBI" as Reuters had reported.
Talk about awkward.
Who knows what revelations the next few days will bring. But, with Reuters and the New York Times competing for headline dominance, it's easy to forget about all those Yahoo hack victims — and I don't just mean the ones we found out about two weeks ago.
The Yahoo hack story got pushed out of the spotlight before it had a chance to really sing. It turns out, getting hacked, exposing untold users to harm, and downplaying it is a performance the company has been repeating for years.
The 2014 hack we just learned about exposed at least 500 million accounts. Yahoo was also hacked in January that year, and the company would not disclose how many accounts were affected. Before that, in March 2013, Yahoo Mail users were crying for help about their accounts getting hacked into for months while the company remained silent. To the surprise of no one, later that year Yahoo user passwords were spotted in a collection of two million credentials found on a botnet server. And prior to that, in 2012, Yahoo was hacked and 450,000 passwords were posted online.
As I write this, I wonder if people on the security team at Yahoo who are caught in the crossfire, or who tried to fix things and got shut down by decision makers, are insulted by this portrait of negligence.
But I don't wonder how Yahoo's decision-makers feel. Because to be insulted, you first have to give a damn.
Images: REUTERS/Robert Galbraith (Yahoo / Marissa Mayer); REUTERS/Dado Ruvic (Yahoo Mail password)