Malware infects computers by hiding in browser ad GIFs
The "Steganos" exploit kit went undetected for two years by avoiding security analysts' computers.
Unless you still use Internet Explorer (and please don't do that), you probably don't have to worry about new malware discovered by Eset researchers. However, the Stegano exploit kit shows how adept hackers have become at slipping infected ads past major networks and then hiding the malware from discovery. It's been operating stealthily for the last two years and specifically targeting corporate payment and banking services.
The attack starts with javascript-infected ads for a "Broxu" screenshot app and, ironically, "Browser Defense," pushing them into large ad networks, where they appear on major news sites seen by millions of users. "We can say that even some of the other major exploit kits, like Angler and Neutrino, are outclassed by the Stegano kit in terms of [the quality of] websites onto which they managed to get the malicious banners installed," the team said.
So how did they escape the powerful anti-malware tech used by big ad networks? Once the ad is served, it runs a custom, cloaked javascript that runs an environment check. It's checking to see if you're running virtual machines or other environments typically used by security researchers. For those cases, it serves up a clean image, but for vulnerable machines, it serves up a special GIF file, caching data within the "alpha," or transparency channel.
As shown above, the image looks perfectly normal to the naked eye. When enhanced, though, you can see a pixel pattern that secretly contains malicious QR-like code. Another script scans, extracts and runs the code using a known Internet Explorer vulnerability, then checks the machine again for packet capturing, sandboxing, VMs and other security-enhancing products. It also checks the graphics and security drivers to confirm it's running on an actual PC.
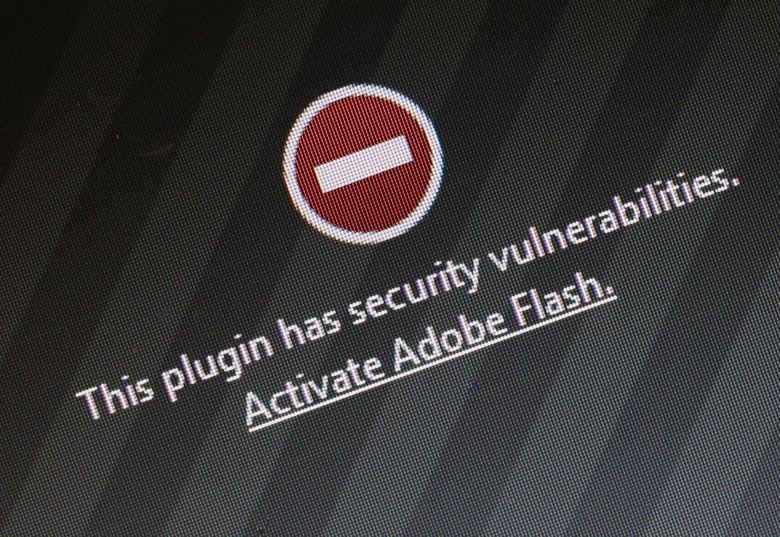
From there, it loads a 1-pixel iFrame off the screen and redirects via a TinyURL to a new exploit site. The landing page checks for the presence of Internet Explorer and loads a Flash file that contains another Flash file. The latter can serve up one of three exploits, depending on the version of Flash that it finds. To check, it passes information back to the server, encoded again as a GIF file. The server passes back a code to denote one of three Flash vulnerability exploits, along with the required password shell code to download the final payload.
It does yet another check for certain file types to ensure it's not being snooped on by a security analyst. If nothing is detected, the payload is downloaded and launched. From there, you can be infected with a backdoor, keylogger, screenshot maker and video maker. At that point, thieves can steal any file, and as mentioned, they've been targeting the banking sector and probing for weaknesses that would presumably allow them to steal or extort cash.
All of that seems pretty elaborate, but it apparently paid off. "The Stegano exploit kit has been trying to fly under the radar since at least 2014," the team says, and until now, no one spotted it (there's no word of any successful exploits, though). All of this could be avoided by by "running fully patched software and using a reliable, updated internet security solution," the Eset researchers say. (Eset sells just such a product, naturally.) And of course, by not using Internet Explorer in the first place.