The 'WannaCry' ransomware is a stark reminder of a broken system
Pointing fingers won’t keep the government from stockpiling and losing exploits.
In April, a hacking group called The Shadow Brokers dumped a cache of Windows' exploits it pilfered from the NSA. The group had decided to start leaking exploits it stole from the agency after it was unable to find a buyer for the government's hacking tools. Inside that April drop was a remote code execution vulnerability called "EternalBlue" (aka MS17-010). Fortunately, Microsoft issued a security patch that fixed EternalBlue in March. What's not so fortunate is that not everyone had applied it to their machines.
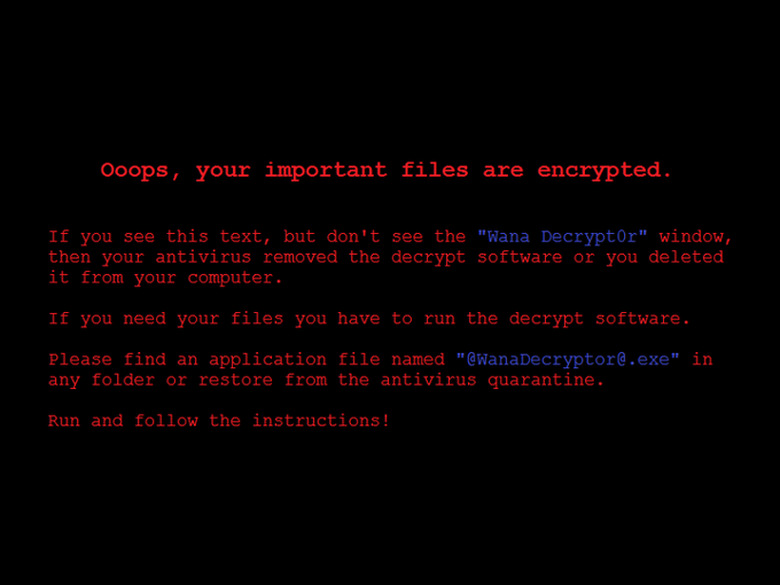
On May 12, many of those unpatched machines were exploited in the largest ransomware scheme ever seen. Computers at companies small and large displayed a message that their data had been encrypted and for $300 (sent via bitcoin) the owners of the machines could have their data back. The exploit works on Windows XP up through Windows Server 2012. And even though Microsoft issued a patch for newer systems, the computing giant ended support for Windows XP and 2000 back in 2010. In other words, if you have an old computer running legacy software, you're on your own.
The most disturbing of the ransomware attacks involved the UK's National Health Service (NHS). Patient data, including medical histories and test results, were caught up in a worldwide extortion racket. This — until recently, NSA-held exploit — has and will continue to wreak havoc on systems the world over and there's a good chance that in the future, we'll see similar situations and we'll once again be looking for someone to blame.
As quickly as news of the ransomware surfaced, people were looking to point the finger at someone. Some lashed out at the companies and hospitals for not applying the patch, others found fault with Microsoft. Of course, people were rightfully angry with the NSA for not disclosing the exploits in its possession and embarrassingly not being able to secure its own hacking tools.
While it's easy for someone with a couple computers in their house or a small company with a large IT budget to apply a security patch immediately, it's not that simple for large infrastructures — especially hospitals. As pointed out by the NHS, large, expensive medical devices like MRI machines still run Windows XP and can't be updated or easily replaced.
It's not just hardware that can be a roadblock to a secure system. Rolling out a software upgrade can take months for larger companies. Rolling out a new OS can take even longer. If you've ever updated your computer to find out that one of your critical apps no longer works, imagine that on a companywide scale.
Some smaller companies simply can't afford to buy the hardware needed to run the latest operating system. If your restaurant or shop is barely squeezing by financially each month, if the register or ordering system are working, why would you take the financial hit and upgrade to new hardware and untested software? It's unlikely a family diner that uses Windows 2000 for its food-ordering system has an IT department.
Microsoft, for its part, took heat for not issuing patches for legacy systems even though the company warned its users years ago that support was ending for XP and 2000. Security is tough. Companies like Microsoft and Apple are constantly trying to stay ahead of hackers. Sometimes they succeed; other times, not so much. There will never be a hacker-proof operating system, and the tech giants have to put resources toward what their customers are using right now instead of software that's decades old.
The reality is the government failed. The NSA, FBI and CIA will continue to stockpile and weaponize exploits. That's not going to end anytime soon. But the shoddy handling of these exploits and even its top-secret code-breaking systems is alarming. If you were wondering why Apple wasn't comfortable handing the Department of Justice encryption keys, this is one of the reasons why.
Even worse, the government refuses to take responsibility. Cybersecurity executive orders don't mean anything if the people who allowed this to happen are not held accountable. If a cache of military weapons had gone missing and they were used to hold up banks and businesses, there would be hell to pay. Essentially, this is the digital version of that.
There will always be groups like The Shadow Brokers and the team that created the ransomware that's crippled so many companies. But there are also hackers and researchers that are working hard to keep our systems running. In the middle are the rest of us just trying to get our work done.
The system is broken from top to bottom, and there's no indication it'll be fixed anytime soon. We need to not only practice good security (regular system backups, not using the same password, using two-factor authentication, not clicking on email links, applying security patches), we also need to help friends and family that might not be as digitally-savvy.
While you're helping others out, remember that you're not alone. Researcher MalwareTech found a flaw in the current variant of WannaCry that accidentally stopped it from launching on new computers by registering the website URL the exploit was pinging. Once he had control of the site, WannaCry's computer takeover and encryption process stopped.
But the flaw has already been fixed, and a new variant of WannaCry is out there extorting cash from unsuspecting Windows users. So if you can, patch your system. But it you can't, be careful and ask for help. Increasingly, it's on us to protect our data, and while the government can talk a big cybersecurity game, it's not doing us any favors.