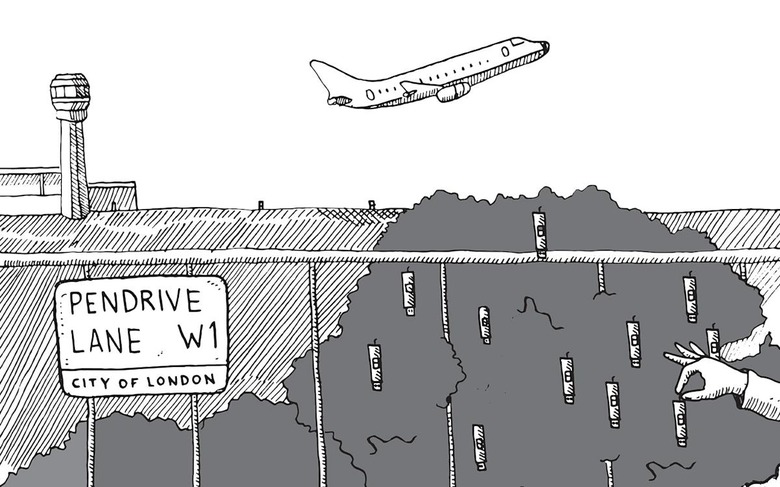
Critical Heathrow Airport security files found in the bushes
Competent security doesn’t grow on trees.
When you're unemployed, you tend to notice the world around you a bit more than the average working stiff. That's how a regular, unemployed fellow in London happened to find intimate and detailed security protocols and maps for London's main airport, Heathrow, lying on the ground in broad daylight
The unnamed man noticed a USB stick in a row of bushes lining the sidewalk on Ilbert Street, along Queen's Park, in West London, so he grabbed it. It wasn't exactly outside the airport's security offices. That's eighteen miles from the airport, or about 40 minutes by car.
Most people hip to day-to-day computer security practices know that you should never, ever plug a random USB stick into any device you care about. Maybe that's why he didn't check it out right away. He hung on to it for a few days, thinking little of it before popping it into a public computer at the library when he logged on to look for work.
To what we can only guess was his horror-and-surprise, he discovered the unencrypted, password-free thumb drive held 2.5GB of data evidently belonging to Heathrow Airport's highest level security team.
Rather than take it to the police, he opted to hand the USB stick over to press — the tabloid paper Sunday Mirror. The Mirror promptly reported that the little drive contained 76 folders comprised of around 200 documents, maps, videos, timetables for anti-terrorism patrons, and much more, tediously compiled and with information across numerous different systems.
The Mirror wrote that it held:
- The exact route the Queen takes when using the airport and security measures used to protect her.
- Files disclosing every type of ID needed – even those used by covert cops – to access restricted areas.
- A timetable of patrols that was used to guard the site against suicide bombers and terror attacks.
- Maps pinpointing CCTV cameras and a network of tunnels and escape shafts linked to the Heathrow Express.
- Routes and safeguards for Cabinet ministers and foreign dignitaries.
- Details of the ultrasound radar system used to scan runways and the perimeter fence.
To anyone working in security, this is a disastrous data set to suddenly discover is out in the wild, for an unknown amount of time, and in unknown hands. Especially at a time when officials have just stated that "Britain is facing its most severe ever terrorist threat." Right now the UK is on a terror alert at the level of "severe" — down from "critical" — after the September 17 Parsons Green tube bombing terror attack.
The Mirror reported that the London Metropolitan Police were working with airport officials to figure out how the USB stick and its information ended up physically exfiltrated from Heathrow and tossed in the bushes along an unremarkable street in London.
Of course, our first thoughts are that it was terrorists. But in the realm of all things security, it's also possible that it was the work of errorists. Maybe they're used to this sort of thing in the UK, though we are now too. Over here in the US, we're running out of digits to count the number of times our government security secrets have ended up on a contractor's computer, were promptly stolen, and then ended up "in the wild" where they've been used for all kinds of harm and completely avoidable stupidity.
This stuff keeps ending up on security contractor's computers because when we say "ended up on a contractor's computer" what we really mean is that some hacker working for Booz Allen or whoever did that thing that hackers do: They hoard. I've often thought there should be a version of "Hoarders" just for hackers, until I realized that was what was in the headlines every day anyway, and it would end up being too depressing.
It wouldn't be depressing just because our security is a grade-A disaster, or because I believe every kind of hacker — white hat, black hat, grey hat, whatever nacho-flavored hat — has compulsively sticky fingers. It would be depressing because hackers are often crap at their own personal security. They will correct you, talk down to you, call users stupid every minute of the day, but it's by and large a culture of not practicing what they preach for various reasons. If you doubt me, just look at how many of them get caught.
The point is, secrets are like catnip to hackers, and the feeling of power makes them sloppy. But oh, do they hoard. The hoarding is also functional: With employment and getting gigs, he who has the most vulns, wins. So if the USB stick with all the Queen's secrets (literally) about Heathrow Airport ended up falling out of some red teamer or physical pentester's pocket on a random street in London, bouncing into the bushes after being hired to do a security assessment on the airport, it's not going to be a surprise. To me, anyway.
In a follow up Wednesday, International Airport Review reported that a meeting of the House of Commons Transport Committee was held on Monday in an attempt to find out what the hell was going on. In it, Heathrow's Chief Executive John Holland-Kaye was asked what he knew about the USB stick, and what the airport was doing in its official capacity to investigate.
Holland-Kaye began with the usual verbal sleight of hand we hear from every business and organization that gets pwned, namely, that they take security very seriously. Once that commercial for nothing was over, he acknowledged that the Metropolitan Police were assisting with their investigation in addition to "setting up an independent internal enquiry."
"From the information I have seen that was on the USB stick and reported in the papers," he said, "there was nothing there that causes us any security concerns. From what I have seen, Heathrow is completely secure." Was he even worried? Maybe, or maybe not. Holland-Kaye added that they "will be reviewing that with a critical eye to see that if there are any procedures to be changed they are changed quickly to ensure that we stay ahead of the game."
It's not the most reassuring statement, to be certain. But in an era of things somehow able to only get almost comedically worse, like having your fire extinguisher catch on fire while putting out a fire, let's hope the somewhere in West London there's a pentester watching all this in the news and just feeling really, really embarrassed.