spying
Latest

Messaging app ToTok is reportedly a spying tool for the UAE
It's no secret that some messaging apps are favored by authoritarians, but one app may be explicitly designed with spying in mind. Unnamed US officials speaking to the New York Times say that the chat app ToTok is believed to be a surveillance tool for the United Arab Emirates. According to a classified intelligence report, the UAE uses ToTok to follow users' conversations, track locations (under the guise of weather), determine social connections and look at media. Most of the app's million of users live in the UAE, but it's popular elsewhere in the world and has seen a surge of demand in the US.

Former Apple exec claims the company spied on his text messages
A former Apple executive is claiming the company spied on his text messages before suing him. In February, Gerard Williams III, who spent almost 10 years working on mobile device chips at Apple, left the company. The same month, he joined NuVia Inc -- a company founded to develop processors for data centers -- with several other Apple developers. In August, Apple sued Williams for breach of contract. Now, Williams is disputing the lawsuit and claims Apple illegally snooped on his texts and phone records.

Commerce Department extends Huawei license for another 90 days
In May, the Trump administration essentially banned the purchase and sale of Huawei products on a temporary basis. The emergency measure was meant to stem concerns that the company provides intelligence or backdoor access to the Chinese government while US agencies investigate the allegations. Organizations that wanted an exemption to this had to apply for what's called a Temporary General License, or TGL. The latest extension of the TGL was scheduled to expire today, but the Department of Commerce announced a 90-day extension this morning.

Former Twitter employees charged with spying for Saudi Arabia
Federal law enforcement is taking action against former Twitter workers who allegedly spied for Saudi Arabia. The Justice Department has charged Ali Alzabarah (the one whose activities first surfaced) and Ahmad Abouammo with using their combined access to monitor Twitter accounts on behalf of the Saudi government. Abouammmo, an American citizen, reportedly snooped on three accounts that included one revealing inner details of Saudi leadership. Alzabarah, a Saudi citizen, is alleged to have obtained personal info for more than 6,000 accounts, including that of high-profile dissident (and Jamal Khashoggi ally) Omar Abdulaziz.

Interior Department grounds drone fleet over security concerns
The US Department of the Interior has halted the use of its 800 drones, which help monitor endangered species, inspect federally protected land and fight forest fires. According to The Wall Street Journal, Interior Secretary David Bernhardt called for the fleet to be grounded this week due to concerns that the drones enable the Chinese government to spy on users. The units will remain unused, save for any emergency situations, until potential security risks are fully reviewed.

Russia reportedly breached encrypted FBI comms in 2010
When the Obama administration kicked out Russian operatives and seized compounds, it might have been for more than their meddling in the 2016 presidential election. Unnamed officials talking to Yahoo News say that some of those diplomats were involved in a counterintelligence strategy that breached FBI communications starting in 2010. Reportedly, the Russians had "dramatically improved" their decryption of some secure comms technology, including the radios used by mobile surveillance teams and the push-to-talk cellphones used as backups. The Russians could track and intercept the chats between agents, though it's not clear if that was possible in real-time.

US Senators ask the FCC to review licenses with China-owned telecoms
Two US Senators want the Federal Communications Commission (FCC) to review whether two Chinese state-owned telecoms should be permitted to operate in the US. In a letter to the FCC, Democratic leader Senator Chuck Schumer (D-New York) and Senator Tom Cotton (R-Arkansas) ask the Commission to review licenses that give China Telecom and China Unicom the right to use networks in the US. According to The New York Times, the Senators are concerned that the companies may use that access to carry out espionage.
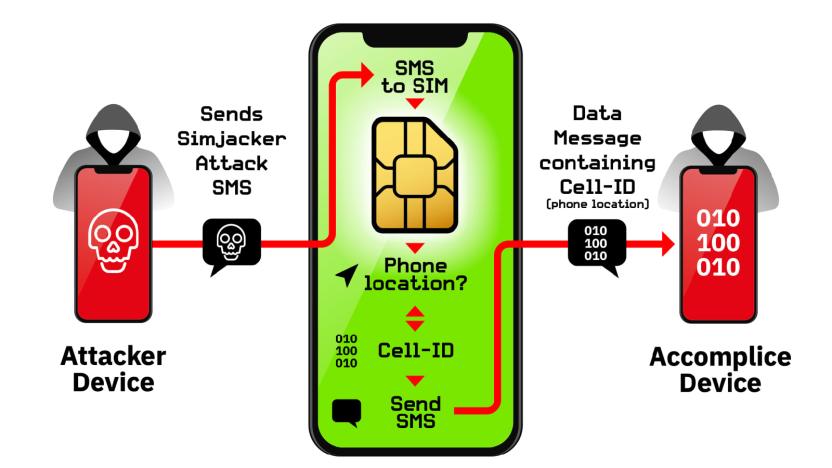
SIM-based attack has been used to spy on people for two years
In a few cases,your SIM card may pose more of a security risk than your phone's software. AdaptiveMobile Security researchers say they've discovered a new vulnerability, nicknamed Simjacker, that's being used to surveil people's devices by an unnamed surveillance company. The technique sends SMS messages containing instructions for an old S@T Browser app supported on some carriers' SIM cards. Where S@T was originally intended to launch browsers, play sounds or otherwise trigger common actions on phones, Simjacker uses it to obtain location info and IMEI numbers that are later sent to an "accomplice device" (again using SMS) that records the data.

Huawei boss is willing to license 5G tech to ease spying fears
Huawei's CEO Ren Zhengfei said the company is willing to help boost a western rival in the global 5G race as a way to ease tensions with the West. In a recent interview, Ren told The Economist Huawei would give another company "perpetual access" to its existing 5G patents, code and technical blueprints in return for a one-time fee.

Huawei allegedly developed a spy-friendly phone network for North Korea
If Huawei was hoping to mend its reputation in the wake of the de facto US ban, it's about to be disappointed. The Washington Post and 38 North have published joint reports indicating that Huawei helped build Koryolink, North Korea's highly restrictive cellphone network that went live in 2008. According to documents, Huawei partnered with China's state-owned Panda International Information Technology on projects in North Korea for at least eight years, with cooperation starting when then-dictator Kim Jong Il visited Huawei's headquarters in 2006. Huawei provided elements like cellular infrastructure, network management and encryption, while Panda provided software and transported Huawei gear.

Hackers broke into a contractor for Russia's spy agency
The Russian government has been linked to a number of high-profile hacks, but it just became a target -- and the data that was stolen says a lot about its apparent goals. A hacking group nicknaming itself 0v1ru$ infiltrated the servers of SyTech, a contractor for the FSB intelligence agency on July 13th. They compromised the firm's Active Directory server and stole 7.5TB of data. The intruders revealed a number of projects that SyTech had been working on for the FSB (and fellow contractor Quantum) since 2009, some of which were pure research while others came to fruition.

Government hackers reportedly broke into Russian search company Yandex
According to a Reuters report, hackers working for Western intelligence agencies reportedly broke into Yandex, the company often referred to as "Russia's Google." The hackers were allegedly looking for technical information that would indicate how Yandex authenticates user accounts. That information could help a spy agency impersonate Yandex users and obtain access to their private messages.

WhatsApp call exploit let attackers slip spyware on to phones
WhatsApp appears to have been the inadvertent conduit for a surveillance campaign. Both WhatsApp and Israeli software developer NSO Group have confirmed that an exploit in WhatsApp's voice calling allowed attackers to load NSO's Pegasus spyware on to Android and iOS devices. The tool could infect a device even if a user didn't answer, and the malicious calls would frequently disappear from logs. Pegasus can use the camera and mic in addition to scooping up location and message info.

Warrantless searches of Americans’ data spiked 28 percent in 2018
An annual transparency report published by the Office of the Director of National Intelligence shows warrantless searches of Americans' data jumped 28 percent in 2018. According to the report, the National Security Agency (NSA) conducted 9,637 warrantless search queries of Americans' calls, texts, and emails in 2018. That's up from 7,512 searches in 2017, and it's more than double the 4,672 warrantless searches the NSA made in 2015.
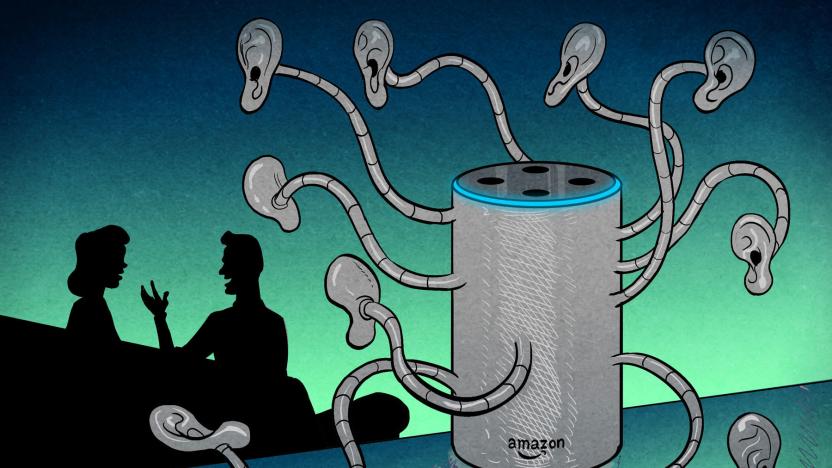
Hey Alexa: How can we escape surveillance capitalism?
Where do you go when you want to escape surveillance? When you want to stop feeling like you might be being listened to by microphones, or watched through surveillance cameras, or tracked by invisible tech gremlins burrowed within devices. Certainly nowhere in public. Perhaps it's your car. Maybe it's your home. Or even your bedroom? For some readers, that perimeter of personal freedom likely shrunk in February when news broke that Google "forgot" to tell consumers its Nest Secure came with a built-in microphone.
The NSA says it's time to drop its massive phone-surveillance program
The National Security Agency (NSA) has formally recommended that the White House drop the phone surveillance program that collects information about millions of US phone calls and text messages. The Wall Street Journal reports that people familiar with the matter say the logistical and legal burdens of maintaining the program outweigh any intelligence benefits it brings.

CIA claims Huawei is funded by Chinese state security
The US has rattled its saber more than once trying to deter countries from using Huawei technology, but it hasn't publicly disclosed much of what it's worried about. You might have a better insight after today, though. A source speaking to The Times claims that the CIA has told UK intelligence officials that Huawei has received funding from Chinese state security, including the People's Liberation Army, the National Security Commission and a "third branch" of China's state intelligence network. The CIA told the UK and the other Five Eyes nations (Australia, Canada and New Zealand) about its beliefs earlier in 2019, according to the source.

Germany may use Huawei hardware for its 5G networks
The UK isn't the only country skeptical of American hostility toward Huawei over spying fears. German officials talking to the Wall Street Journal say the country has made a "preliminary decision" to let Huawei bid on contracts for 5G networking despite US pressure to ban the Chinese company. A cybersecurity agency investigation didn't show evidence that Huawei could steal data through its wireless equipment, the officials said, even though the country had US help. It also couldn't find proof that Huawei had done anything wrong, and conversations with the US and UK over potential security holes were ultimately "inconclusive."

UK believes it doesn't need to ban Huawei from 5G networks
The US may have had some success in persuading allies to ban Huawei equipment from their 5G networks, but not everyone is convinced there's an existential threat. Financial Times sources claim the UK's National Cyber Security Centre has found that it can limit the risks of using Huawei gear in 5G deployments without banning it entirely. This could include using a variety of suppliers and restricting some parts of 5G networks.

Chinese surveillance company found tracking 2.5 million people
Security vulnerabilities are horrible, but one of them is shedding light on the reach of the Chinese surveillance state. Security researcher Victor Gevers discovered that facial recognition firm SenseNets left a surveillance database completely exposed, revealing that it has been tracking over 2.5 million people in the western province of Xinjiang, where China has targeted Uighur Muslims. The company has been holding on to personally identifying info (such as names and ID card numbers) as well as an extensive amount of location info, including 6.7 million data points tagged with names (such as "mosque" and "hotel") gathered inside of 24 hours.





