Developer warns against using in-app browsers due to keylogging potential
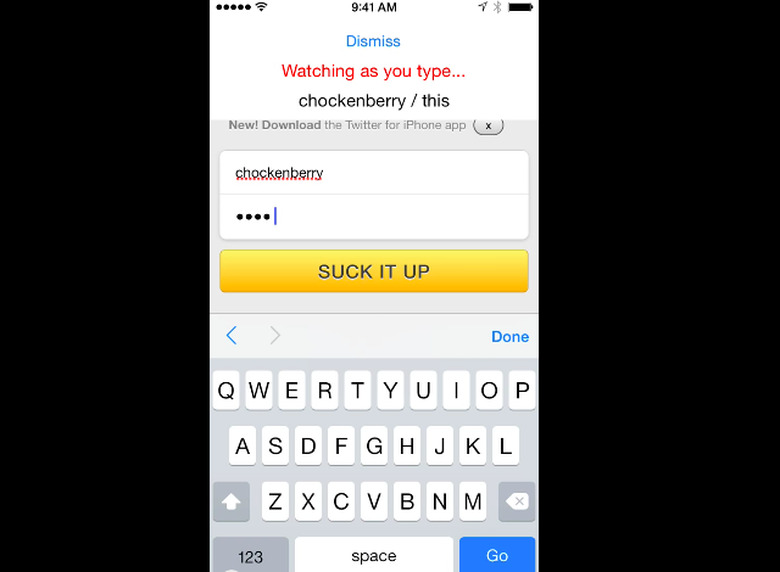
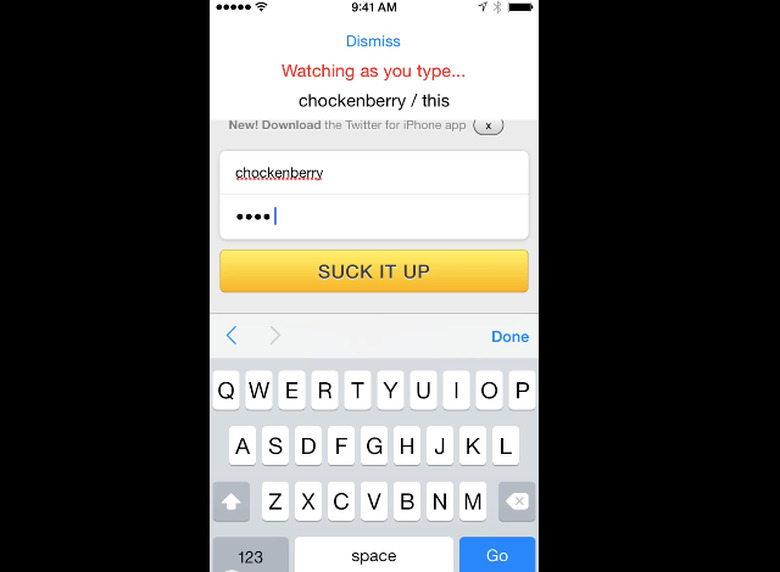
Well-known Iconfactory developer Craig Hockenberry is warning iOS device owners about the risks of using in-app browsers to enter sensitive information such as account login credentials. Users commonly encounter these browsers in social media apps that require them to login into a website in order to give an app permission to access their account. According to Hockenberry, these apps could be exploiting a vulnerability within the in-app browser system to eavesdrop on typing and steal sensitive username and password information.
Hockenberry demonstrates this vulnerability in the video embedded below and points out this hole is not easy to fix because it involves the interaction of web page JavaScript with UIWebview in iOS. The only practical way to protect users from this keylogging is to stop using the in-app browser for authentication and instead launch iOS mobile Safari when the entry of sensitive information is required by an app.
Unfortunately, Apple is rejecting apps that redirect users to Safari for authentication because the company believes it is too cumbersome and confusing to switch a user to Safari. Iconfactory's own Twitterrific app was forced to removed the safer Safari authentication scheme and replace it with the in-app browser method due to Apple's App Store review guidelines.
Twitterrific developers said they won't collect private information from these in-app browser session, but there is no guarantee other apps will adhere to this same policy and little chance Apple's already overloaded review process will detect these rogue apps. Consequently, iOS users need to be aware of this vulnerability as nefarious apps potentially can gather login information for more than just authentication purposes.