Google Apps bug exposed personal data of nearly 283,000 website owners
According to a cadre of Cisco security researchers (via Ars Technica), a Google Apps bug inadvertently caused nearly 283,000 WHOIS registration records — which can include the domain owner's name, address and other contact information — to be made public even though those owners expressly wanted that data to stay private. Erm, oops. If you were one of the people affected by this accidental dose of transparency, Google should have already contacted you, and the search giant also says that the issue that caused this whole mess has already been closed.
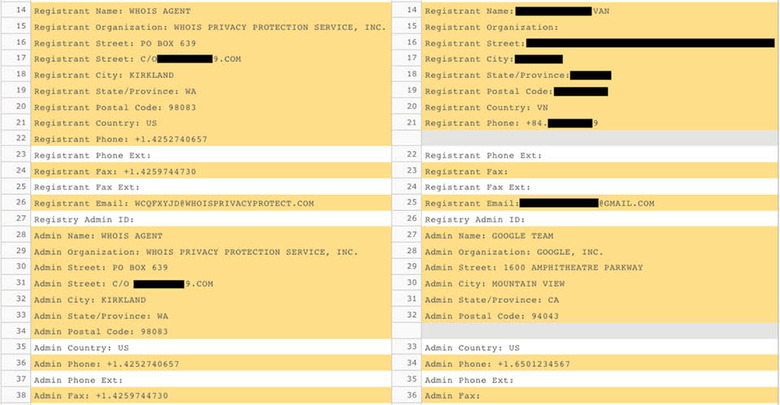
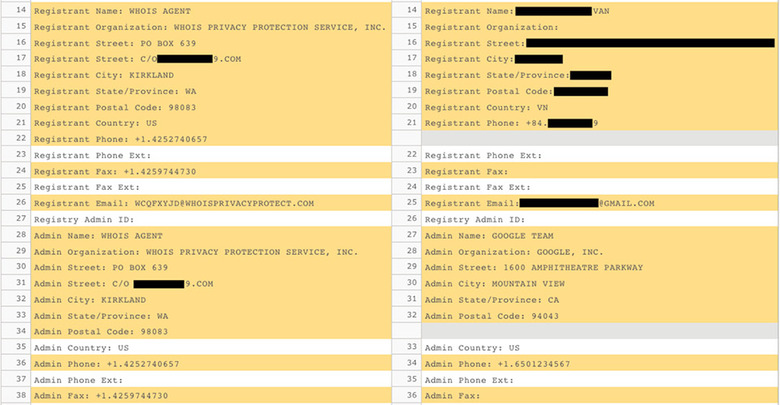
Here's how it all went down: If you wanted to get set up with Google Apps for Work and registered a domain name through Google (and its registrar partner eNom) back in 2012, you had the option of paying an extra $6 a year to keep your website's WHOIS information obscured. Thing is, thanks to a flaw in how Google's systems worked with eNom's, that hidden registration feature wouldn't automatically re-up itself if you renewed your domain name for another year. Yeah, that's right: Those affected had their WHOIS privacy for a year, but that's it. That's not to say that all 283,000 people just had their identities revealed to anyone who cared to look; plenty of people register their domain names with false information.
The Internet Corporation for Assigned Names and Number (or ICANN, to the rest of us) mandates that all of the information you supply during the registration be valid, which can come in handy if an ownership or trademark dispute flares up. Granted, filling out a web form with phony info seems like less of a factor when these people have already decided to pay an annual pittance for opacity, but some people might have made it through this ordeal mostly scot-free.
The rest of the pack would do well to keep on their toes. Quoth Cisco:
The obvious risk here is that some of these individuals who have been unmasked may now be in some form of danger as a result of their connection with the domain registration. Additionally, threat actors may use domain registration information for malicious purposes. For example, sending targeted spear phish emails containing the victim's name, address, and phone number to make the phish seem even more authentic. As eNom points out, identify theft is also a possibility. To best protect themselves users are urged to adopt safe browsing habits and make use of layered defenses like antivirus and antispam technology.
UPDATE: Google has sent along a statement on the matter reiterating some of what we already knew, specifically that the issue has been closed and that it's reaching out to affected parties.
"A security researcher recently reported a defect via our Vulnerability Rewards Program affecting Google Apps' integration with the Enom domain registration API. We identified the root cause, made the appropriate fixes, and we're communicating with affected Apps customers. We apologize for any issues this may have caused."