'Logjam' browser vulnerability fix will block thousands of websites
Researchers have discovered a new browser and website encryption vulnerability called Logjam, and there's good news and bad news. On the plus side, the vulnerability has largely been patched thanks to consultation with tech companies like Google, and updates are available now or coming soon for Chrome, Firefox and other browsers. The bad news is that the fix rendered many sites unreachable, including the main website at the University of Michigan, which is home to many of the researchers that found the security hole. Ironically, that site (which has since been patched) and other government and educational sites are supposed to be secure — so what went wrong?
@InertialLemon @csoghoian Spent the past few weeks doing multivendor disclosure, coordinated by Google.
— Matthew Green (@matthew_d_green) May 20, 2015
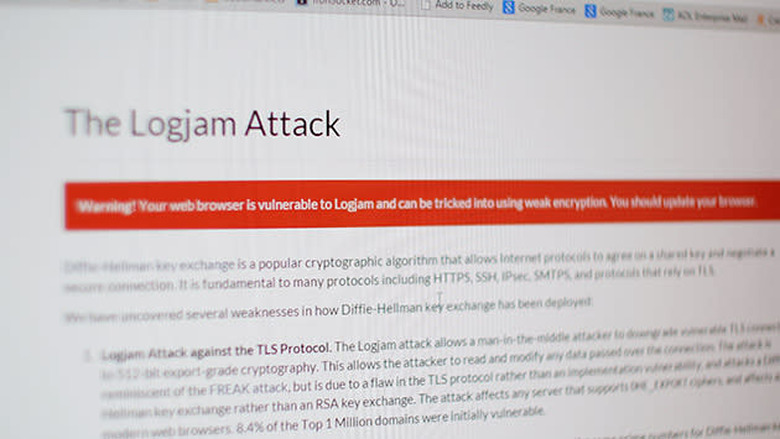
The Logjam vulnerability is a kissing cousin to FREAK, a weakness that also left secure sites like Whitehouse.gov open to attack. Researchers say the new bug's weakness is in an encryption protocol called Diffie-Hellman, letting attackers downgrade certain connections to a mere 512-bits of security. That's low enough to be easily be cracked by sophisticated attackers in just a few minutes, though it's not clear if anyone actually exploited the weakness. However, the researchers speculated that none other than the NSA used Logjam, saying "a close reading of published NSA leaks shows that the agency's attacks on VPNs are consistent with having achieved such a break." However, one of them pointed out that such a hack was "just conjecture."
@RichFelker The ability to passively eavesdrop on 1024 is just conjecture. It seems feasible for the NSA and consistent w the Snowden docs.
— Matthew Green (@matthew_d_green) May 20, 2015
So what to do? If you're an admin or the owner of a web or mail server, you'll want to check the researchers' guide to fixing it, which involves changing Diffie-Hellman cipher settings. If you just want to surf safely, check that you have the latest version of your browser installed — Google Chrome, Mozilla Firefox, Microsoft Internet Explorer and Apple Safari are all releasing patches.