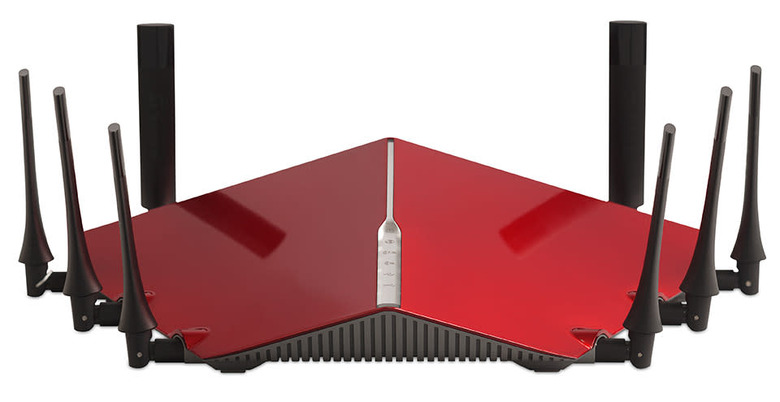
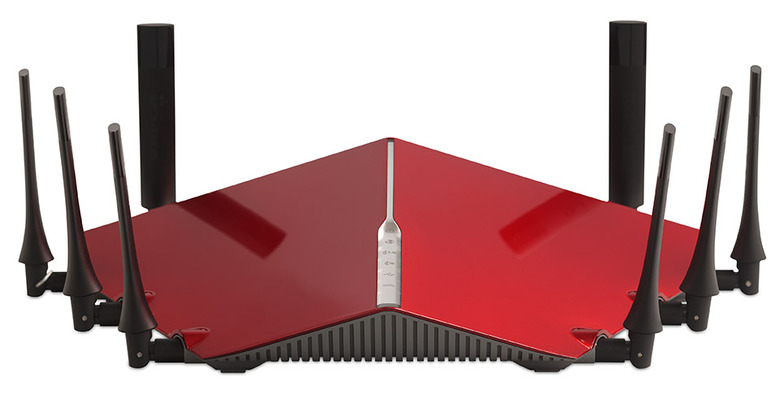
Leaked D-Link code-signing key could make malware look legit
When your company is known for making wireless routers, network switches and home security cameras, leaking your code-signing private keys yourself is the last thing you want to do. Back in February, that's exactly what D-Link did, accidentally leaving a valid key visible in its open-source firmware. If found by an attacker, the key could have been used to make malware that can pass as official software from D-Link — malware that wouldn't trigger security warnings when installed to Windows or OS X machines.
That's bad, but luckily would-be attackers would have had to stumble across the key weeks ago — the leaked certificate expired earlier this month. Still, that means software created using the key between February and September is still valid. D-Link says it's issuing more firmware updates in the near future to address the issue