FBI: Yes, we exploit unpatched security holes
An FBI director admits that the bureau uses zero-day exploits to snoop on targets.
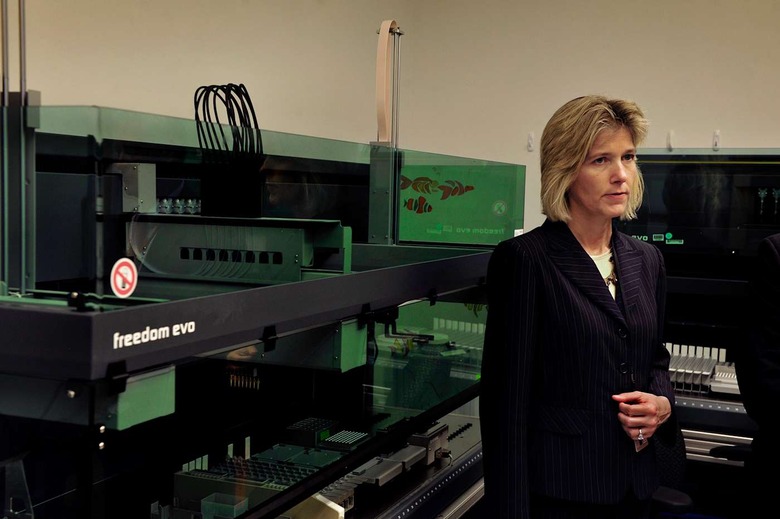
It's no secret that the FBI uses tech tools like Stingray phone trackers to investigate suspects, but it's now clear that the bureau is willing to go even further than that. Operational Technology Division lead Amy Hess (above) tells the Washington Post that the FBI uses zero-day (that is, unknown by vendors) security software exploits for investigations — the first time any official has admitted this on the record. The outfit doesn't prefer to use these hacks given how short-lived they are, Hess says, but they're still on the table.
She also elaborates on the FBI's policy around revealing Stingray use. The bureau doesn't ask police to deny using Stingrays in the first place, Hess claims... it just doesn't want them explaining the exact functionality in public. Investigators can detail things to judges in private sessions if there are any questions, although this isn't going to be very reassuring if you're caught by one of these surveillance sites.
Hess is quick to admit that the zero-day attacks are problematic: the FBI has to strike a balance between catching possible criminals and responsible disclosures that protect the public. However, there are concerns about whether or not it's making the best choices. After all, this is the same outfit pushing for backdoor access that, in practice, would likely leave everyone vulnerable. While the FBI may be thinking carefully before compromising someone's device, it may not end up making the right call.
[Image credit: Michael S. Williamson/The Washington Post via Getty Images]