The Gamble on Privacy, Transparency and Trust
Part Three in a series looking at how to solve the problem of invasive government surveillance. Click here to read the other parts of this post on Engadget: Part One,Part Two or Part Four
Once we fully understand where we stand on our notion of privacy, we can finally begin to build policy which all sides can agree upon. Crucially, as much of the States power and necessities for effective law enforcement rely on a modicum of secrecy, there must be trust between the electorate, the executive, the judiciary and those who seek to enforce the laws enacted by the two. Trust in this relationship is key, as Dennis Frank Thompson has so succinctly put it, "Citizens have a right to insist, as the price of trust in a democracy, that officials not give reason to doubt their trustworthiness."
And boy have they given reason to doubt.
%VIRTUAL-YouTubeEmbed-xT0yRXWo6UU%
To acquire this trust once again, it is imperative that the executive provide accountability and a measure of transparency to their surveillance operations. An idea pioneered by Co-Director of the Harvard Library Innovation Lab at Harvard Law School,David Weinberger and echoed by others in the journalism community from NYU professor of journalism and media critic Jay Rosen,Director of Interactive Journalism at the City University of New York Graduate School of Journalism Jeff Jarvis and even the now infamous Intercept & Guardian journalist Glenn Greenwald, is that, in the fourth estate now: "transparency is the new objectivity." I would argue that transparency may also be both the new public accountability and basis for legitimacy, in politics. Both sets of logic reside in their ability to communicate trust to those whom they are affecting, rather than relying upon a moral notion of assumed trust between parties simply due to hierarchy and voting power. Since we have come to find ourselves untrusting of the State here, that assumed trust is no more, yet trust between parties across the divide is completely necessary for the continuation of a status quo whereby the State continues to provide for its citizens safety and the public continues its use of the internet in roughly the same manner it does today.
That the State continues to provide for its citizens safety is in essence, the end goal of any legislation. The caveat is, that it should not come at any cost. Somewhere in there lies the question of how effective the law needs to be in order to provide this safety. Lawrence Lessig, who many know for his work on copyright reform, money in politics and net neutrality, has discussed the arbitrary notion that the law is a set of binary rulings, instead stating that "The law need not be completely effective in order to be adequately effective", something which David Anderson echoed in his interview with BBC's Law in Action when he stated that "there is only so much we can do with the law, because we do have a lot of very strong counterterrorism laws" and that "in a free country, with relatively open borders, you are not going to stop everybody."
If we know both this, and the fact that eventual failure of any network security is inevitable to be true, even the notion of a legal dragnet surveillance network capable of providing 100% security seems to be a fallacy. When you add in the fact that the perpetrators of many of our latest terror atrocities, including Lee Rigby's murderer and the Charlie Hebdo shooters "were already on the radar of the British and French intelligence services, but they decided to stop monitoring them because of lack of resources"; spinning the idea to the public that with even greater powers capable of infringing on the public privacy, they could prevent the next attack would seem to be an increasingly difficult spin to achieve.
Anderson himself still recommends bulk collection, especially outside of a domestic context, (technical difficulties aside) but inserts a further layer of judicial review to provide the necessary transparency.
Firstly, authorisation of a warrant for surveillance would be taken away from the small pool of ministers who can currently sign off on them, and instead be handed to a set of independent judicial commissioners. As a great majority of warrants are issued for police use in serious crimes; drugs, firearms and trafficking rather than in espionage or counter-terrorism, it is logical to give the decision to a judge, who by professional default, has a much more thorough understanding of policing, crime and how to put a case together properly than a career politician. This firstly takes suspicion away from decisions made by often inexperienced ministers and provides the 'ability to respond quickly and effectively to threats of national security or serious crime', by doing away with the need to busy up the schedule of a Home Secretary with warrant signings.
Secondly, on the issue of national security, Anderson does accept that the judiciary does not, or very rarely plays a part in shaping foreign policy, or what the executive would label as important to national security. Here, Anderson admits that where a warrant is sought on this basis, the decision must lay with the executive, and that we must trust the judicial commissioners to understand this line, and the limits of their knowledge and responsibility.
Asking some of the most intelligent people in the country whose job it is to literally be fair, to get in on this debate, is some of the most sound advice I've ever heard.
Thirdly though, and key to this, Anderson seeks the oversight of a judicial commission, as most people will never know that a warrant has been obtained because British courts do not allow intercepts to be admitted into evidence, providing no judicial redress after the event, therefore, begging the need of it beforehand. But this lack of legal recourse after the fact is a huge achilles heel in the strive for transparency and trust. It still leaves a system which can be abused, whereby judges can be strong-armed, convinced or simply over-ruled by the executive into issuing vaguely written warrants, legalising the exact sort of dragnet surveillance the public is trying to avoid, and covering its tracks by public in-admission in courts. All Anderson is suggesting really is adding another layer of red tape, in which already rich judges, get more well paid jobs at the behest of the British tax-payer to continue a status-quo that nobody wanted in the first place.
(On the question as to whether handing power to an unelected official makes the system less democratic, Anderson states that where interception has been conducted, politicians can never be held to account anyway because it's illegal to disclose when interception has been conducted, and that the government never confirms or denies intelligence matters relating to the fact.)
For this reason, you have to return to the notion of providing Lessig's "adequately effective" legislation. Law enforcement and those who seek to break the law are, and always will be in an endless game of cat and mouse. The whole point of a dragnet surveillance is to limit the possibility of crimes being perpetrated, but whilst crime numbers don't seem to have taken a drastic hitcompared to previous years, public trust in government and their own perception of privacy certainly has.
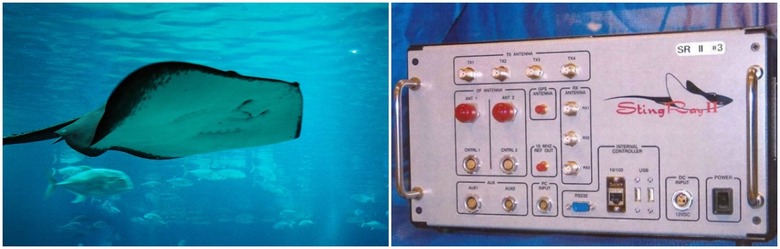
When Daniel Rigmaiden was caught filing fraudulent tax reports in California, he eventually discerned that he had been caught through the usage of a 'Stingray' device, something the police would use to fake a cell tower signal, connect to your phone and access your data. However, as Anderson has stated, the way this evidence was acquired was never submitted into evidence and it seems the FBI and US government refused to allow any mention of the device in a court, effectively forcing States to drop cases where they could not put a prosecution together without the evidence gleaned from the device. It has since come out that these devices are also in widespread use within the UK.
When you have law enforcement utilising devices which passively access data on every single mobile phone within their radio radius in order to surveil just the one device, and when the fruits of that surveillance prove to be the only useful evidence in prosecuting a now known criminal; barring the police from bringing that criminal to justice in order to keep such a device secret certainly defeats the object.
Left: Police Cell-Tower Device used to capture Daniel Rigmaiden. —Right: Deadly cartilaginous fish which caused the death of Steve Irwin.
Where our nation's security services have backdoored social networks through PRISM in order to acquire data we believed to be private without allowing the company in question to perform as the necessary intermediary for governmental requests, or even forced them to divulge personal data without letting their users know. Where it is supposed they have completely compromised ISP's and the Tor network to pinpoint individuals complicit in deep-web crimes and where lately, UK police have scanned the faces of thousands of festival goers; having this evidence inadmissible in court on the basis that the State distrusts both the law-abiding public and those with criminal intent with knowing its abilities to safeguard its citizens, definitely straddles the borders of democracy, and certainly gives you a sense of the regard those in power have for those they now subjugate.
I would argue that having this information come to light in a court would probably not have the long lasting implications law enforcement, or security services are afraid of. Following the facial scanning at Download Festival, police stated that faces were only being matched against those of known criminals and that any further data acquired was destroyed afterwards. Would the Stingray have been made public and had law enforcement openly opted for the same data retention strategy, I imagine public distrust would not be as high relating to the device's use as it is now. Would this lead to criminals opting for other methods of communication or using evasive techniques to hide dominant facial features? Perhaps, but did (intelligent) criminals use Facebook Messenger or WhatsApp to organise their heists before Snowden? At some point, asking a criminal to go the extra mile and do the legwork on a extra set of 10–20 surveillance efforts before the fact, will deter them and cost less to society and law enforcement than performing timely and costly surveillance on a suspect and arresting them after catching them in the act having not put the legwork into avoiding surveillance they didn't know about. This is cat and mouse. This is law that is adequately effective.
Obviously, there should be no safe haven for criminals. As Anderson states, "no channels should be immune from interception" but the circumstances under which they could be intercepted should be open, properly regulated and upon fair request, services should be obliged to hand over incriminating details.
However, this isn't me saying I'm for any sort of governmental criminalisation of encryption or stifling of innovation when it comes to providing private services. Encryption and cryptography are integral to building trust on the network, and are incredibly important in avoiding a large majority of the potential and inevitable breaches, along with, you know, keeping our banks running.
In a cat and mouse system, the onus is on the cat to catch the mouse. However, if we only encourage a 'Digital Proletariat' uptake in heavily encrypted anonymising practises such as Tor browsing, secure VPN's with no IP logging, hardware proxies, blockchain payments for online goods and encrypted PGP communications, without allowing for those means to be legally intercepted, we are not contributing to the solution of the problem of the surveillance State. Whilst for now, many of these seem uncrackable until we invent quantum computing, in the long run, we will only be exacerbating the problem once these avenues have been thoroughly cracked and are no longer safe. And when/if that time does come, we will be all the better placed to deal with it if we get our policy correct now.
"if there is an app which Paedophiles and Terrorists know they can use without slightest possibility of detection, you are subverting the rule of law, and you are letting the bad guys win... it doesn't mean it should be easy for State to read information they really want, but potential has to be there." David Anderson, QC
(On the point of suspicion rising from online surveillance: There are few crimes which reside entirely hidden online. Hate speech is public by nature. Cyber-bullying obviously has at least one witness & the sale of drugs has a physical illegal market on both ends. Other deep-web criminal services such as Ransomware & hacking are sophisticated enough crimes that I imagine their perpetrators understood the risks of sophisticated online surveillance to a degree which would render the usefulness of it pointless.)
To know you may be surveilled and that there is no channel upon which you will be immune from interception provides you with avenues for and the freedom to pursue legal recourse, but to know you are not being surveilled as the norm provides you with integrity and privacy. Implementing a transparent judicial review for legal interception based on warranted particularised suspicion, liaising with the companies which provide private service to the suspect and making the suspect, and public aware of the full extent of the surveillance conducted towards them after its conclusion regardless of whether a guilty act was perpetrated or not provides the electorate with trust, the state with accountability and law enforcement with ample capability to do their job.
Click here for Part Four: 'Balancing policy with network management in the UK'