Set up your own Stingray cell dragnet with these leaked docs
Manuals and documents detail how the phone-intercepting networks function.
The Stingray has been a controversial tool that police departments and government agencies have used to track mobile phone locations and monitor the metadata they send to cell towers. Its maker Harris Corporation has repeatedly denied requests to explain its inner workings, citing terrorist and criminal security concerns despite their frequent use without warrants. But The Intercept has acquired over 200 pages of documentation detailing several communication-intercepting setups of the company's hardware and software.
We've known the basics of how devices like the Stingray work: By impersonating cell towers, they force phones to relay information through them, tracking individual phones via their International Mobile Subscriber Identity (IMSI). But haven't known much about their capabilities, or really how their systems run. This information, split between manuals and documents for different Harris Corporation software and hardware, outlines how to set up a cell data dragnet using their software and IMSI-catching devices.
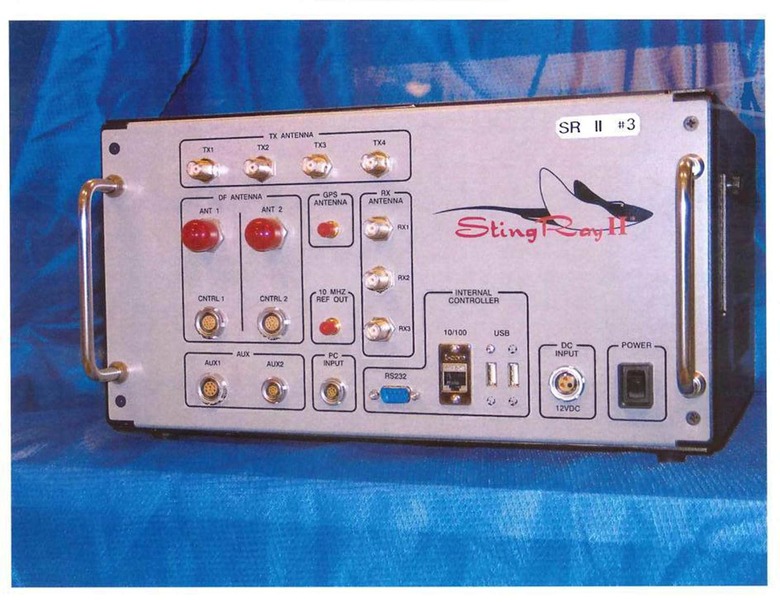
The takeaway is that these can be set up without a lot of technical know-how, as the documents give step-by-step instructions. Heck, The Intercept even acquired a video of the Windows-based Gemini software's setup instruction. The software-and-hardware combinations are pretty robust: The Stingray II device, for example, can impersonate four cell towers simultaneously and monitor four cellular provider networks at once.
Further, according to its quick setup guide that The Intercept uploaded, Gemini lets operators track phones across GSM, CDMA, UMTS and LTE, meaning it can monitor most phones on the market. Users can tag multiple phones and monitor them as they move throughout an area, even nicknaming them to find later. Perhaps most insidious is the Gemini software's capability to "listen and log over the air messages," though it's unclear how much metadata and communication content is saved.
"Stingray" has become a byword for the many devices, including different ones sold by Harris, that pose as cell towers to intercept phone data. In use since the mid-2000s, they came into the public eye after law enforcement used one to help catch a tax fraudster in 2008. The perpetrator fought it in court, claiming that tracking his phone calls and location via such a device violated his Fourth Amendment rights against illegal search and seizure. Since then, they've found their way into police departments and government agencies, from the NYPD, Department of Homeland Security and the IRS, to the UK and even a Canadian police station.
Whether police need warrants to monitor citizens with Stingrays has been legally debated. A year ago, the Department of Justice introduced new policy requiring its agents to get a warrant before tracking phones, with the DHS following suit a month later. A federal judge even dismissed evidence acquired by a Stingray without getting judicial permission. But police departments are another story, and often don't have any policy restrictions on using such devices.
The Intercept believes that these manuals originated in the Florida Department of Law Enforcement, though it's uncertain if they're up-to-date, as the most recent copyrights are dated 2014. Since these 200-plus pages are part of a larger cache acquired by the news outlet, we may see them release more documentation later that peels back more of the curtain shadowing Stingray policy and procedure.