Obama's got a new cybersecurity plan, but what's the point?
It’ll probably just end up as fancy toilet paper for the new administration.
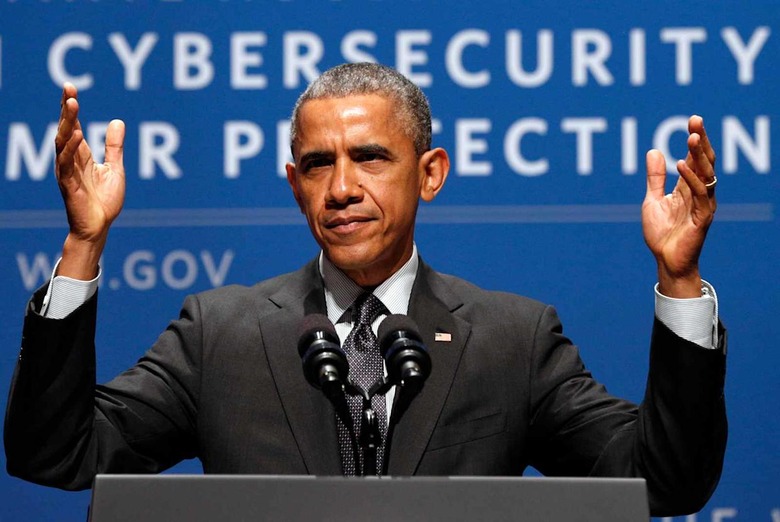
There's been a lot of hot air blown across headlines this week about the big cybersecurity plan proposed by the White House's Commission on Enhancing National Cybersecurity (PDF).
The plan for a commission to create long-term recommendations on beefing up America's cybersecurity was first hatched in April. It's a roadmap that should've been plotted many years ago, and is now being regifted to the next administration. Which may or may not use it for toilet paper.
The report, which identified six key issues for improving the cybersecurity of the US as a whole, is meaningless without the buy-in of the next administration. "The commission considers this report a direct memo to the next president," it states. "It is critical that the next president and his administration and Congress begin immediately to tackle each one of the issues raised."
Seeing the report put in motion by the next administration and Congress would be a good thing, if it happens in some form or another. That's because the report nails it when identifying problems, like securing Internet of Things (IoT) products ASAP. The report finally policy-izes fixing things people like me have been raising the alarm about for years. Namely, that the tech industry rushes things to market before securing them, that organizations no longer have control over people, devices and data, and that attackers are cashing in on our security fatigue.
Sounds good, right? It also includes a generous amount of attention to consumer rights, even suggesting a security "nutritional label" to help citizens assess the risks of products before they buy. Instead of telling us how many calories are in bran flakes, they want us to look at tech products and see "a rating system of understandable, impartial, third-party assessment that consumers will intuitively trust and understand."
There is a fair amount of hate in the report for the traditional username/password system everything runs on for login security. This translated into the commission's hardcore fanboying of the FIDO Alliance, whose emphasis is on getting rid of the traditional password model in favor of multifactor, biometrics and items like YubiKey.
I'll even give the report bonus points for mentioning the Mirai attack in its intro — the concerns presented are up to date. Most reports and the cyber plans of would-be presidents are basically "internet is dangerous because Target got hacked in 2013." I'm not joking.
However, most of the news this week omitted the fact that the 100-page report, based on nine months of study, has a few spots of rot under its shine.
The commission behind the report comprised 12 members. It included corporate interests like the president and CEO of MasterCard, the corporate VP from Microsoft Research, the chief security officer of Uber (Joe Sullivan, formerly Facebook counsel) and former NSA head Gen. Keith Alexander. Some of you may remember Alexander as the NSA's "collect it all" guy, who was forced to admit that the number of terrorist plots foiled by blanket surveillance were wildly and inaccurately overstated.
While I agree with the report's call to have the private sector and government collaborate on a cyber roadmap, and for that map to espouse citizens' rights, if their idea of private sector means Uber, there's a problem. You know, the same Uber that just decided to track its iOS users even when the app is turned off, bypassing the iPhone's consumer-protecting anti-tracking settings.
The commission's 12 "subject-matter experts" didn't come from the sprawling cybersecurity industry itself; they aren't the people out there in the trenches, over whom this policy will govern. Instead, the commission tapped NIST, DHS, DoJ, DoD and GSA — to ensure the apple doesn't fall too far from the tree, we must suppose. I mean, yay NIST. But seriously: Where was the actual public sector when these guys were in the pillow fort writing fan-fic about making passwords go away?
Some sections seem a little less on-the-level in terms of fighting the good fight for us little people.
There's quite a bit about protecting companies from being responsible for anything if they cooperate with the government on information-sharing. Because I guess CISA just wasn't enough. Action item 1.2.3 is about public-private sharing of "risk-management practices" (like the actions of an organization's security team, etc.) under the banner of security. This would explicitly protect companies from FOIA, discovery in litigation, use in regulatory enforcement, use as evidence, etc. ... Hey, maybe that's one of the recommendations we can thank Uber for.
Another curious section talks about working with the international community on "harmonizing" standards and policies, all in an envelope of securing the digital economy. A sagacious person implementing this might explore how it plays out with repressive regimes who could do a lot of damage under the guise of "incident response." Like when China and Russia made moves in 2012 to pass an international treaty that would allow UN member states to cut off and potentially intercept communications under vague wordings for cases that "appear dangerous to the security of the State [...] or to public order or decency."
Ultimately, the report's results are a range of recommendations as action items that direct the next president to create initiatives, carve out budgets, make executive orders and collaborate extensively with the public sector. It states that within the first 180 days of the next administration, "the president should appoint an ambassador for cybersecurity to lead US engagement with the international community on cybersecurity strategies, standards and practices."
The report urgently expresses the need for funds to get federal organizations like the old hacked-to-the-gills OPM up to speed with security. "The next president should formally announce his intention to increase investment in modernizing federal IT," the commission wrote. Based on a calamitous shortage of cyber-workers, the report urges the next president to "initiate a national cybersecurity workforce program to train 100,000 new cybersecurity practitioners by 2020."
President Obama has made it crystal clear that it's up to the next administration to implement this. The new guys would be handling all of its extensive recommendations for collaboration with the private sector (joint public-private action). The report has its problems, yet this is likely its biggest one.
But for now, all our qualms with the report are conundrums for a quieter moment. We are on the precipice of chaos. Hucksters are selling mainly cyber solutions but also fear and uncertainty; the attackers crowd the space as they jockey to sell stolen creds for a few bucks; privacy violations heave consumers into apathy; and companies play the blame game now harder than ever. It's a perfect storm for the selfish to advance their own interests over everyone who doesn't get a seat at the table.
I guess that's why the positive parts of this advisory report feel like a bitter punch. It feels slow, and it feels late. Now more than ever it feels like we're being set up for more apathy, or worse, exploitation. It mostly feels like we should keep working on covering our own cyber-asses.
But if it makes the incoming administration think about cybersecurity a tiny bit, or as more than a tool to advance careers and screw those they disike, then I guess that little bit was worth it.