Russia used a cybercriminal's botnet for a spying campaign
The lines have blurred between private and state-sponsored hacks.
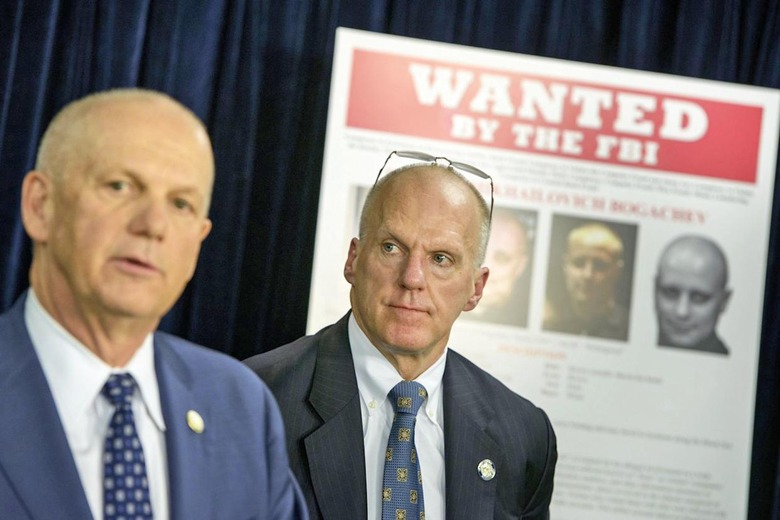
It's no secret that the lines between state-sponsored hacking and cybercrime are fuzzy. After all, relying on professional crooks offers plausible deniability if the intruders are ever caught. However, it's now apparent that those lines sometimes disappear altogether. The New York Times reports that Russian intelligence 'piggybacked' on criminal hacker Evgeniy Bogachev's now-defunct botnet, GameOver ZeuS, to conduct spying campaigns in the US and abroad. Between 2011 and 2014, infected computers were asked to search for documents that clearly reflected Russian political interests, including US support for Syrian rebels, Ukrainian operations and English searches for "top secret" and "Department of Defense." Those last queries suggest that there were at least some American government or contractor systems that had been compromised, and they're definitely not what you'd expect from an outfit siphoning bank accounts.
Russia isn't commenting, but it's no shock that the US imposed sanctions on Bogachev and other hackers. Ukranian officials have outright asserted that Bogachev is working "under the supervision of a special unit of the FSB." Moreover, Russia lets him operate freely — he's believed to be living in a resort town under his own name with no fear of arrest. And he's not alone. Security researchers report that Russia frequently recruits hackers from forums when conducting surveillance, turning a blind eye to their illegal behavior so long as they don't commit crimes within Russia.
As for what can be done? Not much beyond the sanctions. It's difficult to produce completely undeniable evidence of links between thieves and state-sponsored operations, and it's doubtful Russia will take any action so long as people like Bogachev focus on foreign targets. More than anything, this underscores the challenges of identifying and catching government-supported hackers. Investigators sometimes have only indirect clues as to who's really responsible, and they can't usually retaliate beyond either symbolic punishments or thwarting the hacks in question.