The worst part about the Google+ security flaw was the silence
500,000 user profiles is a drop in the ocean, but Google should still have told us.
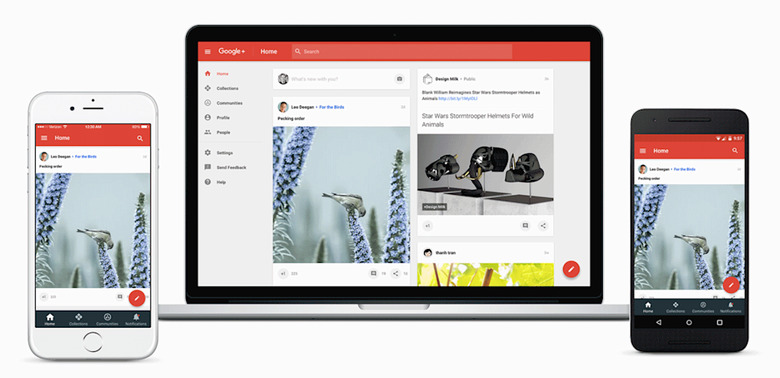
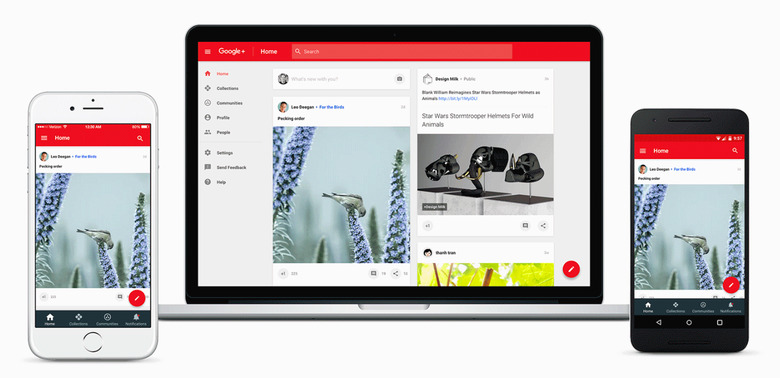
Google+ was the search giant's attempt to build a Google-owned social network that could take on Facebook. Despite the obvious benefits of Google's scale and reach, Google+ was a ghost town, and quickly became a punchline. The gag became that the only people who ever used it were Google employees and the company's die-hardest fans.
Unfortunately, the Wall Street Journal reported that a Google+ bug had exposed its users' personal data. Between 2015 and March 2018, the platform enabled APIs to leech your friends' information, including their email addresses, birthdate, pictures and occupation. Sure, a lot of that information you already share online, but folks who had set their data to be only viewable by friends were similarly affected.
What's troubling isn't merely the data bug — since the world now seems to meet these regular occurrences with nought but a shrug — but Google's attitude toward it. According to the report, company executives decided not to disclose the breach to avoid "immediate regulatory interest." Suddenly, Google wasn't so desperate to be associated with Facebook or social networking.
To be fair to Google, there are some differences between this and Facebook's Cambridge Analytica scandal. The company doesn't believe that anyone took advantage of the bug to leech up to 500,000 profiles. Again, that's a drop in the ocean compared to the (up to) 87 million that Facebook were found to have shared. Not to mention that Google did find the bug and close it after an internal review process into its security systems.
In a blog post, Google's engineering VP Ben Smith said that one of the reasons that Google chose not to disclose was because it didn't know what to disclose. As part of a so-called commitment to privacy, the company only kept API log data for two weeks at a time. So it simply doesn't know if hackers abused the platform because it wasn't looking for problems.
In the same post, Ben Smith said that the company has decided to close (the consumer version of) Google+ due to low engagement. Now, that's clearly true, and Google has, in recent years, been far more willing to kill off unsuccessful projects. But it also seems like an excuse designed to avoid demonstrating contrition for making a privacy snafu of this kind.
Sadly, it's likely that Google will avoid any real consequences for both the data exposure and its silence. Its stock price, which dipped yesterday, has already rebounded, and officials don't appear to be talking penalties. Lawmakers, too, won't care about this bug when CEO Sundar Pichai sits before the Judiciary Committee in November to talk about China and "bias." Washington types would much rather use the time, as they did for Mark Zuckerberg, to soapbox their performative victimhood about Google's non-existent biases.
Had the data exposure been discovered a little later, it would have come under the auspices of the EU's General Data Protection Regulation. That would have forced Google to come clean about the problem within three days of its discovery, and threatened punishments. Instead, the news of this will get washed away in the torrent of Pixel 3 announcements, and very little will change. Except for, perhaps, another couple of people wondering if Big Tech is so powerful now that it needs breaking up. Or even if there just needs to be better fines handed out to companies that are found violating privacy rules.
Google knows so much about you. What you search for, what TV you're watching, and who you're talking to. It hosts your email, stores your files and even offers an Office platform for you to do your job on its platform. The extraordinary power that it holds is troubling, and recent news has only made that unease more justified.
Update, 10/17/18, 4:45PM ET:This story and its headline have been updated to remove references to a data breach, as the data in question was exposed due to a security bug rather than an attack.