Tinder security flaw granted account access with just a phone number
The problem has been fixed, but it's still a pretty big flaw.
Security researchers at Appsecure found a way to access anyone's Tinder account via their phone number. The exploit took advantage of a software flaw in both the dating app's login process as well as the Facebook API that it's based on. The issues have been fixed since, but represent a pretty big security lapse.
"Both the vulnerabilities were fixed by Tinder and Facebook quickly," wrote Appsecure's Anand Prakash on Medium. Facebook and Tinder rewarded the company $5000 and $1250, respectively, for its report. This isn't the first report of Tinder security flaws, either, like when the company failed to encrypt user photos and (back in 2014) exposed users' exact locations for months.
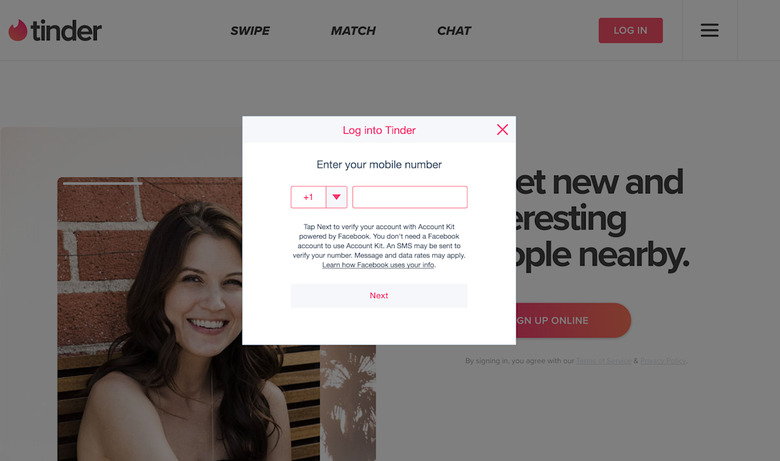
When you login to Tinder, you have the option of using your phone number, which is then passed along to Facebook's Account Kit for authentication to Tinder. The Appsecure folks found that they could get a valid access token with an API request to Facebook's Account Kit using a phone number. In addition, Tinder's login system wasn't checking these access tokens to make sure they matched the associated user's client ID, which means that any valid access token could let someone log in to your Tinder account.
Update: A Tinder spokesperson has issued the company's official statement:
"Security is a top priority at Tinder. Like other major global technology companies, we employ a network of tools and systems to protect the integrity of our platform. As part of our ongoing efforts in this arena, we employ a Bug Bounty Program and work with skilled security researchers across the globe to responsibly identify potential issues and quickly resolve them. At Tinder, we are constantly improving our protocols to not only meet, but exceed industry best practices. However, we do not discuss any specific security measures or strategies, so as not to tip off malicious hackers."