2018 in cybersecurity: Regrets, we have a few
Remember when we had privacy?
This was the year security slips, privacy fails and outright stupidity went from bad to surreal. It was a year in which warnings went unheeded and companies lost whatever trust we gave them. It was a nesting doll of security disasters. A clown car of willful negligence. A long 12 months of totally unsexy, nonconsensual edge-play with our data.
There were cops unlocking iPhones with corpses. Australia mandated backdoors. Apple came out swinging against accusations they were infiltrated by Chinese spy chips. Japan's Cybersecurity minister said he's never used a computer. The head of DC's top cyber think tank turned out to be a con man. A Russian spy claiming to be a cybersecurity aficionado faked her way into the GOP and NRA.
All that, and it seemed like every business big and small had a breach or exposed our private data in some way. Here's our roundup of the nuttiest fruitcakes no one wanted this year, but that we ended up getting anyway.
We didn't vote for this: Election insecurity

Between the lack of action by officials to secure the midterms, to voting machine vulnerabilities gone wild, this was the year American election security went beyond critical.
At the yearly hacking conference DEF CON, the Voting Village flipped the script on voting machine makers (and those who benefit from their insecurity) by exposing the whole sordid mess. They bought surplus decommissioned machines on eBay to probe for vulnerabilities, which caused the makers to panic and try to stop researchers from getting their hands on the gear. The DEF CON event made headlines as researchers of all ages successfully hacked machines and simulations of election websites with terrifying ease — which got the researchers attacked by people who accused them of aiding foreign adversaries. Those working to fix the issues disagreed, to say the least.
DEF CON's Voting Village then compiled a report of everything they found, as well as their conclusions about the issues in digital voting machines. The report was presented to lawmakers on Capitol Hill. Terrifyingly, the findings "highlighted a decade-old vulnerability in a ballot-counting machine used in more than half the states." DEF CON founder Jeff Moss described "a 'civil war' going on at big US voting-equipment vendors between employees who want to proactively address security vulnerabilities and those who stubbornly oppose doing that."
That was before the midterm elections. Also prior to the elections, ProPublica found that "The Election Assistance Commission has ceded its leadership role [in securing the elections]" and some officials told ProPublica that "EAC commissioner, Christy McCormick, was effectively thwarting election security efforts." And Trump, unsurprisingly, just didn't give a shit.
Then the elections happened. There were lots of problems, but perhaps the biggest was Brian Kemp hacking the Georgia election in his favor by doing everything possible to keep people from fixing the well-known security holes in his state's system. Evil clown, away with you!
The emperor wears no security: Cyber void in the White House

For its year in security, the White House basically acted like a guy walking down the street who saw a pile of poop on the sidewalk and aimed for it.
Especially when, in May, it was revealed the President of the United States had long ago decided that securing his phone was just "too inconvenient." This prompted press outlets to declare that he had "gone rogue" with the security of his personal electronics. "The president has kept features at risk for hacking and resisted efforts by staff to inspect the phones he uses for tweeting," wrote Politico, prompting another round of collective terror at the state of our state's security.
"The president," the outlet reported, "who relies on cellphones to reach his friends and millions of Twitter followers, has rebuffed staff efforts to strengthen security around his phone use, according to the administration officials."
The very next month, I reported that John Bolton had eradicated the White House positions (and people) who should be standing between the United States and cyberattacks against our voting processes, our infrastructure and the tatters of our democracy. Next, Bolton appointed a cyber-deputy aide with zero experience in cybersecurity. Fred Fleitz, who now plays a critical role in coordinating national security policy and is a self-appointed cybersecurity policy expert, went on the record saying that all those US intelligence community reports on Russia's election tampering were a setup. "Fleitz has also said it's "impossible" to know if Russia was responsible for election-related hacks," wrote Daily Beast.
Fleitz, a Fox News pundit and op-ed writer, stated that the "intelligence assessments were rigged for political purposes." Defending Russia, WikiLeaks, and RT, he undermined both the ODNI and DHS and stressed that there was no evidence of Russian involvement.
To bring it all home, near the end of 2018 we found out about Ivanka's personal email account, making her "the worst offender in the White House."
In short, the cybersecurity practices of our government's highest leadership can best be described as "pissing into the wind." It's no wonder the US refused to sign the international "Paris call for trust and security in cyberspace."
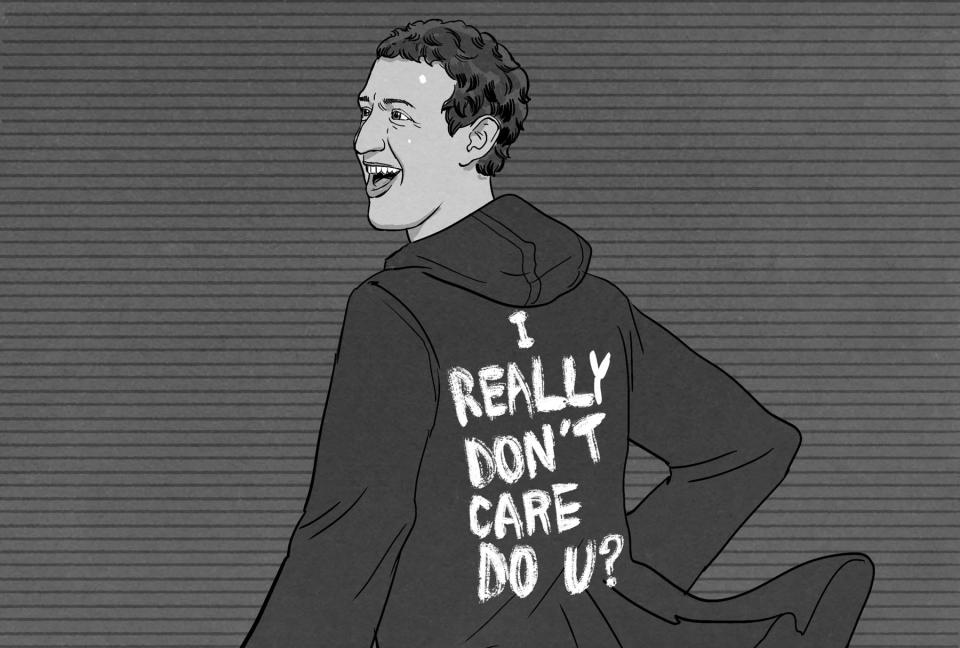
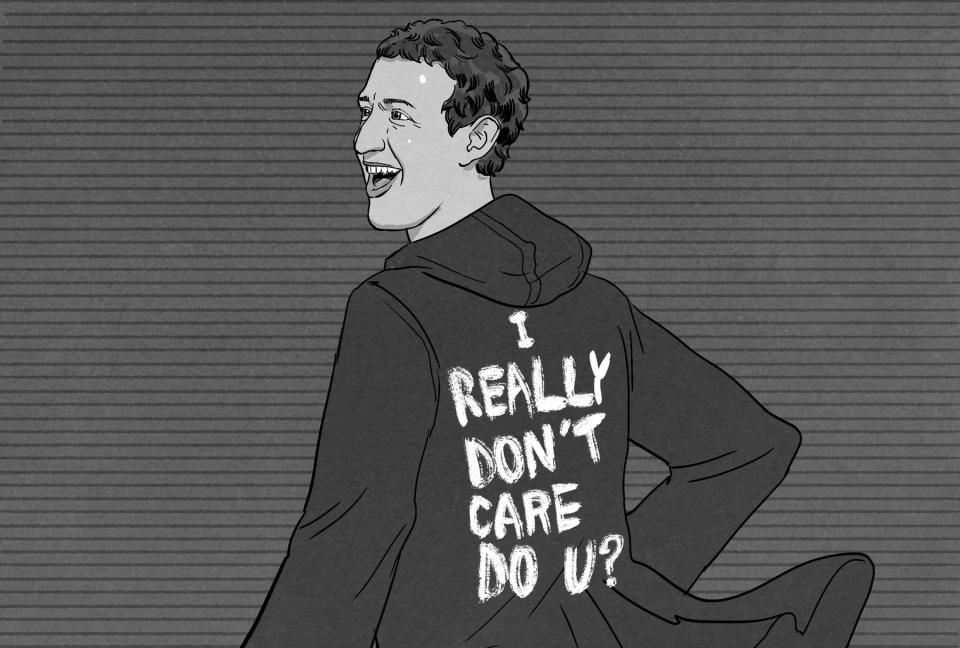
Facebook sees you when you're sleeping ... and its security was a joke

This year proved that even when given every opportunity to do so, Facebook will never do the right thing when it comes to user privacy or security. In fact, an argument could be made that people at the company have no idea what the words mean. Though maybe they're just working from radically different definitions than the rest of the world.
There's simply too much horrible, no-good, awful, and deeply distressing Facebook privacy and security news this year to cover in one go. But the highlights (er, lowlights) say a lot.
The API access stories, where companies were given beyond-the-pale access to user information, have been a yearlong liturgy of privacy horrors. Yet the massive, yearlong hack and the company's ad-profiteering off user security information are two things that look more like maliciousness than carelessness by the day. Both of which the company admitted to with evident reluctance.
We found out that the world's largest, most powerful and influential social network (and identity registrar) actively took user security information and gave it to advertisers. I'm talking about Facebook's two-factor security betrayal, where it was revealed the company took phone numbers under the guise of account security and used them to sell ads (and ad access to users).
Then, there was the massive and egregious breach revealed in October — which had gone on for at least a year. The number of directly affected users was 29 million, which is at least three Londons (population 8+ million), three New Yorks (population 8.5 million) or around half of the entire United Kingdom.
It was an extreme breach — Facebook revealed to users that unknown attackers got their "username, birthdate, gender, location, relationship status, religion, hometown, self-reported current city, education, work, the devices they used to access Facebook and the last 10 places they checked into (or were tagged in) on the site" as well as the past 10 searches affected users did on the site. Caveat for those "last ten" claims — remember, the attack was active and available for nearly a year.
The attackers got all that, plus user access tokens, which facilitate leapfrog entrance into connected apps. Facebook claimed at the time that no other sites were accessed -- but Facebook didn't cooperate with affected sites to help connected apps find affected users (Tinder resorted to appealing to Facebook for a list of affected accounts through CNN), we should be more than skeptical about this claim.
Talk about a dream come true for identity thieves. And in case you think Facebook would at least try to do the right thing by its users, the company has stated it would not be providing identity protection to those affected. So, in light of all those real names they collected, all those IDs they forced people to upload ... let's just say the worst thing possible happened with that information.
As the year comes to a close (and not a moment too soon) it's interesting to reflect that 10 years ago, it seemed like no one outside IT and hacking conferences really talked about cybersecurity, our data or digital privacy.
Now these three things are practically all anyone talks about. Which is good, but also why it's mind-bending that it's all such a disaster. Honestly, there are now a whole lot of people who know better. And there's no excuse for what we've seen go down on the main stage in the cybers this year.
Here's to hoping there's nowhere to go in 2019 but up.