Hackers find an 'unpatchable' way to breach the Nintendo Switch
An NVIDIA Tegra X1 exploit unlocks the Switch's critical bootROM.
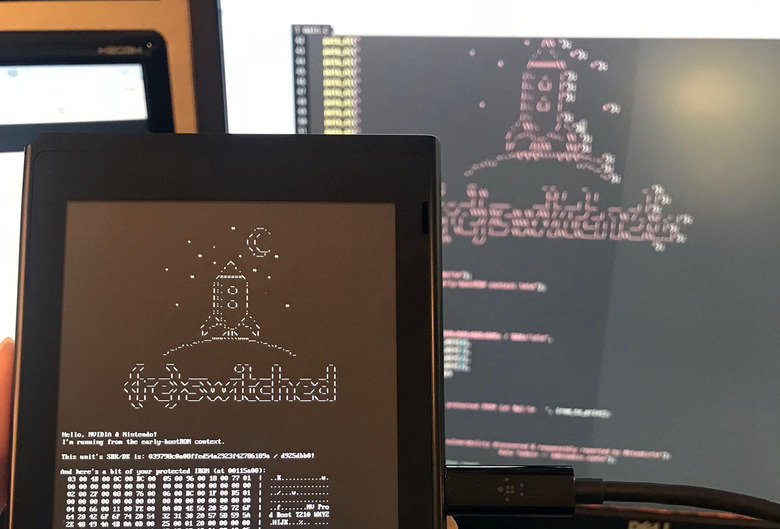
Security researchers from ReSwitched have discovered a Nintendo Switch vulnerability that could let hackers run arbitrary code on all current consoles. Dubbed "Fusée Gelée" ("Frozen Rocket") it exploits buggy code in the NVIDIA Tegra X1's USB recovery mode, bypassing software that would normally protect the critical bootROM. Most worrisome for Nintendo is that the bug appears to be unpatchable and could allow users to eventually run pirated games.
The exploit involves kicking the Switch into USB recovery mode by shorting a pin on the right-hand Joy-Con connector. A payload is then sent at a crucial point during a USB check, forcing the system to "request up to 65,535 bytes per control request," much more than it can handle. That causes a DMA buffer overflow in the bootROM, giving hackers access to the normally-protected application stack. From there, they can run whatever code they want.
Unfortunately, unlike the one in your PC, the Tegra X1 bootROM on the Switch is hardcoded and can't be changed once it leaves the factory. That would be fine if it were secure, but unfortunately, it has the bad length error built in, so there's nothing that NVIDIA or Nintendo can do to fix the 14.8 million Switch systems already shipped, according to ReSwitched.
Well, it is 73F in Denver, today: so I guess it's as good a time as ever to acknowledge: https://t.co/UGqtMeHR13.
Writeup: https://t.co/W07AUWPd9u
Sample payload: https://t.co/d5nCLNa7E5Guides and information so you can use it too are forthcoming. :)
— Kate Temkin (@ktemkin) April 23, 2018
By exposing secret code in the Application stack, the exploit might allow hackers to reverse engineer application security and run pirated or emulated software. It could also be useful for less dodgy functions, like finally giving users the ability to backup game saves in case their Switch is stolen or broken. "Fusée Gelée isn't a perfect, 'holy grail' exploit—though in some cases it can be pretty damned close," said ReSwitched's Kate Temkin.
As Ars Technica points out, Nintendo does have some options, as it might be able to detect hacked systems and lock them out of online play. It's also not a given that games can be hacked just because the system has been exposed, as they have their own encrypted DRM built in.
ReSwitched decided to reveal the exploit in a limited way, but will release further details and guides on how to use it by June 15th. Other groups are also apparently on the job, too. Fail0verflow teased a Dolphin emulator running Legend of Zelda: Wind Walker on a Switch earlier, and has now released its own "shofel2" Tegra X1 bootROM exploit and Nintendo Switch Linux loader.
If you want to try one of the hacks, Fail0verflow does have a warning, though. "If your Switch catches fire or turns into an Ouya, it's not our fault," its Github post states. "It's stupidly easy to blow up embedded platforms like this with bad software (e.g. all voltages are software-controlled). We already caused temporary damage to one LCD panel with bad power sequencing code. Seriously, do not complain if something goes wrong."