Researchers create device that opens hotel doors with old key cards
It could give a user access to an entire hotel within minutes.
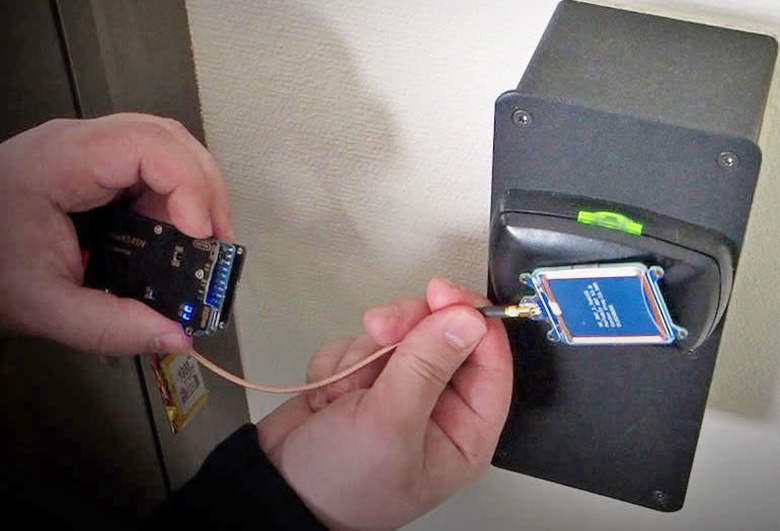
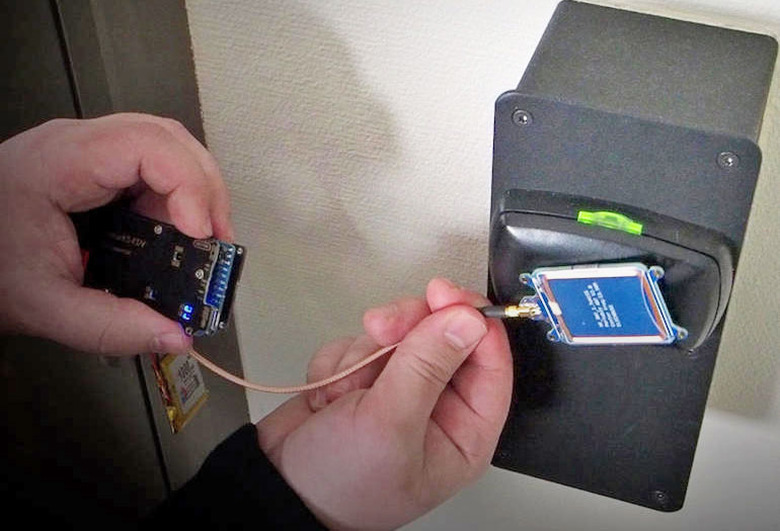
Researchers at cybersecurity firm F-Secure have designed a device that can pull data off of hotel key cards and essentially create a master key for an entire hotel. Alarmingly, the key card doesn't even have to be currently in use. The device can steal data from the card whether it's functional or expired and can give the user access to pretty much any room in the hotel in just a matter of minutes. "It can be your own room key, a cleaning staff key, even to the garage or workout facility," F-Secure's Tomi Tuominen told Gizmodo. "We can even do it in an elevator if you have your key in your front pocket; we can just clone it from there."
The inspiration for the device came in 2003 when a laptop belonging to a colleague of the researchers, who was attending a hacker conference in Berlin, was stolen from his hotel room. Because there was no sign of forced entry and no unauthorized access recorded in the entry logs, nothing much was done.
The ability to create such a device is certainly worrisome, but there is some good news. It took the researchers quite a long time to develop the device, years in fact, and the F-Secure team says it's not aware of any such devices being used maliciously in the real world. "We don't know of anyone else performing this particular attack in the wild right now," Tuominen said in a statement.
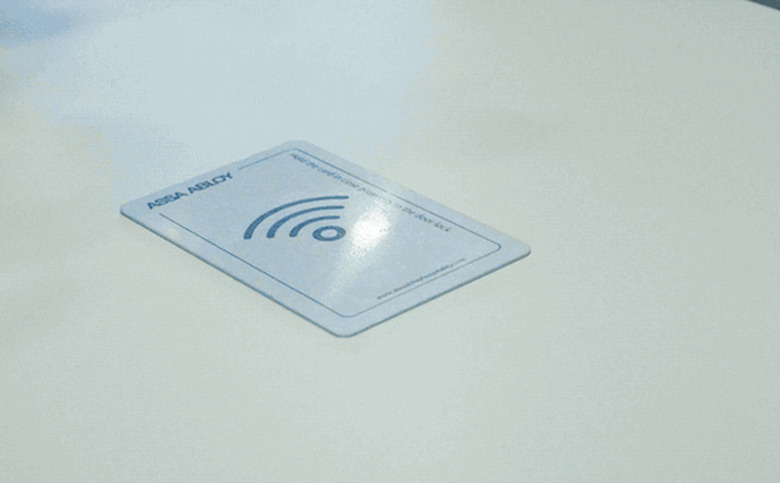
The locks the F-Secure team targeted were developed by VingCard, now owned by Assa Abloy, a company that has acquired a number of other major lock companies such as Yale and August Home and is now the largest lock manufacturer in the world. The VingCard system they targeted is reportedly used in over 42,000 properties in 166 countries. F-Secure says it notified Assa Abloy of its findings and over the past year, the two groups have worked together to develop a fix for the vulnerabilities exploited by the master key device. Affected properties have received updates. "Because of their diligence and willingness to address the problems identified by our research, the hospitality world is now a safer place," said Tuominen. "We urge any establishment using this software to apply the update as soon as possible."
Hotels have been targets of malicious actors in a number of ways over the years, with attacks including credit card info-swiping malware, keyloggers installed on publicly available hotel computers and exploits of hotel WiFi. And others have made devices that crack key card locks as well.