Android malware mimics Uber's UI to steal your log-in
It even deep links to a page in the real app to convince you it's legit.
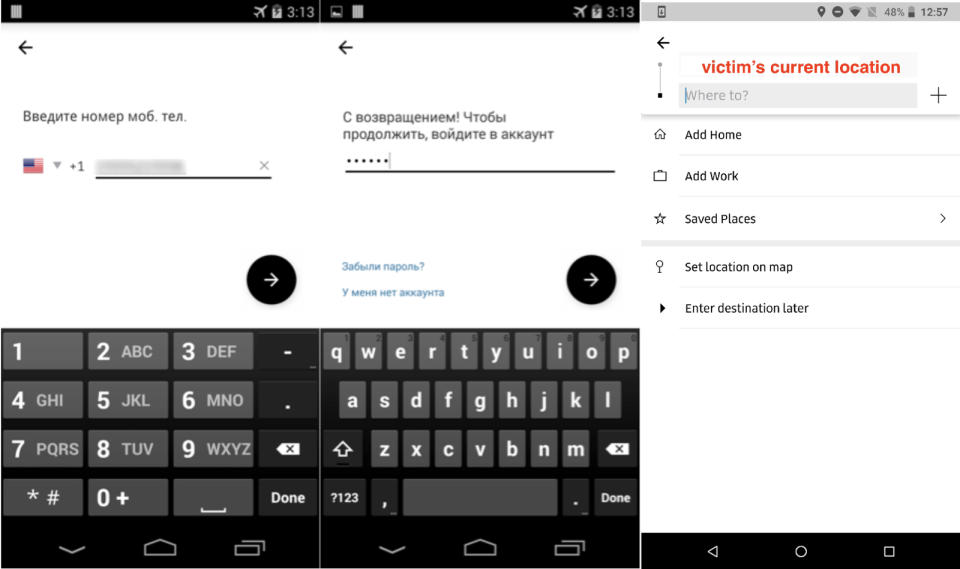
The Android.Fakeapp Trojan has been infecting Google's mobile platform for ages in different forms, and one of its latest variants mimics Uber's interface. According to Symantec, which discovered the new variant after looking at several, the Trojan pops up on screen in regular intervals in an effort to fool you into typing your phone number and password. When you press enter, it sends your log-in credentials to a remote server: the Trojan's creators could then use your log-in to compromise your other accounts or to sell them to fellow hackers on the black market.
This Fakeapp variant doesn't stop at presenting a copy of Uber's log-in screen. To give you a false sense of security and to prevent you from becoming suspicious and changing your password too soon, it even loads a screen from the legitimate app that shows your location after you press enter. It apparently does that by deep linking to a URL in the real application that starts up Ride Request activity using your location as the pick-up point.
Symantec says this case "demonstrates malware authors' neverending quest" to find new social engineering techniques to trick users. Its advice? The usual: make sure your software is updated, install reputable anti-malware apps and don't download from unfamiliar websites.
Update: An Uber spokesperson told Engadget:
"Because this phishing technique requires consumers to first download a malicious app from outside the official Play store, we recommend only downloading apps from trusted sources. However, we want to protect our users even if they make an honest mistake and that's why we put a collection of security controls and systems in place to help detect and block unauthorized logins even if you accidentally give away your password.



