Twitter claims 'social engineering attack' led to crypto scam tweets
The investigation is ongoing.
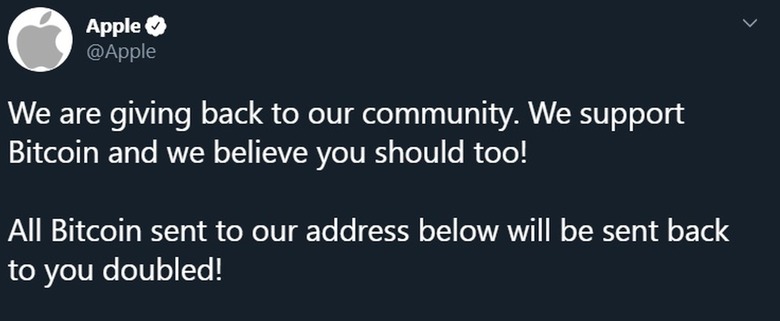
In its first detailed statements since someone took over a number of high profile accounts Wednesday afternoon, Twitter posted a thread explaining "what we know so far." While rumors have swirled about what may have caused a compromise that gave hackers access to Twitter accounts for Elon Musk, Bill Gates, Barack Obama, Apple, Kanye West and others, the company stated "We detected what we believe to be a coordinated social engineering attack by people who successfully targeted some of our employees with access to internal systems and tools."
We know they used this access to take control of many highly-visible (including verified) accounts and Tweet on their behalf. We're looking into what other malicious activity they may have conducted or information they may have accessed and will share more here as we have it.
— Twitter Support (@TwitterSupport) July 16, 2020
This was disruptive, but it was an important step to reduce risk. Most functionality has been restored but we may take further actions and will update you if we do.
— Twitter Support (@TwitterSupport) July 16, 2020
The company went on to say that after temporarily limiting Twitter activity — including a period where all verified accounts were prevented from tweeting — it has restored those features. Internally it's limiting access to its tools while the investigation continues.
Twitter did not comment on a report by Motherboard that included a picture of its internal tools, and cited anonymous sources in the SIM swapping community that said an insider did the work for them. TechCrunch reports that a hacker named "Kirk" contacted forum posters on OGUsers, a site frequented by people who trade in popular social media handles, saying he needed help selling stolen vanity usernames. Their source indicated that it was unlikely a Twitter employee was involved, but one way or another, "Kirk" had access to internal tools and moved on to performing account takeovers later in the day.
Twitter also said that it's investigating "what other malicious activity they may have conducted or information they may have accessed." Based on the hackers ability to completely take over accounts, and the number of accounts they accessed, there's speculation that they could have broken into virtually anyone's account to see information stored as drafts or direct messages. We'll continue to update this post as we learn more about what happened.