Nest Learning Thermostat has its security cracked open by GTVHacker
While we wait for Google I/O (which starts tomorrow) to find out what will become of the company's TV platform, a team that we've seen bust open the padlocks on Google TV, Chromecast and Roku has a new target. GTVHacker just revealed an exploit for the (now Google-owned, and owner of Dropcam) Nest Learning Thermostat. It could let owners do new and interesting things (like replace the Nest software entirely) but of course, someone with bad intentions could take it in another direction: monitor whether the owner is home via its motion detector, sniff network traffic, or just crank up the temperature a few degrees — all without even opening the device. Interested in how the hack works? Like most jailbreaking techniques we've seen on mobile and home connected platforms it requires physical access to the device, so you don't have to worry bout someone wardriving down the block and wreaking havoc with your A/C. Check after the break for more details and a video, and if you're headed to DEFCON in August, the team has a demonstration planned that's oh-so-comfortingly titled "Hack All the Things."
Update: Nest has responded, saying the team's software "doesn't compromise the security of our servers or the connections to them and to the best of our knowledge, no devices have been accessed and compromised remotely."
[Image credit: gpshead/Flickr]
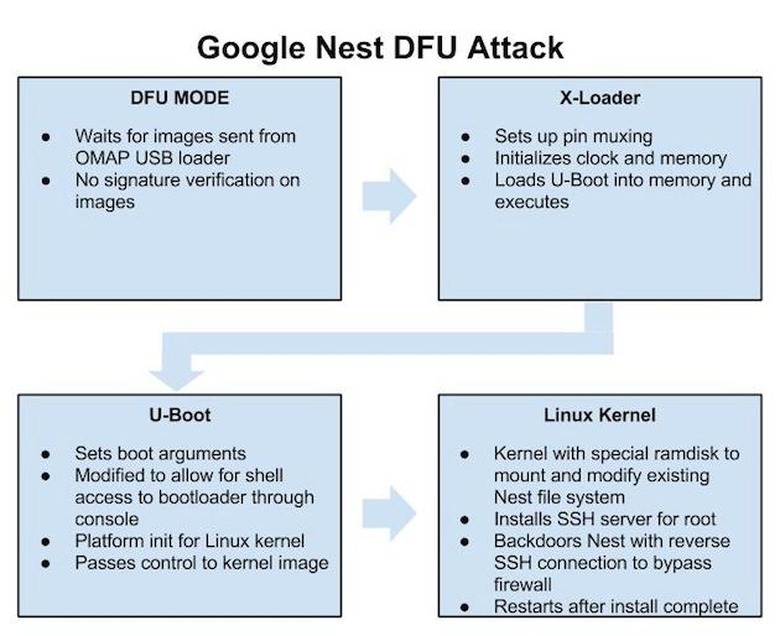
So how is it done? The GTVHacker exploit uses Nest's own pathway for loading software (via the USB port, requiring physical access to the device) to run its own boot-loader and add an SSH server with root access. In layman's terms – it sneaks in like a legitimate update, but opens a backdoor giving whoever put it there complete control, and potentially without the device's owner being aware that anything has changed.
A more detailed account of how it works is on the GTVHacker blog, but the team has already packaged the tool as a one-click root + installer that works from Linux (available for download here, Windows version coming soon), so all it takes to run the tool is a PC and a USB cable. If you're looking for more home theater hacks, the team also promises new rooting techniques for Chromecast and Roku are in the works. For now, if there's a guest lingering in your living room with their laptop and cord at the ready, we'd suggest keeping a close eye on them.
Nest:
This is a physical jailbreak requiring physical access to the Nest Learning Thermostat. It doesn't compromise the security of our servers or the connections to them and to the best of our knowledge, no devices have been accessed and compromised remotely.
Pre #DEFCON Tease: Using DFU to Root Your Google @Nest. #HackAllTheThings #NoSolderingRequired http://t.co/yqUe5sL7Jk
- GTVHacker (@gtvhacker) June 24, 2014