Study claims over 80 percent of 'deep web' traffic relates to pedophile sites
Eighty percent of web traffic on the "deep web" relates to child pornography, according to a study conducted by the University of Portsmouth, UK. It's no surprise that consumers/providers of illegal material want to hide their tracks. What is surprising is the huge amount of traffic share that pedophile material commands. There are plenty of other illegal activities one might use the darker corners of the internet for (buying drugs, contraband etc.), and of course law-abiding folk that just want the anonymity that services like Tor provide. The University's study, however, indicates that once you account for automated "botnet" traffic, 83 percent of deep web traffic was landing at sites providing content containing some sort of sexual abuse of children.
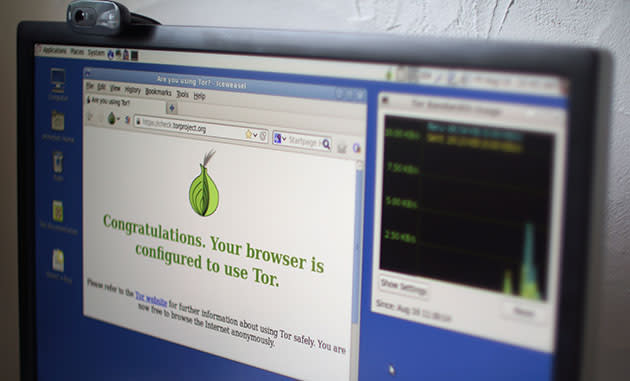
To conduct the study, researchers placed 40 computers onto Tor's network as relay machines (the anonymizing service relies on volunteer's computers moving encrypted traffic around). The team then used web-crawling software to categorize the (approximately) 45,000 services that were using Tor's hidden services (which is distinct from the Tor anonymizing network that stops websites from tracking your identity) at the time. Data from their relays provided the insight into where traffic was going, after discounting automated "botnet" activity (usually relating to malware, viruses and so on). This data was presented at the Chaos Computer Congress in Hamburg, Germany, and you can watch the presentation itself here or embedded above.
To further illustrate how out of whack the numbers are, it's estimated that the number of sites -- like Silkroad -- selling contraband, constitute about a quarter of all hidden services. Child abuse sites? Just two percent. This imbalance could be tough love for those who defend services like Tor for its legitimate uses (privacy and security). Though there are unsurprisingly suggestions that the data is open to interpretation, and that web use/behavior patterns need to be factored in (daily visits over monthly purchases etc.). Also, it's possible that the traffic to such sites might not always result from an actual "consumer." Law enforcement will be investigating such sites, and there's the possibility some of the traffic is a noble attempt to knock them offline through denial of service (though it's not clear if this would have been ignored by the study's botnet profiles). There's also an argument that some services are short lived on the deep web, so the study may just be revealing that abusive sites are more persistent.

