Blame the Internet of Things for today's web blackout
Flashpoint says hacked cameras and routers enabled a Mirai botnet to take out major websites on Friday.
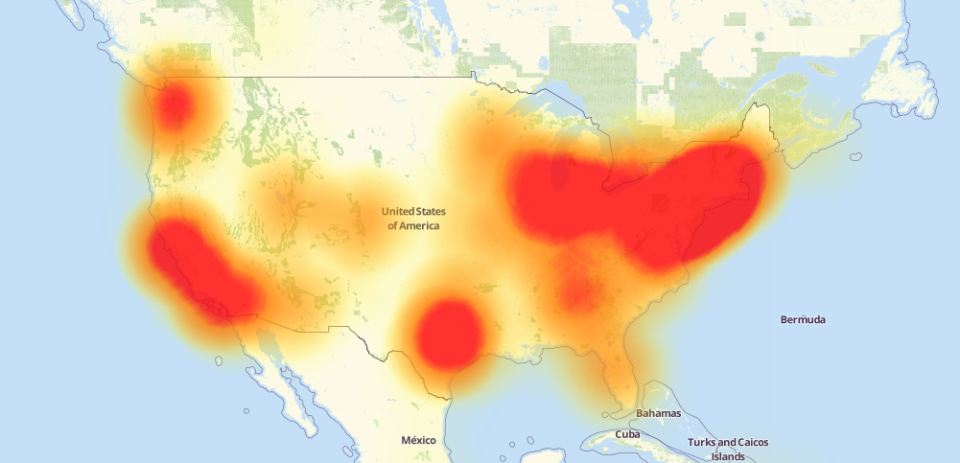
Today's nation-wide internet outage was enabled thanks to a Mirai botnet that hacked into connected home devices, according to security intelligence company Flashpoint. The distributed denial of service attack targeted Dyn, a large domain name server, and took down Twitter, Spotify, Reddit, The New York Times, Pinterest, PayPal and other major websites.
"Flashpoint has observed Mirai attack commands issued against Dyn infrastructure," Flashpoint writes. "Analysts are still investigating the potential impact of this activity and it is not yet clear if other botnets are involved."
Mirai is not a new hacking tool. A massive Mirai attack took down the site of popular security researcher Brian Krebs in late September, peaking at a nearly unprecedented 620 Gbps. Mirai takes advantage of weak security protocols on IoT devices -- in the Krebs case, 145,000 devices were infiltrated, including security cameras and DVRs in homes and offices around the world.
The author of the Mirai malware made its code open-source, and security experts have been warning of a possible large-scale attack since this information came to light.
For its part, Dyn is attempting to stem Friday's attack on its servers. At 3:30PM ET, the company announced the attack had entered its third wave.
"We are actively in the third flank of this attack," Chief Strategy Officer Kyle Owen said, according to TechCrunch. "It's a very smart attack. As we mitigate, they react."
To anyone who is still able to read this story: Congrats. Also, we're doomed.
Update: We're not doomed (for now)! The third attack has been resolved, Dyn announced at 6:15PM ET.

