Trump’s cybersecurity order delivers nothing but more surveillance
It's mostly copied from the Obama administration's work, so it can’t be all that bad. Right?
Remember that cybersecurity executive order we anticipated from the Trump administration, which seemed to quietly disappear in January?
The already-delayed deadline for Trump's EO on "the cyber" and his promise to create a cyber-review team passed last month. Many were wondering if it would fade off into oblivion like a tyrant's hairline — or show up suddenly to drop cyber-bombs on someone's vacant cyber-tarmac.
After a suspenseful delay and one leaked draft, the Trump administration's cybersecurity EO, "Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure," finally saw the light of day. Between the WannaCry ransomware news and nonstop pandemonium issuing from the Mad King's court, it was easy to miss.
The good news is that Trump didn't appoint Julian Assange or Rudy Giuliani to be the nation's Cybersecurity Commandant. No, he bestowed that honor on a man whose primary qualifications include being a real estate heir and the president's son-in-law: Jared Kushner.
Since corrupt appointments have made the past few months a sort of Groundhog Day in hell, it's no surprise, really. I mean, it was only one month before the election that Trump finally put a cybersecurity policy on his website. And it was cribbed from a speech he rattled off saying that he intended to hand most of the work off to others.
As we've come to expect from this administration, the page with Trump's cybersecurity policies is now a 404.
The original text had Trump saying that when he was sworn in, he'd order "an immediate review of all US cyber defenses and vulnerabilities, including critical infrastructure, by a cyber-review team of individuals from the military, law enforcement and the private sector."
Fast-forward to April: We finally got an idea of what the hell was going on. Whispers around government-press campfires said the Trump regime was "close" to revealing its cybersecurity EO and that the president's son-in-law was working on the order with White House tech-policy aides in Kushner's new Office of American Innovation.
Trump also recently signed an executive order creating the American Technology Council, with Kushner as director. Combined with the new EO on cyber, it means that Kushner is in charge of implementing the order. So he will be managing the hiring and be awarding contracts.
But how did it turn out? Well, some people really love it. That's probably because they haven't thought through what it means that Kushner is running the biz-dev end of the show. Also because the whole order reads like Jared copied Obama's homework.
Specifically, Jared and company copied the Obama White House "Presidential Policy Directive 21 of February 12, 2013" and the "Commission on Enhancing National Cybersecurity" report released in December 2016.
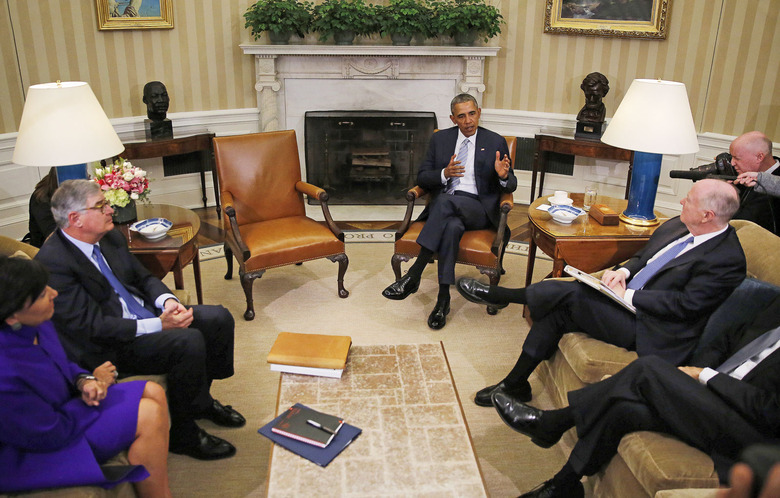
U.S. President Barack Obama meets with members of the Commission on Enhancing National Cybersecurity at the White House in Washington February 17, 2016.
As you can see, Obama's 2016 report has been removed by the Trump administration. Take my word for what was in it.
Unfortunately, Trump and Kushner didn't copy most of the parts that matter.
The new cybersecurity order has three sections. The first part, "Cybersecurity of Federal Networks," says they'll create reports geared toward modernizing federal IT guided by the National Institute of Standards and Technology's (NIST) Framework for Improving Critical Infrastructure Cybersecurity. Framework that came from President Obama's order in 2013.
The second section, "Cybersecurity of Critical Infrastructure," tells agency leaders to figure out how they can support the cybersecurity of "Section 9 entities" at risk of attack and affecting public health, safety and national security. This is yet another part cribbed from Obama's 2013 order.
This middle bit includes only a quick mention of botnets and IoT. And even this tiny section seems suspect in its vague wording. Like the rest of the order, there is nothing telling us how they plan to tackle the problem. It concludes by saying a report is due in a year.
The entire order is a list of reports with loopholes, and for copied homework, it sure left out crucial national security hot points. It's a shame threats like Mirai — star of the 2016 cybersecurity threat-show in the 2016 order — have to be inferred in the Trump-Kushner order.
Researcher Jake Williams from Rendition Infosec saw bright, flashing hazard signs when looking at the Internet of Things section. This section puts decision making around securing IoT devices and consumers under the jurisdiction of the FCC and FTC, among others.
Williams told Engadget in a Thursday call, "It's a power-grab for new capabilities by law enforcement."
He explained: "If it's true that Trump brought in industry leaders, then any one of them knows you can't stop botnets without lots of network monitoring. Given some of the things I've seen, I suspect they'll use the report to say, 'Look at the problems; let's give law enforcement more monitoring capabilities.'"
Drawing a clear line between intentions of the EO's decision makers on IoT and potential harm to consumers, Mr. Williams added that "the idea that they want the FCC involved in botnet monitoring would be to justify the commercial losses and making that a national security issue."
Of course, reducing consumer cybersecurity protections is right in line with the new FCC's statements. It's also in lockstep with Trump's outspoken enthusiasm for government surveillance. In his words, the NSA "should be given as much leeway as possible."
Donald Trump meeting with cyber security experts in the White House, January 31, 2017.
That might also please the original team that backed the Obama report — it also had serious flaws when it came to protecting citizens from government overreach. Lest we forget, the commission behind it included corporate interests like the president and CEO of MasterCard, the corporate VP from Microsoft Research, the chief security officer of Uber (Joe Sullivan, formerly Facebook counsel) and former NSA head Gen. Keith Alexander. Some of you may remember Alexander as the guy forced to admit that the number of terrorist plots foiled by blanket surveillance was wildly overstated.
The final section, "Cybersecurity for the Nation," begins with vague wording about protecting the internet and fostering a cybersecurity workforce ... but goes right into a 90-day deadline for a plan on "the nation's strategic options for deterring adversaries and better protecting the American people from cyber threats." Sounds like cyberwar to me.
Next, within 45 days Trump wants the FBI and the secretaries of defense and homeland security (among others) to give him everything they have on "their international cybersecurity priorities, including those concerning investigation, attribution, cyber-threat information-sharing, response, capacity-building, and cooperation."
Talk about missing the point of copying someone's work; the order is short, opportunistic and wholly lacking specifics. No action items or direction to create initiatives; there's a little nod telling Jared Kushner to carve out budgets (but no details), and nothing about collaboration with the public sector.
And while Obama's 2016 report included a generous amount of attention to consumer rights, even suggesting a security "nutritional label" for products, we come up empty with Trump and Kushner's order.
I think you can see why it's more than annoying that some of my colleagues saw the EO and thought it was a good thing. It's not. It's about 500 steps backward from where we were last year, with a layer of malfeasant opportunism on top.
And we weren't exactly in a great place last year with our government coming to grips with our nation's cybersecurity, either.