exploit
Latest

Amazon fixes security flaws allowing smart home hijacks
Some smart home device owners may have dodged a bullet. Amazon recently patched 13 security flaws in an operating system for the Internet of Things, FreeRTOS, as well as Amazon Web Services connection modules. The holes let intruders crash devices, leak the contents of their memory and remotely run code, effectively giving attackers full control. The flaws might have been far-reaching if they'd gone unfixed -- both FreeRTOS and its safety-oriented counterpart SafeRTOS are used in a wide range of devices inside and outside the home, including cars, aircraft and medical gear.

MIT finds a smarter way to fight Spectre-style CPU attacks
Many companies have developed patches to mitigate Meltdown- and Spectre-like speculative memory attacks. However, they can come with compromises: they can leave major gaps and still slow down your system. MIT researchers may have a better way. They've developed a new method, Dynamically Allocated Way Guard (yes, DAWG is on purpose), that promises tight security without dragging performance through the dirt.

WhatsApp fixes video call exploit that allowed account hijacks
WhatsApp owners may have just dodged a bullet. The messaging service has fixed a security flaw that let intruders hijack the app (and thus your account) when you answered an incoming video call in Android or iOS. If an attacker sent a malformed Real-time Transport Protocol packet, it would corrupt the app's heap memory and open it to attack. Web users weren't affected, since the browser-based client relies on the WebRTC protocol.

Initial 'Fortnite' Android installer let hackers install malware
When Epic said it would skip the Google Play Store with Fortnite's Android release, it raised eyebrows among security experts. Wasn't it creating risks by encouraging gamers (some of whom didn't understand the potential dangers) to install non-Store apps? Well, it did... although not quite in the way you might have expected. Epic Games has patched a Google-discovered vulnerability in Fortnite's original Android installer that would have let intruders download and install malware. The exploit used a man-in-the-disk attack that took advantage of Epic's initially flawed storage handling to intercept download requests and load nefarious content.

Android exploit targeted apps' shoddy use of external storage
Many mobile security flaws revolve around obvious avenues like websites or deep, operating system-level exploits. The security team at Check Point, however, has discovered another path: apps that make poor use of external storage like SD cards. While apps would ideally stick to internal storage (which Google sandboxes against outside influence) as much as possible, some apps have relied unnecessarily on unprotected external storage and didn't bother to validate the data coming from that space. An intruder could take advantage of that poor security policy to manipulate the data and cause havoc -- Check Point called it a "man-in-the-disk" attack.

Permanent LTE exploits steer users to rogue websites
LTE was theoretically supposed to fix the security holes baked into earlier wireless standards, but it isn't completely immune. An international team of researchers has discovered a attack methods (nicknamed aLTEr) that takes advantage of inherent flaws in LTE to direct users to hostile websites. An active exploit uses the lack of integrity checks in LTE's lower layers to modify the text inside a data packet. Since that's easy to determine with DNS packets, which direct traffic to website addresses, you can steer requests to malicious DNS servers and thus take the user to a website of your choice.

Intel details fourth Spectre-style CPU security flaw
Intel said it was expanding its bug bounty program to help find more Spectre-like processor security flaws, and unfortunately it just found one. The company (along with Google and Microsoft) has disclosed a fourth exploit (simply titled Variant 4) that once again uses speculative execution to expose some data through a side channel. The attack is so far known to work in a "language-based runtime environment" like the sort you'd see in a web browser (say, JavaScript), although Intel hadn't seen evidence of successful browser-based exploits.

Global cyberattack targets 200,000 network switches (updated)
The past few days haven't been great for the internet's broader security. Iran's Communication and Information Technology Ministry has reported that it was a victim in a global cyberattack that compromised about 200,000 Cisco switches that hadn't yet received patches for exploits in the company's legacy Smart Install protocol. The attackers displayed a US flag on at least some screens, complete with a "don't mess with our elections" warning, but the attack wasn't focused on Iran -- only 3,500 switches fell to the exploit in the country. About 55,000 of the victim devices were in the US, IT Minister Mohammad Javad Azari Jahromi said, while 14,000 were in China. Other victims were located in Europe and India.

Sophisticated malware attacks through routers
Security researchers at Kaspersky Lab have discovered what's likely to be another state-sponsored malware strain, and this one is more advanced than most. Nicknamed Slingshot, the code spies on PCs through a multi-layer attack that targets MikroTik routers. It first replaces a library file with a malicious version that downloads other malicious components, and then launches a clever two-pronged attack on the computers themselves. One, Canhadr, runs low-level kernel code that effectively gives the intruder free rein, including deep access to storage and memory; the other, GollumApp, focuses on the user level and includes code to coordinate efforts, manage the file system and keep the malware alive.
LTE security holes could lead to fake emergency alerts
Vulnerabilities in cellular network technology definitely aren't things of the past. Researchers at Purdue and the University of Iowa have outlined exploits in LTE protocols that would let intruders conduct ten serious attacks, including spying on calls and text messages, tracking locations, knocking devices offline and even faking emergency alerts. Intuders can take advantage of three key protocol tasks (such as attaching a device to the network and maintaining a connection) to conduct authentication relay attacks that not only let them connect to the network without credentials, but masquerade as the victim's device. A hacker could not only compromise the network, but frame someone else for the crime.

BitTorrent client exploits could let rogue websites control your PC
BitTorrent's peer-to-peer app and its lightweight uTorrent counterpart are susceptible to particularly nasty hijacking flaws. Google researcher Tavis Ormandy recently detailed a host of DNS rebinding exploits in Windows versions of the software that lets attackers resolve web domains to the user's computer, essentially giving the intruders the keys to the kingdom. They could execute remote code, download malware to Windows' startup folder (making it launch on the next reboot), grab downloaded files and look at your download history. The flaws touch on all unpatched versions, including uTorrent Web.

Air Force security hackathon leads to record payout
The US Air Force's second security hackathon has paid dividends... both for the military and the people finding holes in its defenses. HackerOne has revealed the results of the Hack the Air Force 2.0 challenge from the end of 2017, and it led to volunteers discovering 106 vulnerabilities across roughly 300 of the USAF's public websites. Those discoveries proved costly, however. The Air Force paid out a total of $103,883, including $12,500 for one bug -- the most money any federal bounty program has paid to date.
Intel currently facing 32 class-action lawsuits for Spectre and Meltdown
Yesterday, Intel expanded its bug bounty program to catch more issues like the extensive Meltdown and Spectre CPU flaws, but that was too little, too late for some chip owners. We knew three class-action lawsuits were filed in early January days after the vulnerabilities were publicized, but according to an SEC filing, the total has grown to 30 multi-party suits by customers and two securities suits. Most argue that Intel violated securities laws when it assured its products were safe to use, which the Meltdown and Spectre flaws revealed to be untrue.

Intel expands bug bounty to catch more Spectre-like security flaws
To say Intel was caught flat-footed by the Meltdown and Spectre flaws would be an understatement. However, it has a potential solution: enlist more people for help. It's widening its bug bounty program to both include more researchers and offer more incentives to spot Meltdown- and Spectre-like holes. The program is now open to all security researchers, not just by invitation, and includes sweeter rewards for discovering exploits. You now get up to $100,000 for disclosing general security flaws, and there's a new program dedicated to side channel vulnerabilities (read: issues like Spectre) that offers up to $250,000 through December 31st, 2018.

Intel told Chinese firms of Meltdown flaws before the US government
Intel may have been working with many tech industry players to address the Meltdown and Spectre flaws, but who it contacted and when might have been problematic. Wall Street Journal sources have claimed that Intel initially told a handful of customers about the processor vulnerabilities, including Chinese tech companies like Alibaba and Lenovo, but not the US government. While the chip giant does have to talk to those companies to coordinate fixes, the Chinese government routinely monitors conversations like this -- it could have theoretically exploited the holes to intercept data before patches were available.

Blizzard games were vulnerable to a remote hijacking exploit
Fans of Blizzard games might have dodged a bullet. Google security researcher Tavis Ormandy has revealed that virtually all the developer's titles (including Overwatch and World of Warcraft) were vulnerable to a DNS rebinding flaw that let sites hijack the Blizzard Update Agent for their own purposes. Intruders had to do little more than create a hostname their site was authorized to communicate with, make that resolve to the target of their choice (such as the victim's PC) and send requests to the agent. From there, they could install malicious files, use network drives or otherwise create havoc.

Uber security flaw compromised two-factor authentication
Two-factor authentication only works if it's strictly enforced in software, and it sounds like Uber might have fallen short of that goal for a while. In a chat with ZDNet, security researcher Karan Saini has revealed a flaw in Uber's two-factor verification that reportedly rendered it useless. Saini has been keeping the exact details of the exploit under wraps to prevent abuse, but it revolved around a vulnerability in how Uber authenticates users when they sign in. The net effect was clear: an intruder might have only needed your username and password to sign in, giving them the chance to swipe personal info or misuse services.
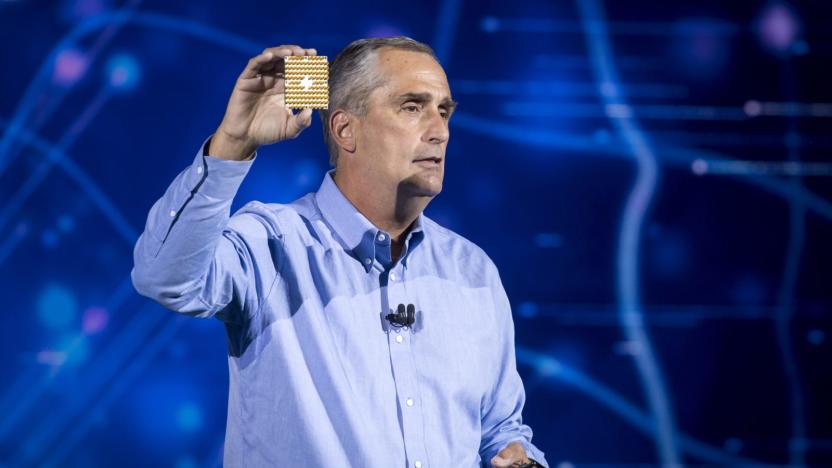
Intel pledges transparency after Spectre, Meltdown vulnerability
The last week or so has seen a lot of activity around Meltdown and Spectre, two CPU flaws in modern chips from the likes of AMD and Intel. Apple, Microsoft and Google have provided interim fixes for their respective hardware, but it will take much more than simple patches (that can cause more harm than good) to truly eradicate the issue. Just a few hours after Intel revealed that there may be more slowdowns from its Meltdown processor fix, the company's CEO Brian Krzanich has written an open letter to further detail the steps Intel is taking to deal with the issues.

NVIDIA updates video drivers to help address CPU memory security (updated)
It's not just your processor and operating system that need patches for the Meltdown and Spectre memory vulnerabilities -- your graphics card does, too. To that end, NVIDIA has started releasing updated drivers that help protect against the CPU vulnerability. All its GeForce, Quadro, NVS, Tesla and GRID chips are immune to Meltdown and Spectre themselves, but the code could leave CPUs open to two Spectre variants. The new software immediately mitigates one Spectre flaw, and NVIDIA is promising future mitigations as well as eventual updates to address the second.

Microsoft says security fixes will noticeably slow older PCs
It's been clear for a while that the fixes for the Meltdown and Spectre memory vulnerabilities would slow down PCs, but just how bad is the hit, really? Microsoft has run some benchmarks, and it's unfortunately bad news if your system is less than fresh. While the patches for Meltdown and one variant of Spectre will have a "minimal performance impact," fixing a second Spectre variant through low-level microcode imposes a tangible speed penalty -- and it's particularly bad on systems released around 2015 or earlier.


