After US Capitol assault, a different cybersecurity threat emerges
In which we acknowledge the big cyber-elephant in the room.
We may receive a commission on purchases made from links.
Among so many things that are horrific about last week's deadly attack on the Capitol building was the fact that it was planned for weeks. In the open. With that in mind, we are left wondering about the cybersecurity questions raised in the aftermath.
When Engadget asked a physical cybersecurity penetration tester what he'd do if assigned to "pentest" the Capitol building during the riot, the response wasn't comforting. His excitement was palpable. "Oooh, so many cool attacks you could do," he said, and began listing equipment he'd bring.
But hold on a second: before getting to the attacks, we need to have some real talk about who would do such a thing. It's a question we're all asking about many aspects of this unbelievably painful moment.
If "nation-state actor" is your go-to answer, you're echoing the focus of nearly everyone else pontificating right now about threat modeling. As in, who would take advantage of unfettered access to hastily abandoned computers and devices left mostly in offices that don't have surveillance cameras?
Everyone's talking about a foreign adversary, then either hyping that threat, or dismissing it.
No one is talking about a domestic adversary. And when it comes to cybersecurity issues, Congressional safety, national security, and January 6... that's a problem.
The calls are coming from inside the house
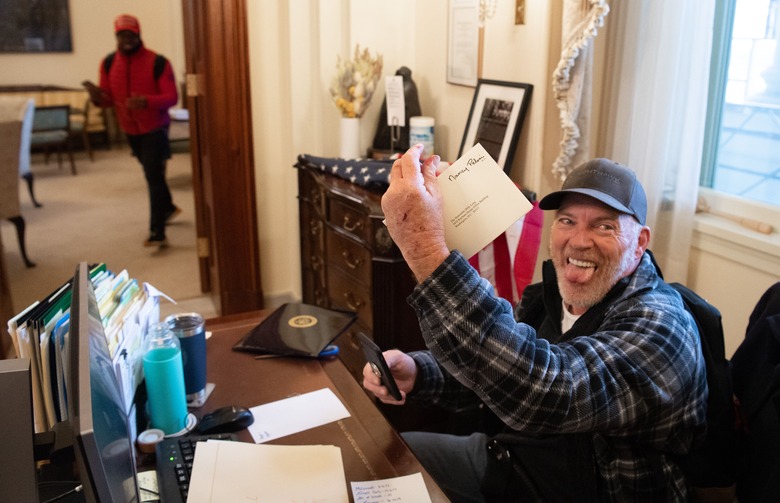
We all saw the images: threatening notes left on computers, the House Speaker's computer screen unlocked with email open, MAGA terrorists looting — and taking electronic items yet to be identified. Reports, with probably more to come, of laptops stolen from the offices of Speaker of the House Nancy Pelosi and Senator Jeff Merkley. Now there are as-yet unconfirmed reports that several classified laptops were stolen during the mob's assault on the Capitol — left open and logged onto the classified SIPRNet network.
Initial impressions of the January 6 attack made it seem like the violent mob were costumed, unstable, virulently racist clowns that were just doing it for the 'gram. Infosec got the quick impression that they "were unsophisticated opportunists who were more interested in taking selfies than infiltrating computer networks."
As we now know, this masked an organized, well-equipped, and pre-planned reality. Low-key, armed, ex-military teams with flexicuffs. Militia ("Oath Keepers") on radios and in body armor, whose forums overflow with fantasies and plans to execute people. In just one example of preparation, attackers knew where to find (Black, Democrat) House Majority Whip James Clyburn's unmarked secondary office — beelining to where he was supposed to be at the time.
Weeks of advanced notice, a loud and unpredictable mob as cover, and a plan to breach and occupy the Capitol building. It makes sense to think of it as an opportunity for a foreign adversary to tag along, blend into the crowd and see what they could get.
Yet one current cybersecurity defense contractor who specializes in offense (attacks) dismissed the Capitol as a valuable (or even practical) nation-state target outright. Speaking with Engadget under the condition of anonymity, they explained that it's not that a whole host of attacks like malware, device cloning, spyware, keyloggers and other invasions weren't possible — for the most part, they were. "The thing you aspire to in cyber espionage," they explained, "is something like SolarWinds. No one knew they were compromised and being attacked. With the Capitol riots, you know everything is going to be considered compromised now"
In addition, they said any competent attacker knows a high-profile attack such as January 6 is going to bring post-compromise forensics. That means any 0-day — costly and valuable malware or other attacks — will be "burned," as in discovered, lost, rendered useless, and exposed. Plus, an operation within the violence, riots, and chaos risks burning cover as well. Any information they get is also old; much of it is relevant only on "day zero" as they phrased it. For a nation-state actor, it's apparently not considered worth blowing money, cover, and resources for things that aren't state secrets.
"It's too many risks for a low-value target," they told Engadget.
By calling the Capitol building and its powerful lawmaking, line-of-succession inhabitants a "low value" target, they explained that it's an unclassified network that deals with unclassified information. I asked how this was different from the 2014 breach of the White House's unclassified network, which pundits largely wrote off but horrified government infosec insiders. "That was different because the attackers had persistent access over time and, the most important thing is, no one knew they were compromised." Which explains why ultimately, those attackers were more successful than people initially believed.
This is when we'd shrug and write off the cybersecurity risks via the Capitol riots as "low" — which many have done. That would be a mistake, one made by an assumption in one's risk assessment: namely, that the question of "who would do such a thing" ended there.
"The Capitol, its unclassified-office-only laptops... the information is unclassified but still sensitive," the contractor stressed.
Red team Nazis
The kind of information you'd get from a presentation laptop, or House Speaker's emails, or their aide's notes would not be "top secret." It could reveal schedules, inauguration plans, personal information, operational details, contact lists, details from presentations, and more. Like info that could be used for phishing, impersonation, and worse.
A domestic attacker let loose in the Capitol building might be less refined and have less resources than a nation-state threat, to be sure. Yet for attackers that want to terrorize and kill individuals or a group of lawmakers, what's on that building's network and its hardware certainly makes it a "high value" target.
Maybe not valuable stuff for Russian spies; they have SolarWinds, after all. But it's definitely of value to those hackers whom the contractor we spoke with candidly described as "those Nazi red team assholes who go to DEF CON." I immediately knew what they meant. It is uncommon, unwelcome, and seldom discussed, but white supremacist, Trump-army hackers exist ("Oath Keepers" go to hacker conferences). And as you'd expect after last week's traumatic attack on the Capitol, hacker con attendees are worried.
In good news, DEF CON isn't playing. When reached for comment, Founder of Black Hat & DEF CON Jeff Moss gave Engadget the following statement:
"DEF CON – still anti-Nazi.
We're still against violence, harassment, intimidation, abuse and unkind treatment of your neighbors. Showing evidence of any of these will still get you thrown out of DEF CON, regardless of the reason. Making members of our community feel unsafe, unwelcome or unable to enjoy the event is, and will always be, enough reason to show you the door.
This applies to everyone. Attendees, staff, volunteers, speakers. Everyone.
DEF CON is a community project, and our community includes all kinds of people. We take very seriously our responsibility to see that everyone is treated with respect. Everyone willing to abide by that basic principle is welcome. Anyone who isn't should find another event."
Other hacker conferences should do the same — rather, they should've done the same long ago. With so much of this, a little bit of prevention would have gone a long way toward everything from saving lives to mitigating terror and destruction.
It's a good feeling to see DEF CON step up — and the team acknowledged the challenges of dealing with a belligerent population that will game systems to avoid detection and accountability. Unfortunately, that's what it takes, and one of the things that got us in this terrible situation is that unlike DEF CON, not everyone is willing to play "Whack-A-Fascist."
In 2018, the HOPE conference (Hackers On Planet Earth) was attended by some whom press described as "men with far-right paraphernalia, including Trump hats and Pepe frog patches."
The pro-Trump attendees attacked and serially harassed researcher Matt Blaze, who gave a presentation on securing the vote. One also rushed the stage at the conclusion of Chelsea Manning's interview. This was all in addition to multiple in-person threats and verbal abuse to speakers and attendees over the course of the conference. At the end of HOPE 12, it came out that a HOPE speaker worked in concert with the alt-right attendees, and the conference was condemned for its organizers refusal "to remove fascist and white nationalist disruptors from HOPE 2018." When Engadget reached out to HOPE for comment via email, the organization said "We have gotten a ton of support and good ideas from the community, and we're much better prepared to deal with this sort of thing." Adding, "What we can commit to is remaining vigilant, developing our staff, and always being open to ideas from the community... Together with the staff of 2600, we have put up a site called usa.wtf, which can also be considered our response."
A cyberhouse in cyberdisarray
Let's just hope the House of Representatives and Senate — which each have their own Sergeant-at-Arms offices overseeing cybersecurity — can think beyond the concept of "foreign adversary" and acknowledge domestic, white supremacist terrorist hackers as an extremely serious threat. Downplaying or ignoring domestic cyber-adversaries, vis-a-vis everyone's first impressions about the Capitol mob, is likely to be a deadly mistake.
Of course, things don't look cyber-peachy for a Capitol in cyber-disarray. "And while the Senate and House each build off of their own shared IT framework," reported Wired, "ultimately each of the 435 representatives and 100 senators runs their own office with their own systems."
Speaking with retired Senate sergeant-at-arms Frank Larkin, the outlet learned "this also means that there aren't necessarily standardized authentication and monitoring schemes in place... [and] representatives and senators have varying levels of cybersecurity competence and hygiene." It's no doubt complicated now that Senate Sergeant at Arms Michael C. Stenger, House Sergeant at Arms Paul D. Irving (as well as Capitol Police Chief Steven Sund) have resigned.
On top of all that, assessment and unification of Congressional cybersecurity appears to have been a stalled work in progress. "In March 2019, Sens. Tom Cotton, R-Ark., and Ron Wyden, D-Ore., asked the Senate Sergeant at Arms for an annual tally of when its computers and smartphones have been breached in order to better inform congressional cybersecurity policy," reported CyberScoop last week. "The Senate Sergeant at Arms has yet to provide the information sought in the letter, according to a Wyden spokesperson."
At any rate, one day after the deadly coup attempt House Chief Administrative Officer Catherine Szpindor sent a notice to House members saying "At this time, there have been no indications that the House network was compromised," and that the CAO's Office of Cybersecurity had issued commands to lock computers and laptops, and shut down "wired network access" during the occupation.
So, uh, there's that at least.
Many reprehensible, dark, and unforgivable acts were committed on January 6. Including one suicide, six people are dead. Gallows were constructed. Attackers sang the 'Star-Spangled Banner' as they beat a Capitol police officer on the ground. NYT photographer Erin Schaff screamed for help as she was assaulted and no one came — imagine hearing that from behind a barricaded door, or while you are being chased by a literal lynch mob.
It's revolting that the attackers felt so safe and righteous in their violence that they documented everything. This detail was a mind-boggling spectacle for the corners of infosec that practice, teach, and pride themselves on social engineering and "opsec" (operational security, or covering your tracks).
Fortunately for us, monsters who fail at opsec always succeed at masterminding their own tragedies. And it is damn satisfying to watch them getting caught and arrested as a result.