Twitter botnet quotes 'Star Wars' from the middle of the sea
350,000 fake, Windows Phone-using accounts show the challenges of bot detection.
Along with trolls and bullies, one of Twitter's biggest problems is bots — automated accounts that puff up follower numbers, troll users or turn fake news into trending topics. Researchers investigating botnets found maybe the strangest one ever: 350,000 that tweet only random Star Wars quotes from Windows Phone devices. While that's actually kind of amusing, the researchers say that it reveals "profound limitations of existing bot detection methods" and shows the potential risks that hidden networks pose to the Twitter ecosystem.
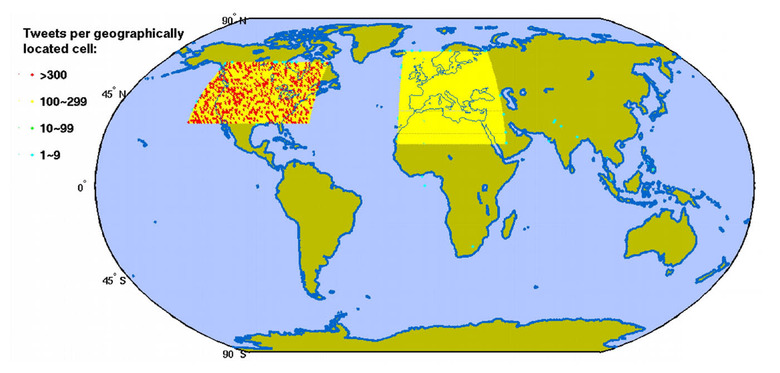
The University College London team discovered the so-called Star Wars botnet purely by chance. They started by downloading data from six million random English-speaking accounts (about one percent of all users) including their last 3,200 tweets and location information. After plotting that on a map (below), they noticed that around 23,000 tweets originated in uninhabited regions, including deserts and oceans, in two distinctively square geographic regions.
They concluded that someone had created a botnet and assigned fake users to random areas within two geographical blocks, "perhaps as an effort to pretend that the tweets are created in the two continents where Twitter is most popular," the team wrote. They manually checked the text in each tweet, and found that, bizarrely, all included random text from Star Wars novels, often starting or concluding with an incomplete word:
Luke's answer was to put on an extra burst of speed. There were only ten meters #separating them now. If he could cover t
Hashtags appeared on random words, or used terms like "#teamfollowback" associated with gaining followers. Each bot had a specific user ID range, tweeted less than 11 times, had fewer than 10 followers and used "Twitter for Windows Phone" as the source of the tweets.
Using that information, the team manually identified 3,244 bots with a high amount of certainty, then created a machine learning algorithm that found over 350,000 in total, all controlled form a central "botmaster." When the botnet was first created on June 20th, 2013, it tweeted 150,000 times daily, then suddenly stopped on July 14th, 2013, and hasn't been tweeting since. However, the bots were still on Twitter at the time of the study and have could easily been reactivated.
It's well-known that there are millions of botnets out there, but the most interesting (and disturbing) thing about this one, says the team, is how easily it was able to hide. To do that, it kept a fairly low profile, hence the low user counts and number of tweets. And the Star Wars quotes, while random, "helped the tweets appear [to be] ... a real human's language," they wrote. Furthermore, the bots used realistic-looking profiles that often included photos.
All of that helped them circumvent Twitter's regular bot detection methods and stay on the site. From there, they could have been re-activated and used for schemes like spamming, fake trending topics, astrotufing, fake followers, opinion manipulation and more. For instance, in a separate study, researchers from Oxford University believe that pro-Trump bots rampaged on Twitter, spreading false stories to influence voters. It's also possible that the botnet was used to test Twitter's defenses, so that its creators could build a better one in the future.
The researchers were lucky to find the botnet, but say future ones could easily be programmed to escape their detection methods. That's why, they say, new protections are needed "to detect other hidden bots and future bots that will look more and more like normal uses." Thanks perhaps to publicity on the research (which is awaiting peer review), Twitter seems to have scrubbed the Star Wars botnet — the only trace I could find of it was a search entry in Google (above).