T-Mobile, AT&T customer account PINs were exposed by website flaws
In both cases, the issue happened when another company tried to verify account info.
As if news of a recent breach leaking T-Mobile customer data to attackers weren't bad enough, Buzzfeed News highlights a pair of issues that could've revealed PIN numbers for customers of T-Mobile and AT&T. The security flaws were uncovered by two security researchers, Ryan aka "Phobia" and Nicholas "Convict" Ceraolo.
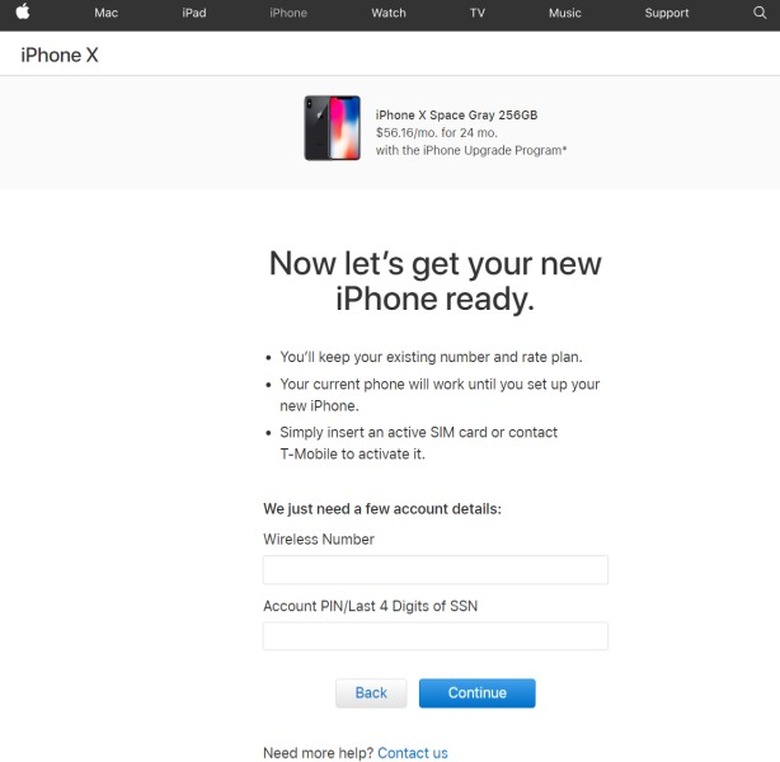
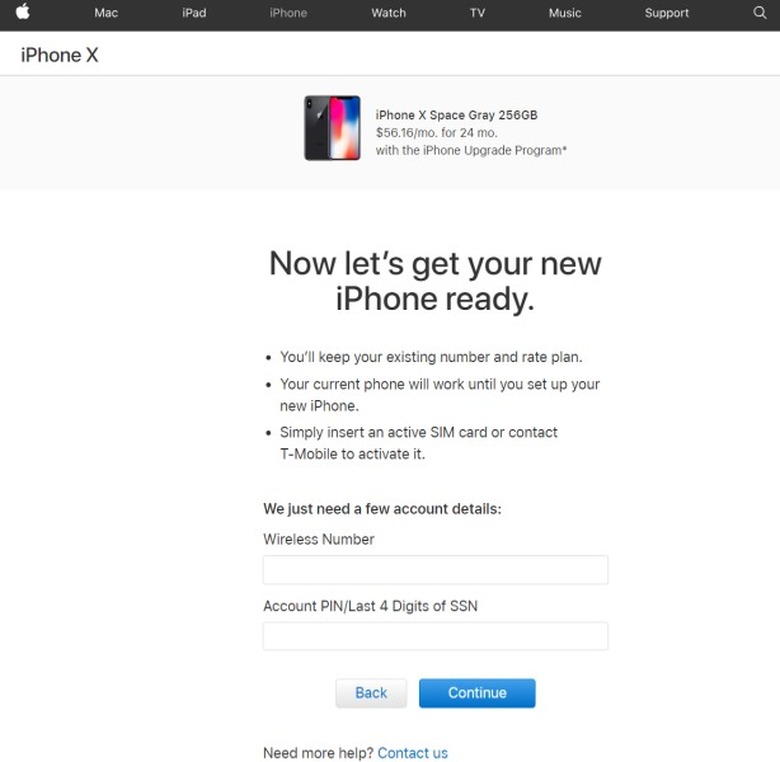
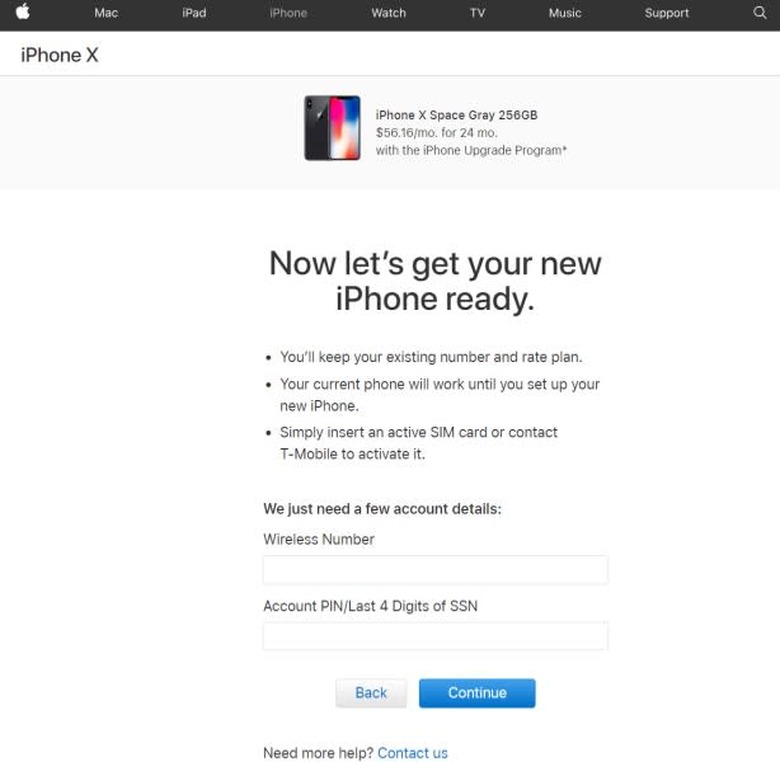
The T-Mobile issue occurred via its link to Apple's online store, where they found that a page in the middle of the iPhone purchasing flow would allow an interested party unlimited attempts at guessing an account PIN or last four digits of the account holder's social security number. Given unlimited tries for a safety feature that's probably four digits with no rate limiting lets hackers run through all the possibilities quickly.
As the report mentions, once they find the right one, it could allow someone to take the number and then use it to hijack a victim's SIM card and phone number. Once you have that, it's easy to hack any service that relies on text messages to send two factor-authentication codes as a primary method or backup, which is what we've seen happen to people like @Deray, or owners of a slew of Instagram accounts. That's some of the reasons why, if possible, it's better to use a two-factor system that relies on a code generated by an app, sent via push notifications or, even better yet, is tied to a physical key.
For AT&T, a similar vulnerability occurred on one of the pages where customers could file insurance claims via Asurion that asked for a PIN, but allowed unlimited attempts and did not put any limit on the rate. Apple and Asurion told Buzzfeed News that the issues have been fixed now that they've been brought to their attention, but that they existed at all shows why it's important to have multiple layers of account security — vulnerabilities can exist even in places that you wouldn't expect.