badpassword
Latest

If hacking back becomes law, what could possibly go wrong?
Representative Tom Graves, R-Ga., thinks that when anyone gets hacked -- individuals or companies -- they should be able to "fight back" and go "hunt for hackers outside of their own networks." The Active Cyber Defense Certainty ("ACDC") Act is getting closer to being put before lawmakers, and the congressman trying to make "hacking back" easy-breezy-legal believes it would've stopped the WannaCry ransomware.

The Facebook president and Zuck's racist rulebook
If a political campaign is an engine then propaganda is its oil, and its gas is the medium of communication with voters. The hacking of the DNC and tonnes of raw crude in propaganda mined out through WikiLeaks, Breitbart and Daily Stormer was black gold for the Trump campaign.

Trump’s cybersecurity order delivers nothing but more surveillance
Remember that cybersecurity executive order we anticipated from the Trump administration, which seemed to quietly disappear in January? The already-delayed deadline for Trump's EO on "the cyber" and his promise to create a cyber-review team passed last month. Many were wondering if it would fade off into oblivion like a tyrant's hairline -- or show up suddenly to drop cyber-bombs on someone's vacant cyber-tarmac.
The enduring myth of the hacker boy-band
Last week, Wired magazine published a sprawling feature on a group of young hackers the magazine claimed would "make us or break us" with their "exceptional talent." The article fawningly profiled each member of a group of Northeastern University college students who would "soon dominate technology -- and shape our future."

The war for the soul of the password
Obviously, whoever invented the password system was a jerk. And whoever started adding all those little rules for password creation is a sadist. Not the kind of sex-positive sadist with a flag for their kink and a set of consensual negotiation rules that ensure password creation is hot for everyone involved. No, we're talking about the kind of sadist that simply likes watching people suffer as they're told to add special characters, but not dollar signs or exclamation points because... reasons.

Turns out, pacemaker security is terrifying
The hacker who uses her wizard powers to get rich by manipulating stocks is a tired Hollywood trope. But that doesn't mean some hackers don't dream about making the fantasy come true, or that the ridiculous vulnerabilities necessary to facilitate such a thing don't exist. Some hackers do indeed have that dream. And reductive Hollywood-style vulns in critical financial (and other) systems are as real as they are plentiful in our world of crap security.
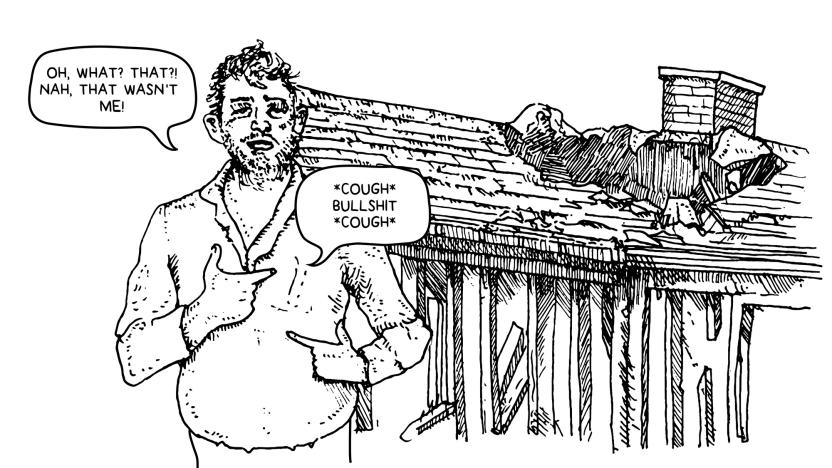
Dallas siren hack: Coming to a city near you
At 11:42 PM last Friday night in Dallas, suddenly and for no apparent reason, what locals call the 'tornado sirens' went off. All of them. It was a clear, calm night; no foul weather presaged the blare of an emergency system so loud it's meant to wake sleepers inside their houses. When the 156 sirens continued to go off in repeating 90-second cycles, seemingly without end, people started to worry about being bombed.
Good luck finding a safe VPN
If you're most people, you just found out about the FCC's internet privacy rules by way of their untimely demise. Thanks to the FCC's new chief, Congress, and Donald Trump, ISPs are now free to track you like crazy and sell your data to the four directions. As a result, interest in VPNs exploded overnight.

When the 'S' in HTTPS also stands for shady
Just when we'd learned the importance of HTTPS in address bars, spammers and malicious hackers have figured out how to game the system. Let's Encrypt is an automated service that lets people turn their old unencrypted URLs into safely encrypted HTTPS addresses with a type of file called a certificate. It's terrific, especially because certificates are expensive (overpriced, actually) and many people can't afford them. So it's easy to argue that the Let's Encrypt service has done more than we may ever realize to strengthen the security of the internet and users everywhere.
FCC: Your cybersecurity isn't our problem
The new FCC chairman hasn't wasted any time getting down to business. That is, the business of burning consumer privacy and security to the ground. New Trump appointee FCC Chairman Ajit Pai has suspended the agency's consumer data privacy rules indefinitely. Before they even went into effect. He's basically holding the safeguards underwater while two Republican-backed congressional resolutions come in for the kill.
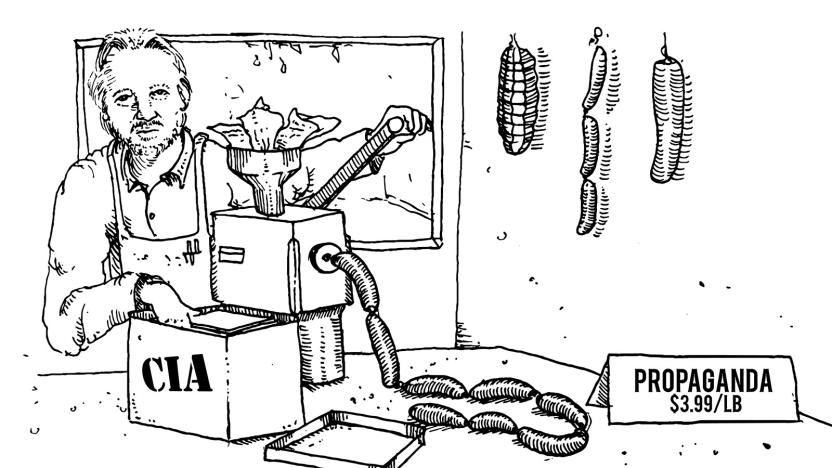
WikiLeaks CIA cache: Fool me once
This week's poorly conceived distraction from Trump and Putin sittin' in a tree was brought to us by WikiLeaks, which dumped 8,761 documents of the CIA's hacking arsenal online for all to see. The leak factory didn't even bother trying to play coy -- it actually made the "Vault 7" password an anti-CIA JFK quote about destroying the agency. Hilarity ensued. Well, if you think it's funny when the press parrots WikiLeaks' misleading claims wrapped in PR spin.
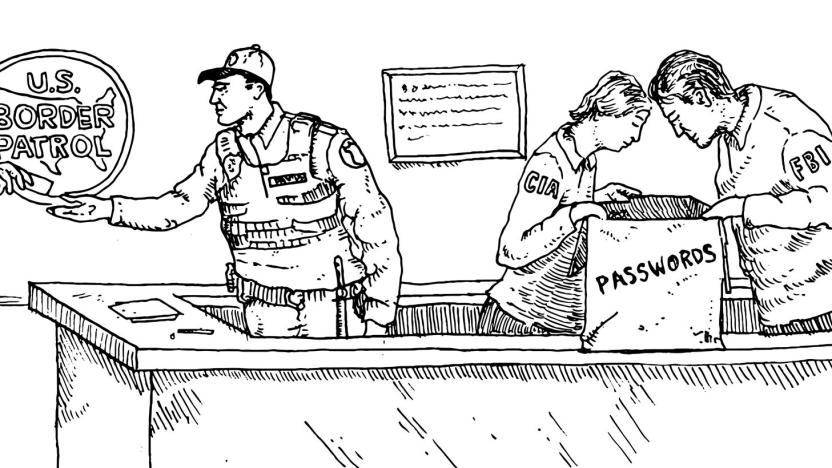
The Border Patrol can take your password. Now what?
There's a whole world of bad security advice going around about traveling in and out of the United States. It's largely because under the Trump Administration there has been an uptick in Customs and Border Protection agents searching the phones and digital devices of travelers at airport checkpoints.

How used cars became a security nightmare
Application security for connected cars is far less mature than anyone should be comfortable with. This was clear at the RSA information security conference last week in San Francisco, where two presentations demonstrated different ways cars can be remotely controlled or even stolen by non-owners. All because the people designing connected car apps literally didn't think things through and consider the possibility of second owners -- or hackers.

When vending machines attack (a university)
We are marching toward certain doom at the hands of an angry Skynet of our own invention. Need proof? This week a school was attacked by its own soft drink vending machines. You read that right.
Inauguration-protest arrests lead to Facebook data prosecution
If you attend a protest in Washington, D.C., nowadays, better plan on leaving your cellphone at home. That is, unless you want police to confiscate it, mine it for incriminating information and then gather even more data from their BFF -- Facebook. At least one person arrested during protests on Inauguration Day got an email from Facebook's Law Enforcement Response Team alerting them that investigators wanted access to their data. Another received a Facebook data subpoena.
The way to a man's heart is actually through WiFi
They say you can't hide what's in your heart, but the saying is doubly true for an Ohio man whose pacemaker data has been used to indict him on felony charges of aggravated arson and insurance fraud.

A whole new low in government trust
Our country changed so quickly in the past week that it feels like the pod doors have been sealed shut and an antigravity switch flipped inside our borders. From the outside, it probably looks like a snowglobe scene of hell. The Doomsday Clock advanced, "thanks to Trump," and it's now only two and a half minutes to nuclear midnight, while The Economist's Democracy Index downgraded the US from "full democracy" to "flawed."
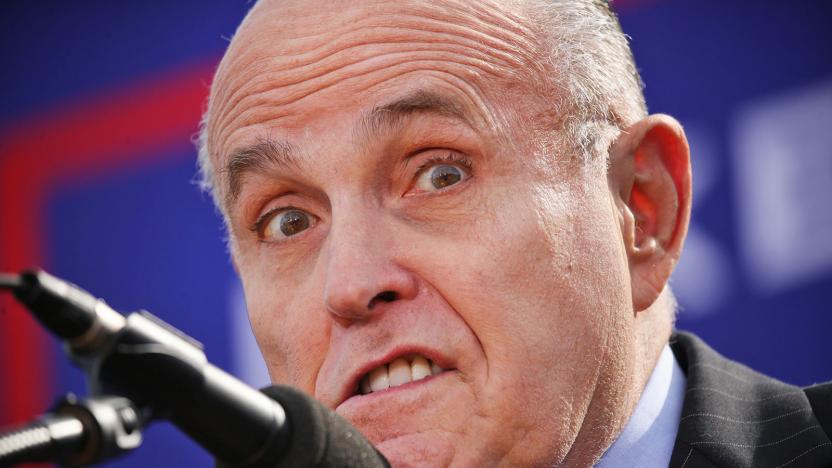
Giuliani as Trump's cybersecurity adviser is an unfunny joke
I had just finished hacking the Gibson when I heard the news: Rudy Giuliani, the guy who said he was gonna solve cybersecurity, had just been named Trump's cyber adviser. I hopped onto our hacker mafia's government-proof encrypted chat app to make sure everyone knew that we were in real trouble. When I got no response from Mr. Robot or Anonymous, I got my rollerblades on and got out of my mom's basement as fast as possible. I dialed our ringleader with a secret, anti-authority encrypted phone app while hacking all the traffic lights between here and his mom's basement as I raced over. When he picked up I blurted, "Stop hacking baby monitors and trying to crash the stock market!"
FTC vs D-Link: All bark, no bite
Most routers are bad. Bad to their little router bones. But they were made that way. And when you get one of the bad ones in your home, they sit there like little privacy and security time bombs, just waiting to become conduits of evil in your house. You think I'm joking. But if you look at the state of router security, then you will know this is a big problem. And it's one that's nearly impossible for normal people to fix.

Soon cops will search your phone just like your car
Imagine a routine traffic stop during which the officer has the legal right to search not just your car, but your phone too. That's where we're likely headed: A Florida court recently denied Fifth Amendment protections for iPhone passcodes, saying suspects must now reveal them to police. The decision came after a previous court had ruled that a suspect couldn't be compelled to give up the key to unlock his phone based on laws against self-incrimination.
