malware
Latest

Atlanta ransomware attack may cost another $9.5 million to fix
The effects of the "SamSam" ransomware attack against Atlanta's government were much worse than it seemed at first glance. To start, city Information Management head Daphney Rackley revealed at a meeting that more than a third of Atlanta's 424 necessary programs were knocked offline or partly disabled, and close to 30 percent of those affected apps were "mission critical" -- that is, vital elements like the court system and police. The government initially reckoned that essential programs were safe.

'WannaCry hero' faces more federal malware charges
Marcus Hutchins, the cybersecurity researcher credited with helping stop last year's WannaCry virus, is facing four new charges related to malware he allegedly created to steal financial information. Now, the FBI says Hutchins lied about creating the malware called Kronos, and that he conspired with others to promote it online, including via YouTube.

Data-stealing router malware bypasses web encryption
A recently discovered strain of router malware appears to be much worse than thought. Cisco Talos has learned that VPNFilter can not only render devices unusable, but can bypass the SSL encryption you often see on the web. A module in the malware intercepts outgoing web requests to turn them into non-secure (that is, basic HTTP) requests, helping it steal sign-ins and other sensitive data when possible. It can also use man-in-the-middle attacks to insert hostile JavaScript into outside websites, and target devices beyond the router itself, such as PCs on the local network.

FBI links North Korea hackers to two more malware attacks
The FBI and the Department of Homeland Security have linked more malware with North Korean hackers. The agencies say state-backed hackers called Hidden Cobra have likely used remote access tool Joanap and server message block worm Brambul to infiltrate the global media, aerospace, financial and critical infrastructure sectors. The attacks are part of a North Korea cyberattack campaign that has persisted since at least 2009, the agencies wrote in a Technical Alert.

Report finds Android malware pre-installed on hundreds of phones
Even if you're careful about avoiding sketchy websites and apps, there's nothing you can do if your smartphone has malware built in. That's actually the case with hundreds of different smartphones, according to Avast Threat Labs. The researchers found adware installed mostly on devices not certified by Google from manufacturers like ZTE, Archos and myPhone. Users with affected phones will see popup ads and other annoying problems, and because the adware is installed on a firmware level, it's incredibly difficult to remove.

North Korea-linked hackers targeted defectors with Android spyware
When Android malware slips into the Google Play Store, it's usually there to push unwanted ads or perpetuate a scam. McAfee researchers, however, have discovered something more sinister. A North Korean group nicknamed Sun Team recently posted three apps in Google Play that were used to target defectors from the authoritarian country. The attackers contacted people through Facebook in bids to have them install seemingly innocuous "unreleased" apps for food and security. When installed, the rogue apps would send contacts, photos and text messages to the intruders using Dropbox and Russia's Yandex to both upload data and send commands.

Android malware returned to Google Play with just a name change
Google has done a lot to thwart Android malware in recent months, but it's apparent there's still some work to do. Symantec recently discovered seven previously removed rogue apps that resurfaced on Google Play simply by using a new publisher and new app names. The titles masqueraded as productivity apps and would even use official Google imagery to hide their origins, but would push ads and scam websites if they were allowed to stay for four hours.

Sophisticated Android malware tracks all your phone activities
An advanced type of malware can spy on nearly every Android smartphone function and steal passwords, photos, video, screenshots and data from WhatsApp, Telegram and other apps. "ZooPark" targets subjects in the Middle East and was likely developed by a state actor, according to Kaspersky Lab, which first spotted and identified it.

Intel's new malware scanner will be easier on your CPU
Since the full impact of Spectre and Meltdown became clear earlier this year, Intel has been making a big effort to reassure its customers that security is its top priority. To that end, the company has announced Intel Threat Detection Technology (TDT), which aims to fortify against malicious attacks without affecting CPU performance.

Avast claims its secure browser is 30 percent faster than yours
Avast has updated its browser to give users greater control over their online privacy. According to the company, its renamed Avast Secure Browser (formerly SafeZone) is designed to plug the security gaps that result from users' misplaced protection expectations. Features such as Stealth Mode, HTTPS Encryption, anti-tracking and anti-fingerprinting have been designed to account for the 69 percent of UK consumers who believe standard private-browsing modes will anonymize their identity, and the 81 percent who believe their browser would alert them to web-based threats, such as malicious cryptomining and extensions.

Android malware found inside seemingly innocent QR code apps
Google is getting better at keeping Android malware out of the Play Store, and that's leading attackers to use more sophisticated disguises for their rogue apps. SophosLabs has proof: it just detailed a recent ad-spawning malware strain, Andr/HiddnAd-AJ, that slipped into Google Play through innocent-looking QR code and compass apps. While that's nothing new by itself, the malware used a pair of tricks to feign innocence. The hostile code was buried in what looked like a regular Android programming library, and it didn't kick in until 6 hours after you've installed it.

Suspect arrested for cyber bank heists that amassed $1.2 billion
Europol announced today that the suspected leader of an international bank heist scheme has been arrested. The arrest was a result of an investigation that involved a number of cooperating law enforcement groups including the Spanish National Police, Europol, the FBI and the Romanian, Belarusian and Taiwanese authorities. The person was arrested in Alicante, Spain.

Atlanta government computers hit by ransomware
The last victim affected by ransomware is the city government of Atlanta, GA. The ninth-largest metro area in the US isn't able to do things like process payments or provide access to courthouse information because some systems are locked down. During a press conference, mayor Keisha Bottoms and newly-appointed COO Richard Cox said that they're working with the FBI, DHS, Microsoft and Cisco to find out what data has been potentially been compromised.The local NBC affiliate reports a ransom note included with the SamSam ransomware is demanding about $51,000 in bitcoin to restore the systems. If it is SamSam, it's part of a family of malware has been active against many government and healthcare systems since late 2015. In January, Talos noted that its makers had already netted over $325,000 in ransom sent to one bitcoin wallet. This particular attack isn't spreading on the level of 2017's NotPetya/WannaCry, but its apparent ability to target critical systems where the owners are likely to pay makes it even more troublesome, spreading first through vulnerable servers and then onto Windows desktops. The Atlanta government said it will be open for business in the morning, and that infrastructure like public safety, water and the airport are unaffected.

Sophisticated malware attacks through routers
Security researchers at Kaspersky Lab have discovered what's likely to be another state-sponsored malware strain, and this one is more advanced than most. Nicknamed Slingshot, the code spies on PCs through a multi-layer attack that targets MikroTik routers. It first replaces a library file with a malicious version that downloads other malicious components, and then launches a clever two-pronged attack on the computers themselves. One, Canhadr, runs low-level kernel code that effectively gives the intruder free rein, including deep access to storage and memory; the other, GollumApp, focuses on the user level and includes code to coordinate efforts, manage the file system and keep the malware alive.

Cryptocurrency mining site hijacked millions of Android phones
Smartphone users are just as vulnerable to cryptocurrency mining hijacks as their PC counterparts, and sometimes on a dramatic scale. Malwarebytes has detailed a "drive-by" mining campaign that redirected millions of Android users to a website that hijacked their phone processors for mining Monero. While the exact trigger wasn't clear, researchers believed that infected apps with malicious ads would steer people toward the pages. And it wasn't subtle -- the site would claim that you were showing "suspicious" web activity and tell you that it was mining until you entered a captcha code to make it stop.
Google credits AI for stopping more rogue Android apps in 2017
Google likes to boast of its ability to shut down Android malware, and it apparently has good reason to brag about 2017. The company took down over 700,000 apps that violated Play Stores policies last year (a 70 percent increase over 2016), and it was considerably better at pulling rogue apps in time to avoid infections. Thanks to a slew of new machine learning techniques, it caught 99 percent of apps with "abusive contents" before anyone had installed them.

ATM 'jackpotting' hacks reach the US
For some ATM thieves, swiping card data involves too much patience -- they'd rather just take the money and run. The US Secret Service has warned ATM makers Diebold Nixdorf and NCR that "jackpotting" hacks, where crooks force machine to cough up large sums of cash, have reached the US after years of creating problems in Asia, Europe and Mexico. The attacks have focused largely on Diebold's front-loading Opteva ATMs in stand-alone locations, such as retail stores and drive-thrus, and have relied on a combination of malware and hardware to pull off heists.
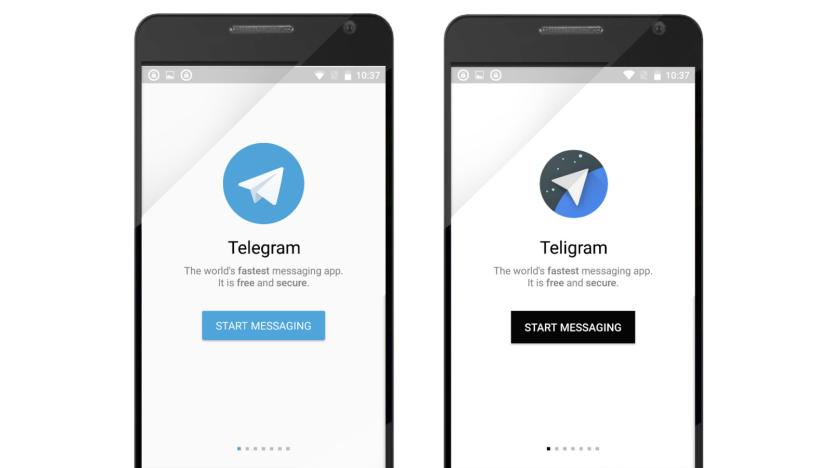
Telegram targeted by fake apps that serve malware and ads
Make sure you check an app's name before you download it: Telegram, for instance, had an evil twin on Google Play named "Teligram." According to Symantec, which discovered its existence, its profile and description on the store mirrored the authentic app's, with the only difference being the slightly altered logo. It was also branded as "New version updated" in an effort to fool users into thinking it's the new version of Telegram. And it probably could've fooled people, too, since it actually works as a messaging platform.

Malware creator charged for 13-year spying spree
You don't need an elaborate crime ring (or a government agency) to write malware that spies on others -- sometimes, just one person can be responsible. The US Department of Justice has charged Ohio resident Philip Durachinsky with 16 crimes for allegedly writing malware, nicknamed "Fruitfly," that gave him unfettered access to the PCs of "thousands" of individuals and institutions between 2003 and January 2017. Reportedly, he not only stole sensitive data to use for fraud and blackmail (such as logins, embarrassing chats and medical records) but took screenshots, logged keystrokes and spied on people through their webcams.
Intel says it will patch 90 percent of recent chips by next week (updated)
A little more than a day since Google Project Zero went public with its findings regarding a major security flaw in Intel (and others) chip designs, the company announced that it is already is pushing out patches to eliminate the vulnerability. Intel has "already issued updates for the majority of processor products introduced within the past five years," per the company press release, and expects to have 90 percent of affected chips produced within the past five years patched by the end of the week.







