DefCon
Latest
2018 in cybersecurity: Regrets, we have a few
This was the year security slips, privacy fails and outright stupidity went from bad to surreal. It was a year in which warnings went unheeded and companies lost whatever trust we gave them. It was a nesting doll of security disasters. A clown car of willful negligence. A long 12 months of totally unsexy, nonconsensual edge-play with our data.

Voting machines are still plagued with vulnerabilities as midterms loom
The Def Con Voting Village, which for two years in a row has let conference attendees try their hand at breaching voting machines, has released the report on this year's event. More than 30 voting machines and other pieces of election equipment were available this year and many of them are still used throughout the US. Troublingly, attendees uncovered multiple vulnerabilities, the number and severity of which the report described as "staggering." "What these vulnerabilities in this report and warnings from national security leaders tell us is that this is a severe national security threat," said Voting Village co-organizer Jake Braun.

New lawsuit shows your phone is unsafe at American borders
A recent case filed in federal court, in which an American woman had her iPhone seized and cracked by Customs and Border Protection in a New Jersey airport puts a whole new spin on the things we now need to worry about when leaving the country. It appears that now everyone's phones, despite country of origin or cause, are subject to nonconsensual seizure and search -- even if we refuse to give up our passwords. If you're not caught up on the story, news hit this week that a Staten Island mom coming home from a February trip with her 9-year-old daughter from Switzerland had her iPhone snatched, kept for months and accessed for no given reason. Apple did not respond to a request for comment by publication time.

This cute Def Con badge beckons you to hack it
At previous Def Cons I wrote about the unofficial badges and the culture surrounding those pieces of technology. This year I was determined to move past my infatuation with blinking lights and colorful PCBs (printed circuit boards). Then I saw the Maneki Neko badge. It's the iconic beckoning cat (literally what "maneki-neko" means) with a moving 3D-printed arm and two 16-segment LEDs that blink at you while it waves.

Dozens of kids hack election site replicas in just minutes
The Def Con hacker conference has been demonstrating how vulnerable voting machines are to hacks through its Voting Village, wherein adults are given the chance to compromise various models of voting devices. But this year, Def Con also let kids get in on the game, opening up replicas of states' election websites to children aged eight to 16. The event, put on by r00tz Asylum and supported by the University of Chicago and the Democratic National Committee, showed just how vulnerable these sites are to attack.

Security flaws could open body cameras up to hacks
At Def Con this weekend, Josh Mitchell, a cybersecurity consultant with Nuix, showed how various models of body cameras can be hacked, tracked and manipulated. Mitchell looked at devices produced by five companies -- Vievu, Patrol Eyes, Fire Cam, Digital Ally and CeeSc -- and found that they all had major security flaws, Wired reports. In four of the models, the flaws could allow an attacker to download footage, edit it and upload it again without evidence of any of those changes having occurred.

Android exploit targeted apps' shoddy use of external storage
Many mobile security flaws revolve around obvious avenues like websites or deep, operating system-level exploits. The security team at Check Point, however, has discovered another path: apps that make poor use of external storage like SD cards. While apps would ideally stick to internal storage (which Google sandboxes against outside influence) as much as possible, some apps have relied unnecessarily on unprotected external storage and didn't bother to validate the data coming from that space. An intruder could take advantage of that poor security policy to manipulate the data and cause havoc -- Check Point called it a "man-in-the-disk" attack.

Elaborate hack turned Amazon Echo speakers into spies
Some people worry that hackers could infiltrate their smart speakers and spy on them, but that hasn't been the practical reality -- not for Amazon's Echo, at least. A team of researchers from China's Tencent has come about as close as you can get right now, however. They've disclosed an attack on the Echo that uses both a modified speaker and a string of Alexa web interface vulnerabilities to remotely eavesdrop on regular models. It sounds nefarious, but it requires more steps than would be viable for most intruders.

Machine learning can 'fingerprint' programmers
Programmers tend to have their own distinct styles, but it's not really feasible to pore over many lines of code looking for telltale cues about a program's author. Now, that might not be necessary. Researchers have developed a machine learning system that can 'de-anonymize' programmers, whether it's through raw source code or compiled binaries. As explained to Wired, the approach trains an algorithm to recognize a programmer's coding structure based on examples of their work, and uses those to pinpoint common traits in code samples. You don't need large chunks of a given program, either -- short snippets are often enough.
When your Uber driver is a spy
Like other migrating beasts, hackers travel huge distances for feeding, breeding, and breaking things every summer -- at Defcon in Las Vegas. The way they move about the city is driven primarily by the availability of free booze at corporate parties or the convenience of air-conditioned infosec habitats; the heat makes them torpid. As such, everyone takes taxis, Ubers, and Lyfts everywhere, day and night.

DNC-led Def Con event tests election websites against child hackers
At the Def Con hacker conference next week, the Democratic National Committee is co-sponsoring a contest that will pit child hackers against replicas of state government websites, Wired reports. Kids between the ages of eight and 16 will try to break into replicas of the websites secretaries of state use to post election results, and the one that devises the best defensive strategy will win $500 from the DNC. Another $2,000 will be awarded to whoever can penetrate a site's defenses. The University of Chicago and a non-profit called r00tz Asylum that offers cybersecurity lessons for children are also sponsoring the event.

When China hoards its hackers everyone loses
They say you don't notice something good until it's gone. With China's decision to restrict its information security researchers from participating in global hacking competitions, we're about to see what that looks like on the global "zero day" stage.
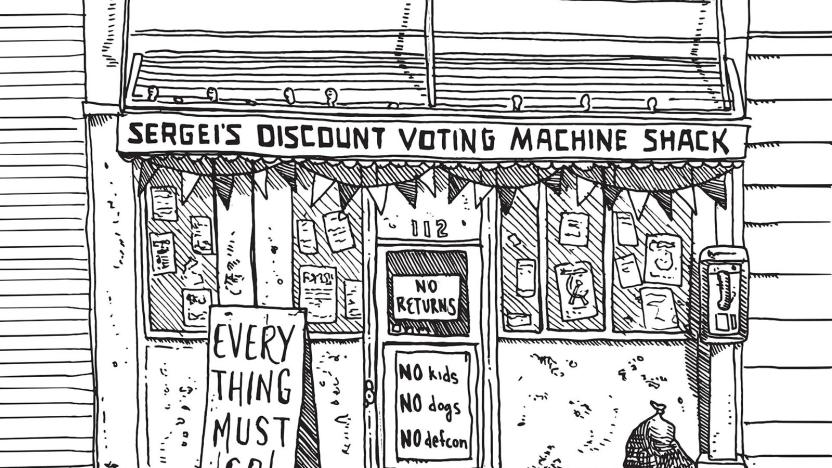
Voting-machine makers are already worried about Defcon
Last year, Defcon's Voting Village made headlines for uncovering massive security issues in America's electronic voting machines. Unsurprisingly, voting-machine makers are working to prevent a repeat performance at this year's show. According to Voting Village organizers, they're having a tough time getting their hands on machines for white-hat hackers to test at the next Defcon event in Las Vegas (held in August). That's because voting-machine makers are scrambling to get the machines off eBay and keep them out of the hands of the "good guy" hackers.

DefCon event shows how easy it is to hack voting systems
It's no secret that it's possible to hack voting systems. But how easy is it, really? Entirely too easy, if you ask researchers at this year's DefCon. They've posted a report detailing how voting machines from numerous vendors held up at the security conference, and... it's not good. Every device in DefCon's "Voting Machine Hacking Village" was compromised in some way, whether it was by exploiting network vulnerabilities or simple physical access.

Your timely reminder: Not all hacking requires a computer
The public perception of hacking involves a shadowy figure in a hoodie hunched over a laptop, tapping furiously while a waterfall of glowing green text fills the screen. Also he's probably listening to industrial music. First off, that's a ridiculous caricature, and more important, not all intrusions are the result of someone banging away on a keyboard to "hack the network." Exploiting the vulnerabilities of a company can simply involve picking up a phone, chatting with a few people or memorizing a few tones.

FBI arrests UK security researcher who stopped WannaCry outbreak (updated)
Marcus Hutchins, the 23-year-old security researcher who is credited with halting the spread of the WannaCry malware program earlier this year has been arrested by the FBI while attending the Def Con security conference in Las Vegas, Motherboard reports.
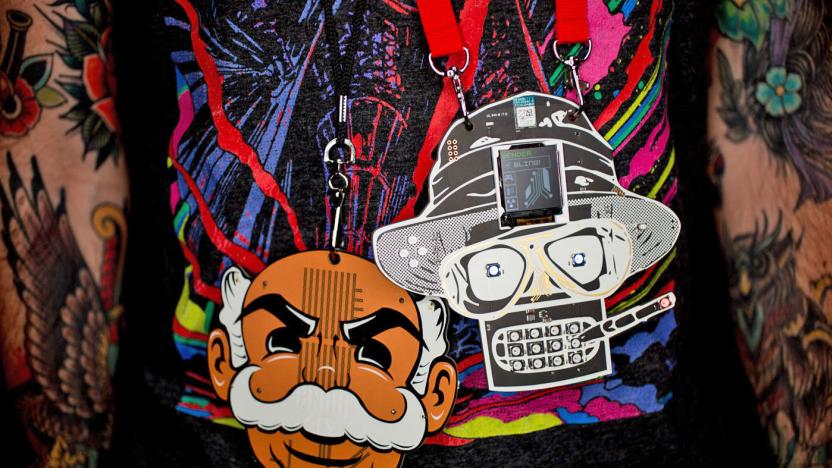
The exquisite art and subculture of Def Con’s (unofficial) badges
A series of tweets sent me and other Def Con attendees scrambling to get to the Caesers Palace pool as quickly as possible. I cut short a conversation, shoved my gear in my bag and ran out of the press room without an explanation. I was after a piece of art. A piece of tech. But mostly I was excited about adding to my growing collection. I was on the hunt for Puffy, one of dozens of unofficial Def Con badges available for sale at the annual hacker conference from build-teams from all over the world. It's a piece of electronics shaped like a fish, and I decided I must have it.
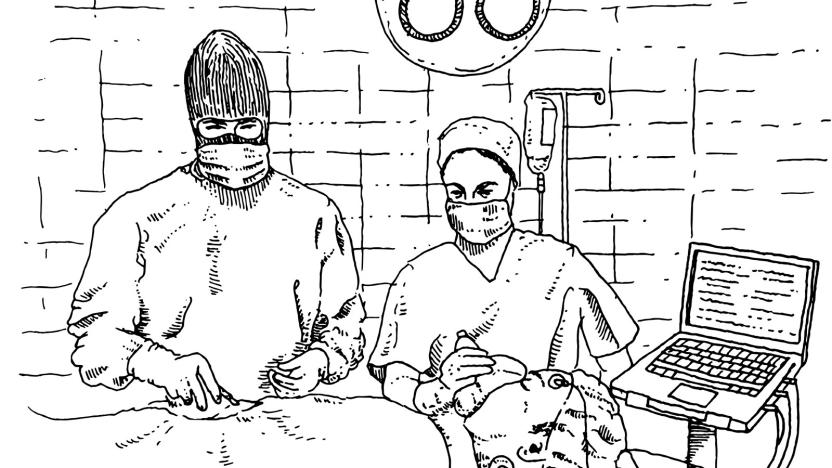
Now doctors need to be hackers, too
As far as anyone knows, there hasn't been a real-life hack attack on someone's pacemaker. Which is surprising. Security researchers have shown us that it's a very real possibility. Even the FTC has been urging connected-medical-device makers to adopt security best practices, with multiple 2017 reports stressing the issue.

Rudy Giuliani will advise Trump on cybersecurity
During an appearance on Thursday's Fox & Friends talk show, former NYC mayor Rudy Giuliani announced that he would be forming a cybersecurity team for President-elect Trump. According to the Trump Transition's official announcement, the team would advise the President-elect on issues "concerning private sector cyber security problems and emerging solutions developing in the private sector." Presumably, this will entail more than simply writing things down on paper and having them delivered by courier.

The incredibly intricate badges of Def Con
Three days before the 24th annual Def Con hacker event, badge designer and builder 1o57 (aka Ryan Clarke) had a problem. "The lion's share of the 20,000 badges showed up this year not programmed," he told Engadget. He gathered up a team and they went into "hell mode" to hand-program blinking pieces of electronic riddled with cryptographic puzzles.




