nsa
Latest

Snowden: We rely too much on Facebook for news
Facebook has been under fire this past week for supposedly influencing the election by not doing enough to stop the rise of fake news. In an interview at the Real Future Fair conference, NSA whistleblower Edward Snowden said that while this is certainly an issue, the real problem here is that Facebook is where most people get their news. "This gets into a bigger challenge, which is lack of competition," he said. "This is a danger of a single point of failure."
The consequences of the Trump presidency on cybersecurity
Hacking and cybersecurity played a huge role in the presidential election. So much so that Donald Trump, America's new president-elect, was helped greatly by the acts of criminal hackers in his journey to the White House, and is now an outspoken WikiLeaks fan.

Edward Snowden will discuss Trump and privacy on November 10th
American technology policies could change significantly under Donald Trump, and that includes its stance on privacy. How will the new leader alter government surveillance, for example? Edward Snowden might have an answer. The whistleblower and Dutch search engine StartPage are hosting a live event on November 10th at 4:30PM Eastern to address what happens to privacy in the Trump era, among other questions. Snowden speaking engagements are nothing new, but this is special -- he's more than a little familiar with government spying activities, and this is his first chance to opine on how things might be different under a new administration.

AT&T reportedly spies on its customers for government cash
AT&T controls a big chunk of America's cellular infrastructure, and it turns out that it's been using that power for super-creepy purposes. The Daily Beast is reporting that the telco has essentially turned itself into a spy-for-hire in the pay of the government. According to the piece, the company's Project Hemisphere is providing warrantless surveillance, thanks to some legal gray areas, that score it millions of dollars from taxpayers.

NSA's hacking tools found among data stolen by contractor
The feds quietly arrested NSA contractor Harold Thomas Martin III back in August for stealing an enormous number of documents from the agency. Now, the investigators sifting through the documents found in his computers discovered what they were probably looking for from the start. According to the New York Times, the documents he stole included the NSA's top secret hacking tools posted online by a group called Shadow Brokers earlier this year. Federal agents had to pore over terabytes upon terabytes of data to find those tools, since the classified materials found in Martin's possession make the Panama Papers (2.6 terabytes) and Edward Snowden's documents look insignificant in comparison.

Reuters: Yahoo email scanning done with a Linux kernel module
In the ever evolving saga of Yahoo's email servers and who could peek into them, the latest nugget comes from a Reuters report that the scanning program operated at a deeper level than mail filters for porn or spam. Citing three former employees, it now says the scanning was done via a module attached to the Linux kernel itself. While the more technically-minded wondered why this method would've been employed at all, others like Senator Ron Wyden called for the government to release the FISA order apparently ordering the surveillance.

NYT: Yahoo reworked its malware scanner for email surveillance
Following a Reuters report that in 2015 Yahoo scanned customer emails for US surveillance, the New York Times has followed up with details from anonymous sources of its own. Although Yahoo responded a day later claiming the initial report was "misleading," the NYT sourced unnamed government officials claiming the company modified a system used to scan all incoming email for malware that stored matching messages and made them available to the FBI.

NSA contractor arrested for allegedly stealing secrets
The New York Times reports that the FBI quietly arrested and charged an NSA contractor in late August on suspicion of stealing, and potentially disclosing computer code relating to an offensive hacking program designed to break into the network systems of adversarial foreign governments like Russia, China, Iran and North Korea.

ICYMI: The selfie-obsessed can verify online ID with photos
try{document.getElementById("aol-cms-player-1").style.display="none";}catch(e){}Today on In Case You Missed It: Mastercard is introducing a way to verify online purchases, by sending a link to the user's cell phone, which then walks them through taking a selfie and blinking on command to show they're a real human. Meanwhile Google unleashed a slew of new products at its Developer's Conference in San Francisco, here's the full scoop on the new phone. Toyota's cute little robot is available only in Japan but sure is darling, the video is here. As always, please share any interesting tech or science videos you find by using the #ICYMI hashtag on Twitter for @mskerryd.

Yahoo reportedly gave US government access to all users' emails (updated)
According to Reuters, Yahoo provided US intelligence officials access to all of its customers incoming emails last year. The publication's sources claim that the company had to comply with a classified request from the government, which allowed the National Security Agency and FBI to scan "hundreds of millions" of Yahoo Mail accounts.

NSA operative might have accidentally leaked its hacking tools
American authorities are still digging into how a set of NSA's hacking tools landed in the hands of a group called Shadow Brokers who then leaked them online. According to Reuters, they're now focusing their investigation on a theory that one NSA operative used the tools on a remote computer three years ago. They believe the operative left them there exposed, and that's where Russian hackers got a hold of them. The exploits allow users to take advantage of security systems' software flaws. They can target a number of companies' products in particular, including Cisco's firewalls and routers, putting their customers at risk.

'Snowden' is a simplistic, but important, reminder of NSA spying
When Oliver Stone's Snowden was first announced, it seemed far too soon to be retelling the story of the infamous whistleblower. After all, it was only three years ago that the files Snowden leaked led to the world-shaking revelations of the NSA's massive global surveillance network. That's not nearly enough time for us to make any sort of substantive historical analysis.

House committee: Snowden is a 'serial exaggerator and fabricator'
The US House of Representatives' intelligence committee just releasing a statement condemning Edward Snowden and recommending he be extradited to face justice. After two years spent reviewing the 1.5 million documents Snowden stole and interviewing experts, the committee report rejects his whistleblower claims and attempts to poke enough holes in his story to portray him as a dangerous liar. Obviously, the government has an incentive to downplay his leak's accomplishments and hammer home their threat to the country, but with the ACLU and Amnesty International calling on President Obama to pardon Snowden, it's critical to look past the static of competing narratives.
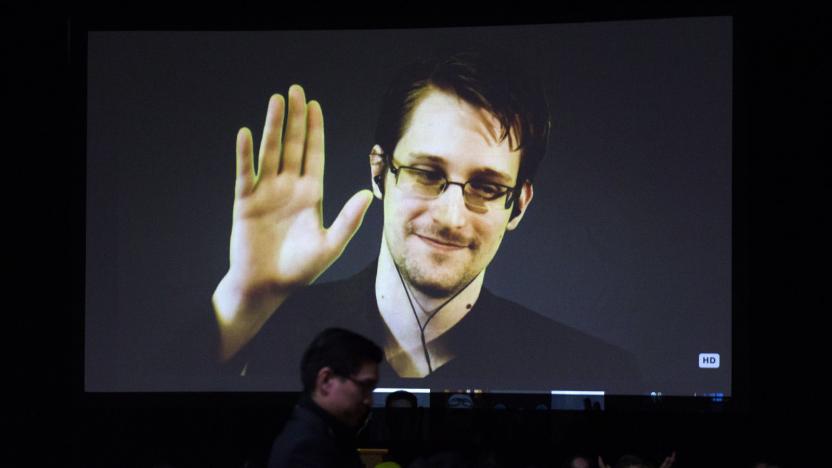
Edward Snowden explains why Obama should pardon him
Edward Snowden laid out the reasons he should receive a pardon from President Obama in an interview with the Guardian, saying that while his actions as a whistleblower were technically illegal, they benefited citizens of the United States. "I think when people look at the calculations of benefit, it is clear that in the wake of 2013 the laws of our nation changed," Snowden told the Guardian. "The Congress, the courts and the president all changed their policies as a result of these disclosures. At the same time there has never been any public evidence that any individual came to harm as a result."

ACLU and Amnesty International ask Obama to pardon Snowden
The American Civil Liberties Union and Amnesty International, two of the highest-profile human rights organizations in the United States, are calling for President Obama to grant clemency to Edward Snowden. The "Pardon Snowden" campaign kicks off today with a petition to "let President Obama know that the American people stand with Snowden." It's seeking 60,000 signatures and is hosted by the ACLU, which has signed on as Snowden's legal adviser.

New Snowden leaks unravel mystery behind NSA's UK base
Just when you thought you couldn't be shocked by the NSA's snooping anymore, new leaked documents show the agency's reach extends far beyond American borders. According to files obtained by The Intercept from NSA whistleblower Edward Snowden, a US base in the UK has been eavesdropping on satellite and other wireless communications around the world.

Watch Snowden talk 'Snowden' with Oliver Stone next month
NSA whistleblower Edward Snowden's telepresence world tour has another stop: a conversation following an early screening of the upcoming Oliver Stone biopic, Snowden. The Oscar-winning director will also be a part of the fireside chat, but rather than beaming in from Moscow, according to Deadline he'll be joining from New York. That, in a nutshell, is the difference between being wanted by the federal government and making a movie about someone wanted by the federal government.

Untangling the NSA's latest alleged embarrassment
Last week, security researcher Mikko Hypponen found a notice on Github from an entity called Shadow Brokers, a reference to master of the galactic black market for information in the game Mass Effect. The notice was for an auction of exploits from the Equation Group (widely believed to be operated by the NSA).

Here's how the NSA spied on Cisco firewalls for years
Edward Snowden leaks revealed that the NSA had the ability to spy on Cisco firewall traffic for years, but just how did the agency do it? We now have a clearer idea. An analysis of data from the Equation Group hack shows that the NSA used a specialized tool, BenignCertain, that uses an exploit in Cisco's Internet Key Exchange implementation to extract encryption keys and read otherwise secure virtual private network data. Cisco has confirmed that the attack can compromise multiple versions of its old PIX firewalls, which were last supported in 2009.

New Snowden docs suggest Shadow Broker leak was real
On Monday, a group of hackers calling themselves the Shadow Broker put up a number of cyber-espionage tools reportedly stolen from NSA-associated hacking outfit, the Equation Group. Edward Snowden has already publicly speculated that the intrusion and theft was actually just another salvo in the ongoing Digital Cold War happening between the US and Russia. However, nobody was 100 percent certain that the tools for sale really were NSA property. Now, Snowden has released documentation to The Intercept that suggests the tools really are what the Shadow Brokers say they are.













